はじめに
先週Darktraceはある中規模の企業において4週間のトライアルを実施中に、標的型Sodinokibiランサムウェアを検知しました。
本ブログ記事では攻撃ライフサイクルのすべての段階について、攻撃者の使用した戦術、技術、手順、およびDarktraceがどのようにこの攻撃を検知したかを詳しく見ていきます。
Sodinokibiグループは、 ‘二重の脅威’ として知られる革新的な脅威アクターです。ランサムウェアを使った標的型の攻撃を実行すると同時に被害者のデータを抜き出すその能力からそう呼ばれています。この能力により彼らは身代金が払わられなければデータを公開するという脅しをかけることができます。
DarktraceのAIはこの攻撃の発生とともにリアルタイムに識別することができましたが、セキュリティチームはDarktraceを注視しておらずアラートに対処できませんでした。またAntigena もアクティブモードに設定されていませんでした。設定されていれば攻撃を遅らせ脅威を即座に封じ込めていたはずです。
タイムライン
以下のタイムラインは主な攻撃のフェーズの概要です。ほとんどの攻撃が1週間内に発生しており、大半のアクティビティは最後の3日間に集中しています。

技術分析
Darktraceは2つの主なデバイスが攻撃されたことを検知しました。これらはインターネットに接続されたRDPサーバー(以後‘RDP サーバー’と呼びます)およびSMBファイルサーバーとしても機能していたドメインコントローラ(以後‘DC’と呼びます)でした。
過去の攻撃では、Sodinokibiはランサムウェアアクティビティにホストレベル暗号化を使用しました。これは侵害されたホスト自体で暗号化が行われるものです。これに比べてネットワークレベルの暗号化では多くのランサムウェアアクティビティがSMBなどのネットワークプロトコルを介して実行されます。
最初の侵入
数日間に渡り、被害企業の外部と接続されたRDPサーバーがウクライナにある未知の外部IPアドレスから成功したRDP接続を受信していました。
最初の偵察活動が開始される直前、Darktraceは別のRDP接続がRDPサーバーに対して前に見られたものと同じRDPアカウントを使って行われていることを観測しました。この接続は1時間近く継続しました。
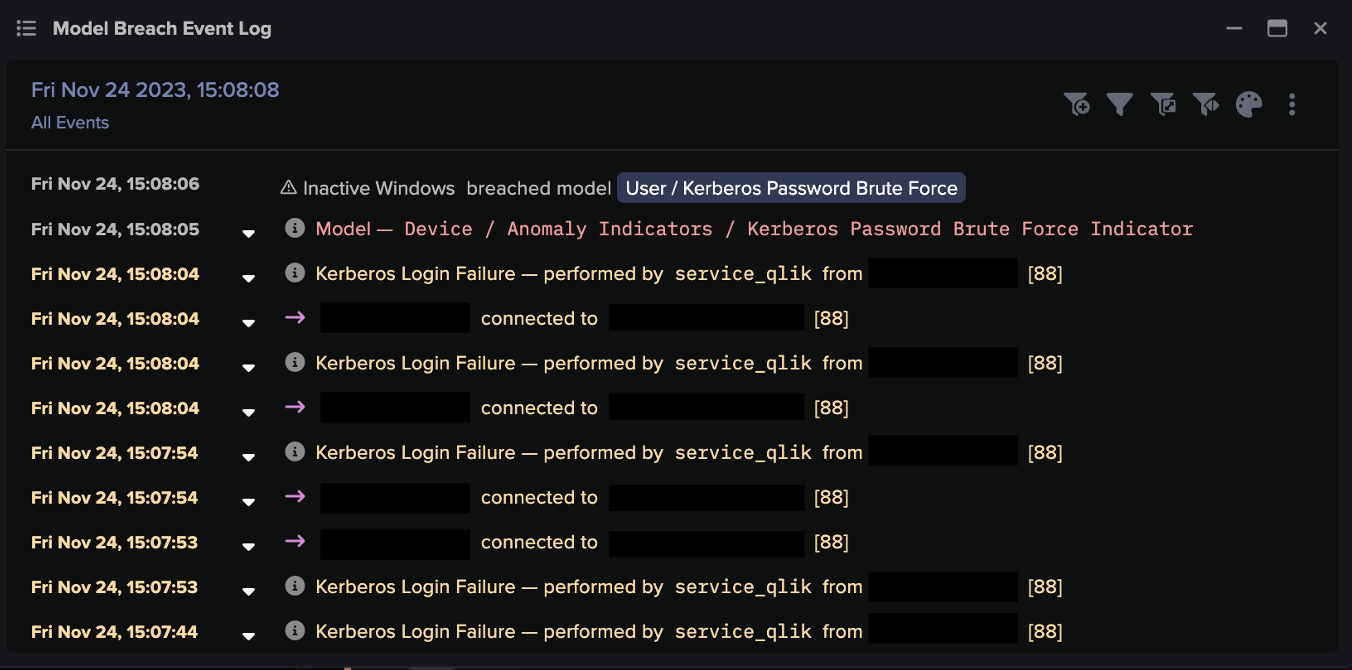
