日々変化する脅威の中で、新たな戦術、技術、手順(TTP)が日々出現しており、セキュリティチームにとって非常に大きな課題となっています。攻撃者が利用する攻撃手法は多岐にわたるため、「まだ存在しないプレイブックをどのように防御するか」という克服不可能な問題が生じているように思われます。
Faced with the growing number of novel and uncommon attack methods, it is essential for organizations to adopt a security solution able to detect threats based on their anomalies, rather than relying on threat intelligence alone.
In March 2023, Darktrace observed an emerging trend in the use of an application known as ‘PerfectData Software’ for probable malicious purposes in several Microsoft 365 account takeovers.
Darktrace DETECT™は、アノマリーベースの検知機能により、このアプリケーションを使用する際のアクティビティチェーンを特定することができ、その過程で脅威アクターによる新しい技巧を発見する可能性があります。
Microsoft 365の不正侵入
In recent years, Microsoft’s Software-as-a-Service (SaaS) suite, Microsoft 365, along with its built-in identity and access management (IAM) service, Azure Active Directory (Azure AD), have been heavily targeted by threat actors due to their near-ubiquitous usage across industries. Four out of every five Fortune 500 companies, for example, use Microsoft 365 services [1].
Malicious actors typically gain entry to organizations’ Microsoft 365 environments by abusing either stolen account credentials or stolen session cookies [2]. Once inside, actors can access sensitive data within mailboxes or SharePoint repositories, and send out emails or Teams messages. This activity can often result in serious financial harm, especially in cases where the malicious actor’s end-goal is to elicit fraudulent transactions.
DarktraceはMicrosoft 365環境にアクセスした悪意ある行為者が、予測可能な方法で行動することを定期的に観察しています。典型的な例としては、新しい受信トレイのルールを作成し、悪意のあるリンクをたどったり、機密情報を提供したりといった後続のアクションを実行するよう受信者を説得することを目的とした詐欺的なメールを送信することが挙げられます。また、行為者が新しいアプリケーションをAzure ADに登録し、マスメールやデータ窃盗などのフォローアップ活動に使用できるようにすることも一般的です。したがって、Azure ADへのアプリケーションの登録は、比較的予測可能な脅威行為と思われます[3][4]。Darktrace DETECT は、Azure ADにおける異常なアプリケーション登録が、期待される行動からの逸脱を構成し、したがってアカウント侵害の可能性を示す指標となり得ることを理解します。
これらのAzure ADにおけるアプリケーションの登録は、Azure ADにおけるサービスプリンシパルの作成および権限の割り当てによって証明されます。Darktraceは脅威アクターがPerfectData Softwareという名前のサービスプリンシパルに権限を作成および割り当てる傾向が高まっていることを検知しています。このAzure ADの活動をさらに調査したところ、進行中のアカウント乗っ取りの一部であることが判明しました。
PerfectData Software の活動
Darktrace は、PerfectData Software という名前のアプリケーションに関する次のような活動パターンのバリエーションを顧客基盤において観察しました:
- 脅威アクターは、仮想専用サーバー(VPS)または仮想専用ネットワーク(VPN)サービスに関連するエンドポイントから、Microsoft 365アカウントにサインインします。
- 脅威アクターは、PerfectData SoftwareというアプリケーションをAzure ADに登録し、アプリケーションにアクセス権を付与します。
- 脅威アクターがEメールボックスデータにアクセスし、受信ルールを作成する。
2つの別々のインシデントにおいて、悪意のあるアクターは、VPNサービス(それぞれHideMyAss (HMA) VPNとSurfshark VPN)に関連するエンドポイントから、および自律システムAS396073 MAJESTIC-HOSTING-01 内のエンドポイントから活動を行うことが確認されました。
2023年3月、Darktraceは自律防御システム内でクウェートベースのIPアドレス、AS198605 AVAST Software s.r.o. からMicrosoft 365アカウントにサインインする悪意のあるアクターを確認しました。このIPアドレスはVPNサービス、HMA VPNと関連しています。その後数日間、あるアクター(おそらく同じ悪意あるアクター)が、ナイジェリアベースの2つの異なるエンドポイント、VPS関連のエンドポイント、HMA VPNのエンドポイントから、さらに数回アカウントにサインインしています。
ログインセッション中、アクターは様々なアクションを実行しました。まず、PerfectData Softwareという名前のサービスプリンシパルを作成し、権限を割り当てました。このサービスプリンシパルの作成は、Azure ADにPerfectData Softwareというアプリケーションを登録したことを意味します。 このアプリケーションを登録した理由は不明ですが、数日以内に、行為者は別のアプリケーションであるNewsletter Software Supermailerを登録して許可を与え、乗っ取られたアカウントのメールボックスに新しい受信トレイルール名 's' を作成しました。この受信箱ルールは、特定の条件を満たしたメールをRSS Subscriptionという名前のフォルダに移動させる。このNewsletter Software Supermailerアプリケーションは、大量送信を容易にするために行為者が登録したものと思われます。
これらの行為の直後、Darktraceはこの脅威アクターがこのアカウントから数千通の悪意のあるメールを送信していることを検知しました。このメールには、Credit Transfer Copy.htmlという名前の添付ファイルが含まれており、この中には不審なリンクが含まれていました。さらに調査を進めると、この最初の侵入行為の前に、顧客のネットワークが偽の請求書メールを数回受信していたことが判明しました。さらに、最初のアクセス時に、侵害されたアカウントへのログイン失敗が異常に多く発生していたことも判明しました。

