はじめに
SaaSプラットフォームや多要素認証(MFA)サービスの普及を利用して、悪意あるアクターが組織のネットワークに不正にアクセスすることが後を絶たない中、アカウントの侵害を早い段階で防ぐために適切なセキュリティツールを導入することが極めて重要となっています。
攻撃者が頻繁に使用する手法の1つに、アカウントの乗っ取りがあります。アカウントの乗っ取りは、脅威アクターが認証情報を悪用してSaaSアカウントにログインする際に発生します。多くの場合、本物の攻撃者は通常ログインしないような珍しい場所からログインします。
これらのアカウントへのアクセスは、フィッシングメールやパスワードスプレー攻撃によって認証情報を採取したり、ユーザーアカウントでMFAを有効にせず、認証にユーザー認証情報のみを必要とするなど、安全でないクラウド防御対策を悪用することで引き起こされます。アカウントの完全性が侵害されると、脅威アクターはマルウェアの配信、機密データの読み取りと流出、さらに社内外のユーザー認証情報を採取するためのフィッシングメールの送信など、さらなる活動を行い、攻撃サイクルを繰り返すことができます [1,2]。
2023年初頭、 Darktraceは、教育分野の顧客のネットワーク上で大規模なアカウント乗っ取りとフィッシング攻撃を検知し、数百のアカウントに影響を与え、数千のEメールがネットワーク外に転送される結果となりました。Darktrace DETECT™が提供する極めて高い可視性により、キルチェーンのあらゆる段階で敵対的な活動を検知することができました。Ask the Expert(ATE)サービスを通じてDarktrace Analystチームから直接サポートを受けることにより、顧客は十分に情報を得て改善策を実施できるようになりました。
一連の攻撃の詳細
Darktrace はその結果、お客様のネットワーク上で乗っ取られた全てのアカウントで、見知らぬ場所からのログイン、すべての受信メールを悪意のあるEメールアドレスに転送するというメール転送ルールの有効化、フィッシングメールの送信とその削除という同じパターンの活動を確認しました。

初期アクセス
Darktrace DETECTは、2023年1月14日に顧客環境上の異常なSaaSアクティビティを最初に検知し、その後2月3日にも、複数のSaaSアカウントが、珍しいIPアドレスと地理的に不可能な移動タイミングを持つ非定型の場所からログインしていること、またはアカウント所有者が他の場所で活動している間にログインしていることが観察されました。オープンソースインテリジェンス(OSINT)ソースを使用したその後の調査で、IPアドレスの1つが最近ブルートフォースまたはパスワードスプレーの試みに関連していたことが判明しました。
このような異常なログインのパターンは、攻撃の期間中ずっと続き、毎日、より多くのユニークなアカウントが同様の異常なログインでモデルブリーチを発生させました。これらのユーザーのログインにはMFA認証が適用されなかったため、認証に認証情報のみを必要とすることで、最初の侵入プロセスが可能になりました。
Eメールを送信する
また、侵害されたアカウントは、「Email HELP DESK」という件名のメールを外部および内部の受信者に送信していることが確認されました。これは、脅威者が社内のヘルプデスクを装って受信者の信頼を得るためにソーシャルエンジニアリング戦術を採用したものと思われます。
Eメールを転送する
ログインに成功した後、侵害されたアカウントは、外部のEメールアドレスにEメールを転送するためのEメールルールを作成し始め、そのうちのいくつかは、OSINTソースによると悪意のある活動のためのドメインに関連していたことが判明しました [3]。
- chotunai[.]com
- bymercy[.]com
- breazeim[.]com
- brandoza[.]com
Eメールの転送は、SaaSの侵害行為において、通信回線を制御するためによく見られる手口です。悪意のある脅威アクターは、機密情報の流出、侵害されたEメールへの持続的なアクセスの獲得、請求書支払いのリダイレクトなど、不正な目的のために進行中の通信に介入しようとすることがよくあります。
Eメールを削除する
Eメール転送の直後、感染したアカウントが一斉に異常なEメールを削除したことが検知されました。さらに調査を進めると、これらのアカウントは以前に大量のフィッシングメールを送信しており、この大量削除は、送信トレイから削除することでこれらの活動を隠そうとしたものと思われます。
2月10日、この顧客はDarktrace が侵害されたと特定したすべてのアカウントにパスワードの一括リセットを適用し、MFAを備えた特権アカウントのプロビジョニングを行いました。これらの対策により、最初の侵入経路に対処し、侵害を食い止めることに成功したと発表しています。
Darktrace のカバレッジ
Darktrace は、自己学習型AIを駆使して、アカウントが悪意のあるアクターに乗っ取られたことを示す可能性のある異常なSaaSアクティビティを検知する能力を効果的に実証しました。従来のルールやシグネチャベースのアプローチに頼るのではなく、Darktrace のモデルはネットワーク自体の理解を深め、危険なものが予想される生活パターンから逸脱した場合に瞬時に認識することができます。