この攻撃で使用されたRDPの認証情報は、攻撃前のどこかの時点で、一般的なブルートフォース攻撃、クレデンシャルスタッフィング攻撃、あるいはフィッシングにより漏えいしていたと思われます。
DarktraceのDeep-Packet Inspection機能により、接続とすべての関連情報を明確に確認することができます:
疑わしいRDP接続の情報:
時間: 2020-02-10 16:57:06 UTC
ソース: 46.150.70[.]86 (ウクライナ)
デスティネーション: 192.168.X.X
送信先ポート: 64347
プロトコル: RDP
Cookie: [REDACTED]
継続時間: 00h41m40s
データ出力: 8.44 MB
データ受信: 1.86 MB
Darktraceはこの組織に通常接続しないIPアドレスから着信RDP接続を検知しました。
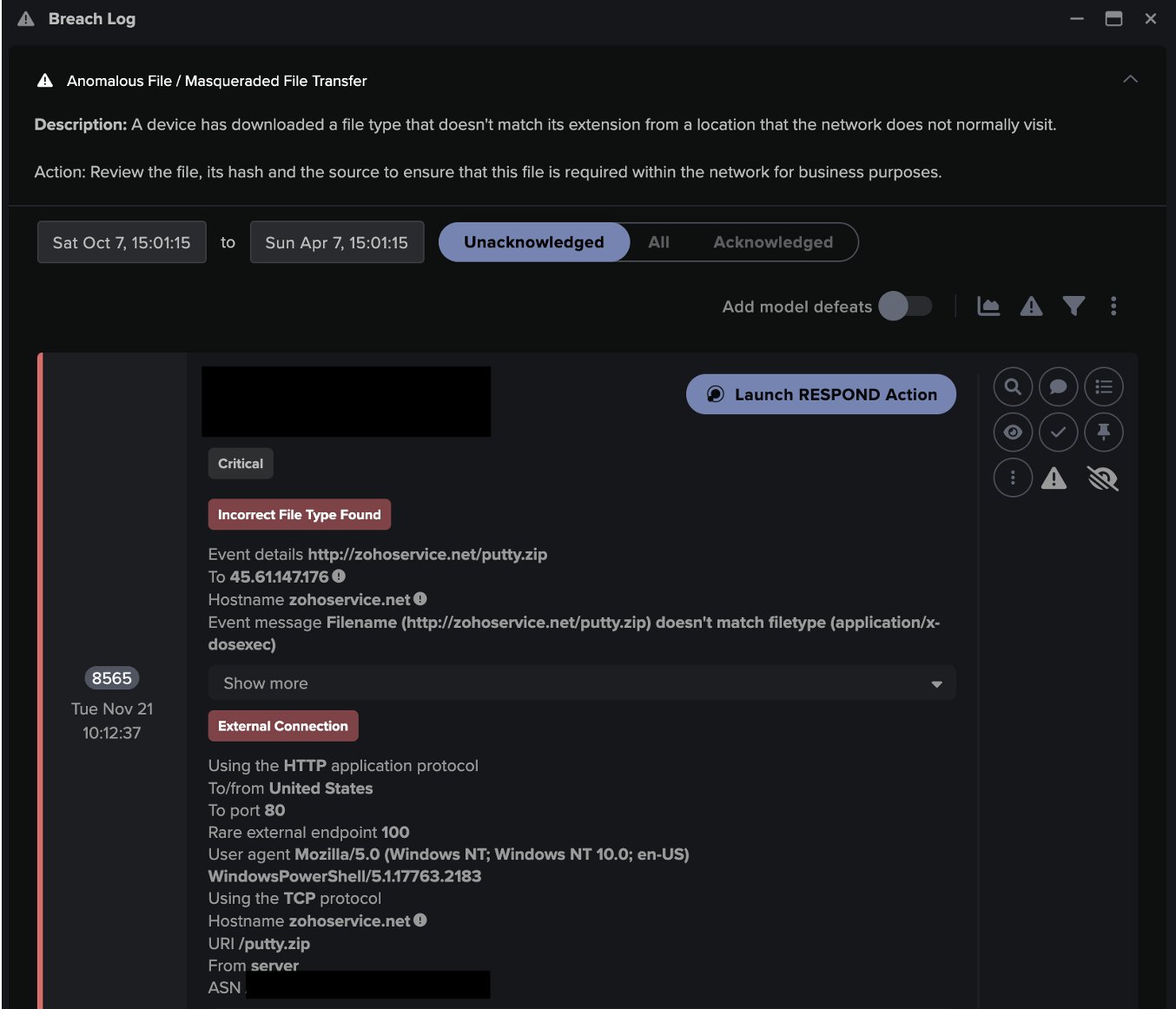
攻撃ツールのダウンロード
ウクライナからの不審なRDP接続から約54分後、RDPサーバーは人気のあるファイル共有プラットフォームMegauploadに接続し、そこから300MB近いデータをダウンロードしました。
DarktraceのAIはこのサーバーも、自動的に検知されたピアグループも、そして同じネットワーク上の誰も、Megauploadを利用しておらず、その結果これを即座に異常な動作として検知し、通常とは異なる動作であるとのフラグを立てました。

フルホスト名およびダウンロードに実際に使われたIP同様、Megauploadはこの組織にとって100%稀であったのです。
その後、40GBを超えるデータがMegauploadにアップロードされることになります。おそらく最初の300MBのダウンロードは、脅威アクターが追加のツールとC2インプラントを被害者の環境に導入したものと思われます。
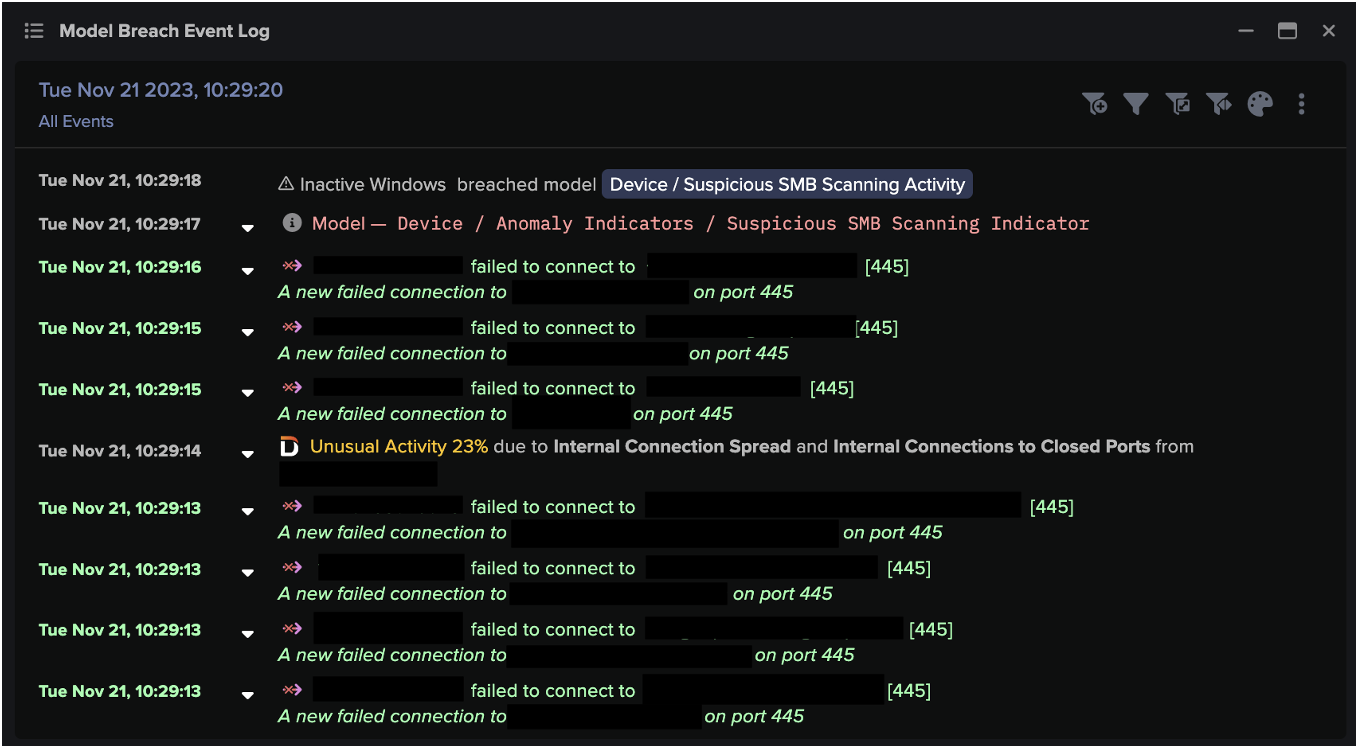
内部偵察
MegauploadからRDPサーバーへのダウンロードのわずか3分後、Darktrace はRDPサーバーが異常なネットワークスキャンを行っていると警告しました:

RDPサーバーは同じサブネット上の9台の内部デバイスを7つのポート21、80、139、445、3389、4899、8080に対してスキャンしました。 攻撃的セキュリティのノウハウを多少持っている人であれば誰でも、これらのポートのほとんどがWindows環境で水平移動を行うためにスキャンするデフォルトポートであることに気づくでしょう。このRDPサーバーは通常ネットワークスキャンを行いませんので、Darktraceはこのアクティビティについても高度に異常であると識別しました。
その後、脅威アクターがさらなるネットワークスキャンを行う様子が観測されます。彼らは大胆になり、より汎用のスキャンを使うようになりました。そのうちの1つはNmapでデフォルトユーザーエージェントを使っていました:

さらなるコマンドアンドコントロールトラフィック
最初のC2トラフィックは主にRDPを使っていたと思われますが、脅威アクターは、今度はさらなる永続性を確立し、より弾力性の高いC2チャネルを構築しようとしました。
最初のネットワークスキャン(2020年2月10日19:17頃)実施後ほどなく、RDPサーバーは被害者の環境において通常は見られない不審な外部サービスを使った通信を開始しました。
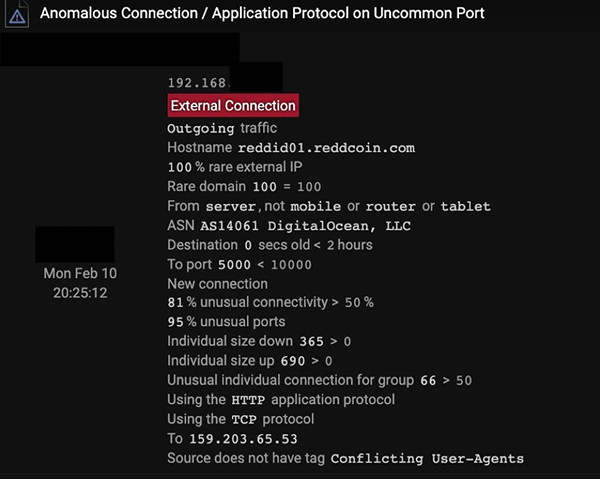
Reddcoinへの通信
Reddcoinについても、ネットワーク上で他に使っている人はいませんでした。さらにこのアプリケーションプロトコルと外部ポートの組み合わせはネットワークにとってもきわめて不審なものでした。
通信はReddcoin APIに対しても行われ、手動の接続ではなくソフトウェアエージェントをインストールしようとしていることがわかりました。これが検知されたのは、Reddcoinがネットワークから見て稀であっただけでなく、「若い」ことも理由でした。つまり、この外部接続先は25分前まではネットワーク上で接続された形跡がなかったのです。

Reddcoin APIへの通信

Exceptionless[.io]への通信
このように、exceptionalness[.]io への通信はビーコニングの要領で Let’s Encrypt 証明書を使って行われていました。これはネットワークにとって稀であり通常とは異なる JA3 クライアントハッシュを使っていました。これらのことは、脅威アクターが300MBのツール類をダウンロードした直後に、デバイス上に新しいソフトウェアが存在していることを示しています。