2023年3月にDarktrace が観測した別のケースでは、悪意のあるアクターが、自律防御システムAS397086 LAYER-HOST-HOUSTON内のエンドポイントからMicrosoft 365アカウントにサインインしていることが観測されています。このエンドポイントは、VPNサービスであるSurfshark VPNに関連しているようです。このログインに続いて、自律防御システムAS396073 MAJESTIC-HOSTING-01内のVPS関連からのログインが何度か失敗したり成功したりしました。その後、PerfectData Softwareと呼ばれるアプリケーションを登録し、権限を付与していることが確認されました。前例と同様、この登録の動機は不明である。このアクターは、Surfshark VPNエンドポイントからさらに数回ログインを繰り返しましたが、それ以上の不審な行為を行う様子は確認されていません。

これらの例でも、また、Darktrace が観察したどの例でも、脅威アクターが PerfectData Software と呼ばれるアプリケーションを登録し、許可を与えた理由は明らかではありませんでした。また、この名前のアプリケーションの悪意のある使用に関するオープンソースインテリジェンス(OSINT)リソースやオンライン文献は存在しないようです。とはいえ、PerfectData Software という名称のEメール移行ツールやデータ復旧およびバックアップツールを提供していると思われるウェブサイトはいくつか存在するようです。
Darktrace の顧客のネットワーク上で観察された悪意のあるアクターによるPerfectData Softwareの使用が、これらのツールの1つであったかどうかは不明であります。しかし、ツールの性質を考えると、悪意のあるアクターは、侵害されたEメールボックスからのEメールデータの流出を促進するために、ツールを使用することを意図していた可能性があります。
If the legitimate software ‘PerfectData’ is the application in question in these incidents, it is likely being purchased and misused by attackers for malicious purposes. It is also possible the application referenced in the incidents is a spoof of the legitimate ‘PerfectData’ software designed to masquerade a malicious application as legitimate.
Darktrace のカバレッジ
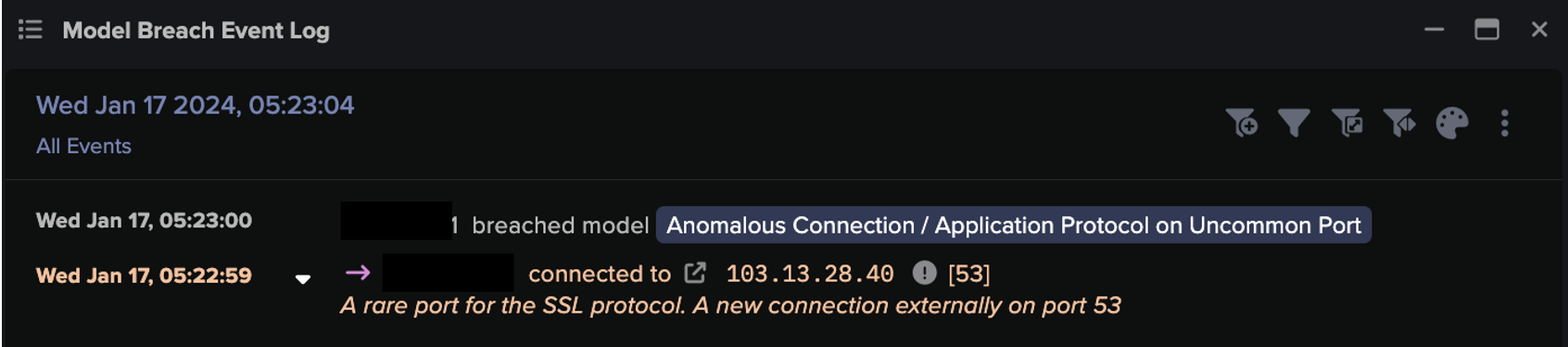
Darktrace によって検知された PerfectData Software アクティビティチェーンのケースは、通常、VPNまたはVPS関連のエンドポイントから内部ユーザーのMicrosoft 365アカウントにサインインする行為から始まります。これらのログインイベントは、それに先立つ不審なEメールやブルートフォースアクティビティとともに、以下のDETECT モデルが侵入する原因となりました:
- SaaS / Access / Unusual External Source for SaaS Credential Use
- SaaS / Access / Suspicious Login Attempt
- SaaS / Compromise / Login From Rare Following Suspicious Login Attempt(s)
- SaaS / Email Nexus / Unusual Location for SaaS and Email Activity
その後、受信箱ルールの作成、Azure ADへのアプリケーションの登録、大量のEメール送信などの活動により、以下のDETECT モデルが侵害されました。
- SaaS / Admin / OAuth Permission Grant
- SaaS / Compromise / Unusual Logic Following OAuth Grant
- SaaS / Admin / New Application Service Principal
- IaaS / Admin / Azure Application Administration Activities
- SaaS / Compliance / New Email Rule
- SaaS / Compromise / Unusual Login and New Email Rule
- SaaS / Email Nexus / Suspicious Internal Exchange Activity
- SaaS / Email Nexus / Possible Outbound Email Spam
- SaaS / Compromise / Unusual Login and Outbound Email Spam
- SaaS / Compromise / Suspicious Login and Suspicious Outbound Email(s)