初期アクセス
初期アクセスは以下のモデルで検知されました:
- Security Integration / High Severity Integration Detection
- SaaS / Unusual Activity / Activity from Multiple Unusual IPs
- SaaS / Access / Unusual External Source for SaaS Credential Use
- SaaS / Compromise / Login From Rare Endpoint While User Is Active
初期アクセスは、以下のCyber AI Analyst インシデントでも検知されました:
- Possible Hijack of Office365 Account
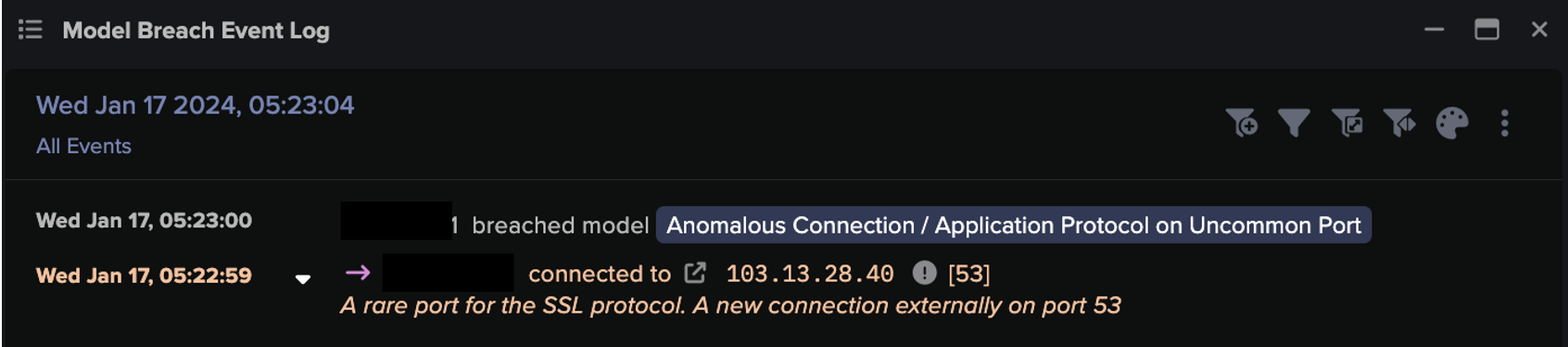
モデルブリーチとAI Analystのインシデントでは、図3に描かれているように、MFAの使用不足と合わせて、100%レアな外部IPアドレスからのログインが検知されました。


Eメールを転送する
Eメール転送は、以下のモデルで検知されました:
- SaaS / Admin / Mail Forwarding Enabled
攻撃されたアカウントの多くは、外部Eメールアドレスへのメール転送ルールを設定しており、表向きは、ネットワーク上での永続性を確立し、機密性が高い通信を流出させるために検知されました。

大量のEメール削除
大量のEメール削除は、以下のモデルで検知されました:
- SaaS / Compromise / Suspicious Login and Mass Email Deletes
- SaaS / Resource / Mass Email Deletes from Rare Location

Darktraceは、稀な場所から非常に異常な大量メール削除を行うアカウントを検知しました。この攻撃者は、「Email HELP DESK」というメールを削除しており、後にこの攻撃で使用された主要なフィッシングメールであることが確認されました。削除は侵害されたアカウントの送信トレイで観察され、おそらく悪意のある活動を隠すために行われたものと思われます。
Darktraceは、この連動した活動のパターンを、以下のようなシーケンシャルなモデルでも検知しました:
- SaaS / Compromise / Unusual Login, Sent Mail, Deleted Sent
- SaaS / Compromise / Suspicious Login and Mass Email Deletes
Ask the Expert
お客様は、ATE(Ask The Expert)サービスを利用して、攻撃に関するより多くの技術的な情報とサポートを要求しました。Darktraceの24時間365日体制のアナリストチームは、専門的な支援とさらなる詳細を提供し、その後の調査や修復のステップを支援することができました。
さらなる検知と遮断
残念ながら、このお客様は攻撃時にDarktrace/Email™を有効にしていませんでした。Darktrace/Emailは、インバウンドおよびアウトバウンドのメールフローを可視化することで、潜在的なデータ損失インシデントを監視することができます。この場合、Darktrace DETECT/Emailは、侵害されたアカウントから送信されたフィッシングメールや、攻撃者が社内のヘルプデスクになりすまそうとした試みを完全に可視化することができたと思われます。さらに、新たにAnalysis Outlookとの統合により、従業員はメールが疑わしい理由を理解し、セキュリティチームに直接メールを報告できるようになり、フィッシング攻撃に対するユーザーの意識を継続的に高めることができます。
Darktrace/Emailは、Darktrace/Network™の検知を強化します。Darktrace/Network内の「Email Nexus」モデルをトリガーとして、デジタル資産全体で悪意のある活動を検知し、SaaSの不正ログインから不正ユーザーによって送信された大量のスパムメールまでを関連付けます。