上記のネットワークアクティビティのほとんどは、脅威アクターがツールをRDPサーバーに投下した直後に発生していますが、ReddcoinおよびExceptionlessとの接続の具体的な目的は不明です。この攻撃者は市販のツール(Megaupload、Nmap等)を使うことを好むようなので、これらのサービスをC2あるいはテレメトリー収集目的で使ったのかもしれません。
これで2月10日のほとんどのアクティビティが終了しました。
さらなるコマンドアンドコントロールトラフィック
攻撃者がなぜこのようなことをするのでしょうか?多くのC2を一度に使うことは1つか2つのチャネルを使うよりもずっとノイズが大きくなります。
2月12日と13日にも、著しいアクティビティの増加がみられました。
RDPサーバーは多数の高度に異常かつ稀な接続を外部デスティネーションに対して実行し始めました。以下のサービス、IPおよびドメインがC2目的でのみ使われたものかどうかは不確定ですが、高い確度で攻撃者のアクティビティとリンクされたものです:
- vkmuz[.]netへのHTTPビーコニング
- 著しいTorの使用量
- 非標準RDPポート29348番を使った198-0-244-153-static.hfc.comcastbusiness[.]netへのRDP接続
- 管理者アカウント(ジオロケーションがロシア)を使った92.119.160[.]60へのRDP接続
- Megauploadへの接続継続
- Exceptionless[.]io へのSSLビーコニング継続
- api.reddcoin[.]comへの接続継続
- freevpn[.]zoneへのSSLビーコニング
- 31.41.116[.]201 の/index.php への新しいユーザーエージェントを使ったHTTPビーコニング
- aj1713[.]onlineへの不審なSSL接続
- Pastebinへの接続
- 不審なJA3クライアントハッシュを使ったwww.itjx3no[.]comへのSSLビーコニング
- safe-proxy[.]comへのSSLビーコニング
- 事前のDNSホスト名ルックアップのないwestchange[.]topへのSSL接続(マシンドリブンの可能性)