Darktrace RESPOND™が自律応答モードで有効になっている場合、PerfectData Softwareの活動チェーンは、以下のRESPOND モデルの違反につながりました:
Antigena / SaaS / Antigena Suspicious SaaS Activity Block
Antigena / SaaS / Antigena Significant Compliance Activity Block
In response to these model breaches, Darktrace RESPOND took immediate action, performing aggressive, inhibitive actions, such as forcing the actor to log out of the SaaS platform, and disabling the user entirely. When applied autonomously, these RESPOND actions would seriously impede an attacker’s progress and minimize network disruption.

また、Darktrace Cyber AI Analystは、PerfectData Softwareアプリケーションの登録内容を自律的に調査し、その結果を消化しやすいレポートにまとめることができました。

結論
Microsoft 365サービスの職場への普及とリモートワークの継続的な重視により、アカウントの乗っ取りは、世界中の組織にとって以前よりも深刻な脅威になりました。ここで取り上げた事例は、悪意のある行為者がVPNサービスに関連するエンドポイントから活動を行う傾向を示すとともに、PerfectData Softwareのように悪意のある新しいアプリケーションを登録することもあります。
悪意あるアクターがアカウントハイジャックにPerfectData Softwareを使用した理由は不明ですが、このアプリケーションの正規版または偽装版が、脅威行為者の手口として出現する可能性が非常に高くなっていることは明らかです。
Darktrace DETECT’s anomaly-based approach to threat detection allowed it to recognize that the use of ‘PerfectData Software’ represented a deviation in the SaaS user’s expected behavior. While Darktrace RESPOND, when enabled in autonomous response mode, was able to quickly take preventative action against threat actors, blocking the potential use of the application for data exfiltration or other nefarious purposes.
付録
MITRE ATT&CK マッピング
偵察:
T1598 - フィッシングによる情報提供
クレデンシャルアクセス:
-T1110 - ブルートフォース
初期アクセス:
- T1078.004 - 有効なアカウント:クラウドアカウント
コマンド&コントロール:
- T1105 - Ingressツール転送
永続性:
- T1098.003 - アカウントの操作:クラウドの役割の追加
収集:
- T1114 - Eメールコレクション
防御回避:
T1564.008 - アーティファクトを隠す:Eメール非表示ルール
ラテラルムーブメント:
- T1534 - 社内向けスピアフィッシング
異常なソースIP
- 5.62.60[.]202 (AS198605 AVAST Software s.r.o.)
- 160.152.10[.]215 (AS37637 Smile-Nigeria-AS)
197.244.250[.]155 (AS37705 TOPNET)
- 169.159.92[.]36 (AS37122 SMILE)
- 45.62.170[.]237 (AS396073 MAJESTIC-HOSTING-01)
92.38.180[.]49 (AS202422 G-Core Labs S.A.)
129.56.36[.]26 (AS327952 AS-NATCOM)
92.38.180[.]47 (AS202422 G-Core Labs S.A.)
- 107.179.20[.]214 (AS397086 LAYER-HOST-HOUSTON)
45.62.170[.]31 (AS396073 MAJESTIC-HOSTING-01)
参考文献
[1] https://www.investing.com/academy/statistics/microsoft-facts/
[2] https://intel471.com/blog/countering-the-problem-of-credential-theft
[3] https://darktrace.com/blog/business-email-compromise-to-mass-phishing-campaign-attack-analysis
[4] https://darktrace.com/blog/breakdown-of-a-multi-account-compromise-within-office-365