Darktrace RESPOND™ は攻撃時に顧客環境で有効になっていませんでした。もし有効になっていれば、Darktraceはキルチェーンの複数にわたって検知されたSaaSモデルの侵害に対して自律的に行動を起こすことができたはずです。RESPONDは、乗っ取られたアカウントを無効にするか、一定期間強制的にログアウトさせ、悪意のある行為者によって確立された受信トレイのルールも無効にすることができたでしょう。これにより、顧客のセキュリティチームは、インシデントを分析し、状況を緩和するための貴重な時間を得ることができ、攻撃がこれ以上拡大することを防ぐことができました。
結論
最終的に、Darktraceは、この大規模な標的型SaaSアカウントの乗っ取りとその後のフィッシング攻撃を検知することができた顧客ネットワーク上の比類のない可視性を示しました。これは、深層防御の重要性を強調するもので、決定的に重要なのは、この環境ではMFAが実施されていなかったため、標的となった組織がクレデンシャルの盗難による危険にさらされる可能性が高かったことです。また、このアカウント侵害の後にDarktraceが検知したフィッシング活動は、あらゆるセキュリティスタックにおけるEメール保護の必要性を強調しています。
Darktraceの可視性により、アカウントのログイン、メール転送ルールの作成、送信メール、フィッシングメールの大量削除など、高度な粒度で攻撃を自律検知することができました。Darktraceの異常検知は、新たな脅威を特定する際に、シグネチャやルール、既知の侵害指標(IoC)に頼る必要がなく、代わりにユーザーの通常の行動からの逸脱を認識することに重点を置いていることを意味します。
しかし、進行中の攻撃に即座に介入して停止させることができる自律的な遮断技術が存在しなければ、組織は常に被害が発生した後に攻撃に対処することになります。Darktrace RESPONDは、疑わしい活動を検知するとすぐに対策を講じ、攻撃が拡大するのを防ぎ、お客様のビジネスに大きな支障をきたさないようにするためのユニークな存在です。
Credit to: Zoe Tilsiter, Cyber Analyst, Gernice Lee, Cyber Analyst.
付録
モデルブリーチ
SaaS / Access / Unusual External Source for SaaS Credential Use
SaaS / Admin / Mail Forwarding Enabled
SaaS / Compliance / Microsoft Cloud App Security Alert Detected
SaaS / Compromise / SaaS Anomaly Following Anomalous Login
SaaS / Compromise / Unusual Login, Sent Mail, Deleted Sent
SaaS / Compromise / Suspicious Login and Mass Email Deletes
SaaS / Resource / Mass Email Deletes from Rare Location
SaaS / Unusual Activity / Multiple Unusual External Sources For SaaS Credential
SaaS / Unusual Activity / Activity from Multiple Unusual IPs
SaaS / Unusual Activity / Multiple Unusual SaaS Activities
Security Integration / Low Severity Integration Detection
Security Integration / High Severity Integration Detection
IoC一覧
brandoza[.]com - domain - probable domain of forwarded email address
breazeim[.]com - domain - probable domain of forwarded email address
bymercy[.]com - domain - probable domain of forwarded email address
chotunai[.]com - domain - probable domain of forwarded email address
MITRE ATT&CK マッピング
Tactic: INITIAL ACCESS, PERSISTENCE, PRIVILEGE ESCILATION, DEFENSE EVASION
Technique: T1078.004 – Cloud Accounts
Tactic: COLLECTION
Technique: T1114- Email Collection
Tactic:COLLECTION
Technique: T1114.003- Email Forwarding Rule
Tactic: IMPACT
Technique: T1485 - Data Destruction
Tactic: DEFENSE EVASION
Technique: T1578.003 – Delete Cloud Instance
参考文献
[1] Darktrace, 2022, Cloud Application Security_ Protect your SaaS with Self-Learning AI.pdf
[2] https://www.cloudflare.com/en-gb/learning/access-management/account-takeover/