ここで目立っているのは、(潜在的)C2チャネルの多様性です。Tor、ダイナミックISPアドレスへのRDP、VPNソリューションおよびおそらくカスタム / カスタマイズされた市販のインプラント(DGA様のドメインおよびIPから/index.phpへのHTTP)などです。
攻撃者がなぜこのようなことをするのでしょうか?多くのC2を一度に使うことは1つか2つのチャネルを使うよりもずっとノイズが大きくなります。
一つの答えは、攻撃者がステルス性よりも短期的なレジリエンスを重視していたということかもしれません。このネットワーク内の攻撃全体が7日間しかかかっておらず、大半のアクティビティが2.5日間で発生していたことを考えると、これは理解できます。別の可能性としては、攻撃時にさまざまな人物が並行して関与していたということも考えられます。1人の攻撃者はハッキングにおいてRDPセッションを好み、別の攻撃者はよりスキルが高く特定のポストエクスプロイト用フレームワークを使用した、ということかもしれません。
金銭目的でのこの攻撃の全体としての手口は、Advanced Persistent Threat (APT)攻撃のようなステルス性の、スパイ関連インシデントに見られるものよりも、スマッシュアンドグラブ(ガラス窓を破ってひったくる)的なものだったと言えます。
データ漏えい
DCは24時間にわたりおよそ40GBのデータをMegauploadにアップロードしました。
上記のアクティビティはすべてRDPサーバー(最初の上陸拠点の役割を果たした)上で観測されましたが、次のデータ抜き出しはRDPサーバーと同じサブネット上のドメインコントローラー(DC)で観測されました。
DCは24時間にわたりおよそ40GBのデータをMegauploadにアップロードしました。
Darktraceはこのデータ抜き出しを進行中に検知しました。DC(または類似のデバイス)が同じような量のデータをインターネットにアップロードしたことはありませんでした。さらに、被害者企業の環境内のいずれのクライアントあるいはサーバーもMegauploadを使用していなかったのです。

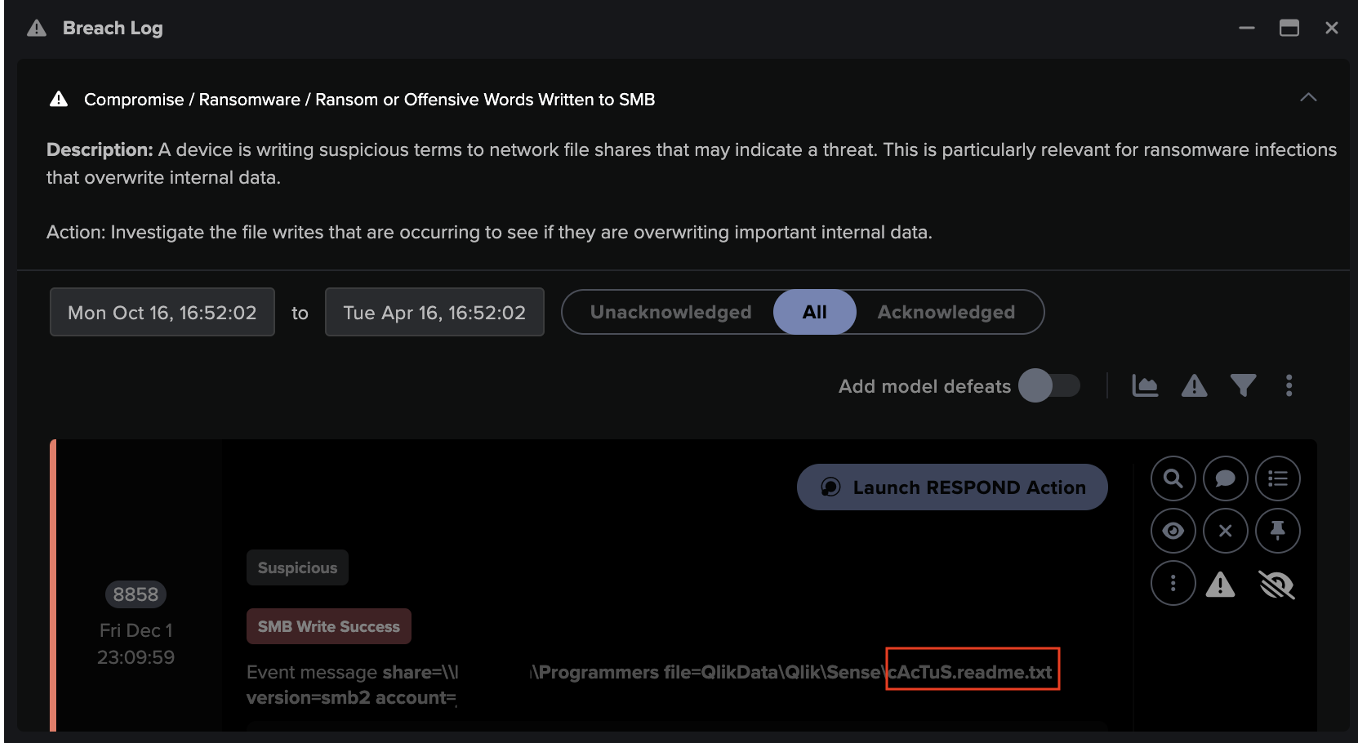
脅迫文
最後に、Darktraceは2月13日には不審なファイルが内部SMB共有上でアクセスされていることを検知しました。これらのファイルは脅迫文のようでした。Sodinokibiグループの他の被害者が報告しているのと同様に、ランダムに生成されたファイル名を使っていました:
413x0h8l-readme.txt
4omxa93-readme.txt
まとめと考察
脅威アクターはほとんど市販のツールを使っており、これによりアトリビューションがしにくくなるとともに、検知もより難しくなります。
この攻撃は現在のランサムウェアの特徴の多くを備えていました。金銭目的で、動きが速く、標的型でした。
脅威アクターはほとんど市販のツール(RDP、Nmap、Mega、VPNソリューション)を使っており、これによりアトリビューションがしにくくなるとともに、検知もより難しくなります。こうしたツールの使用によりしばしば通常の管理アクティビティに紛れ込むことが可能になります。異常検知を使用しないと、このようなアクティビティは検知できません。
外部に送信される数千の普通のRDP接続のなかから、1つの異常な発信RDP接続をどうやって特定できるでしょうか?Megauploadの使用が、ユーザーによる普通の使い方ではなく、悪意のあるものであるとどうやって知ることができるでしょうか?Darktraceの自己学習型AIが威力を発揮するのはこうした点です。
Darktraceは脅威インテリジェンスや静的なシグネチャを一切使用することなく、攻撃ライフサイクルのあらゆる段階を検知しました。
以下の図は侵害された2つのデバイスでの検知結果の概要です。侵害されたこれらのデバイスはネットワーク内で最もスコアの高いアセットでした。Darktraceの使用経験があまりない初級レベルのアナリストであっても、このような進行中の攻撃をリアルタイムに識別することができます。

RDPサーバー
RDPサーバー上での検知結果には次が含まれていました:
- Compliance / File Storage / Mega - Megauploadの不審な使用
- Device / Network Scan - 不審なネットワークスキャンの検知
- Anomalous Connection / Application Protocol on Uncommon Port - 通常と異なるポート上でのプロトコル使用の検知
- Device / New Failed External Connections - 不審なC2の失敗を検知
- Compromise / Unusual Connections to Let’s Encrypt - Let’s Encryptを使ったSSLによるC2の可能性を検知
- Compromise / Beacon to Young Endpoint - ネットワークにとって新しい外部エンドポイントへのC2を検知
- Device / Attack and Recon Tools - Nmap等の既知の攻撃的セキュリティツールの検知
- Compromise / Tor Usage - 不審なTor使用の検知
- Compromise / SSL Beaconing to Rare Destination - ジェネリックSSL C2の検知
- Compromise / HTTP Beaconing to Rare Destination - ジェネリックHTTP C2の検知
- Device / Long Agent Connection to New Endpoint - デバイス上で通常と異なるサービスを検知
- Anomalous Connection / Outbound RDP to Unusual Port - 不審なRDP C2を検知

DC
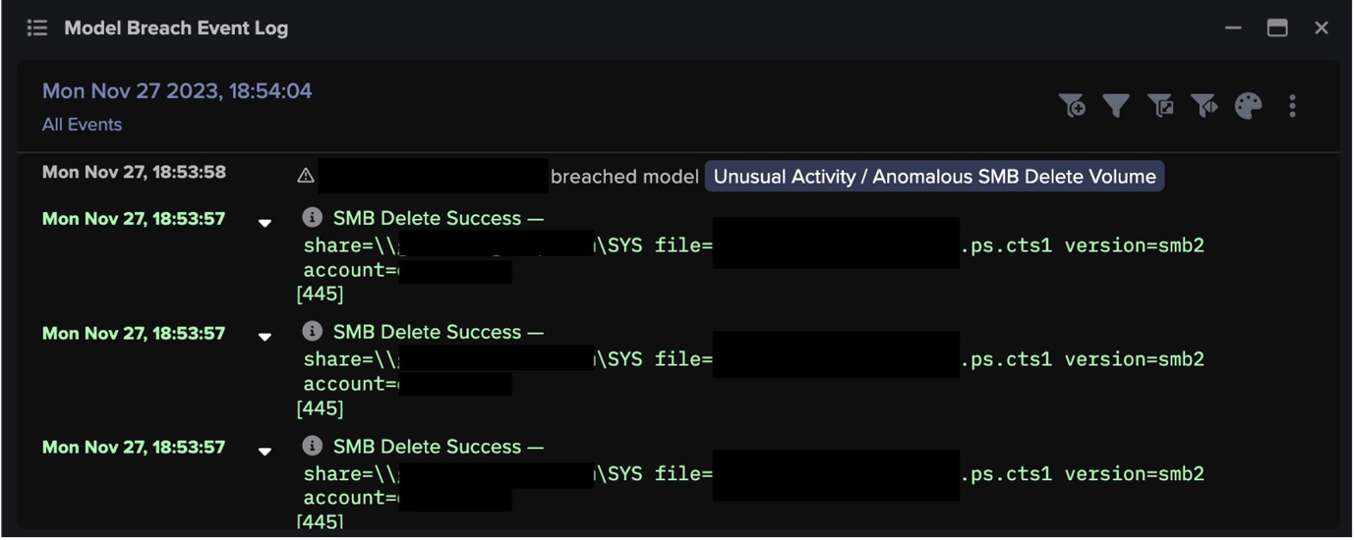
DC上での検知結果には次が含まれていました:
- Anomalous Activity / Anomalous External Activity from Critical Device - dcs上の不審な動作の検知
- Compliance / File Storage / Mega - Megauploadの不審な使用
- Anomalous Connection / Data Sent to New External Device - 不審なロケーションへのデータ抜き出し
- Anomalous Connection / Uncommon 1GB Outbound - 不審な接続先への大量のデータ送信
- Anomalous Server Activity / Outgoing from Server - インターネット上の不審なエンドポイントへのC2の可能性
































![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)