2022年6月、Darktrace は同社のクライアントベースでQakbotの感染急増が確認しました。検知されたQakbotの感染は、場合によってはCobalt StrikeやDark VNCなどの2次ペイロードの配信につながり、2022年初頭にMicrosoftがXL4とVBAマクロをデフォルトでブロックしたこと[1]/[2]/[3]/[4]や、Microsoft Support Diagnostic Tool(MSDT)におけるFollina脆弱性の公開 [5] から生まれた新しい配信方式によって開始されたものでした。Qakbotの配信方法に変更が加えられたにもかかわらず、Qakbotの感染により、ネットワークアクティビティに異常なパターンが生じることは避けられませんでした。このブログでは、これらのネットワーク活動の詳細について、Darktrace/Networkのカバレッジ内容とともにご紹介します。
Qakbotの背景
Qakbotは、2007年に銀行の認証情報などの機密データを盗むために設計された銀行トロイの木馬として登場しました。 それ以来、Qakbotは、情報を盗むだけでなく、悪意のあるペイロードを投下し、バックドアとして機能する、高度にモジュール化された三拍子揃った脅威として発展しています。また、このマルウェアは汎用性が高く、脅威の変化に応じて配信方法も定期的に変更されています。
脅威アクターは、Eメールベースの配信手法でQakbotを配信します。2022年前半、Microsoftは、XL4およびVBAマクロをデフォルトでブロックするバージョンのOfficeの展開を開始しました。この変更以前は、Qakbotのメールキャンペーンは、通常、悪意のあるマクロを含むOfficeの添付ファイルを含む詐欺的なメールの拡散で構成されていました。 これらの添付ファイルを開き、その中のマクロを有効にすることで、ユーザーのデバイスにQakbotがインストールされることになります。
ユーザーのデバイスにQakbotを配信するアクターは、そのアクセス権を他のアクターに売却したり、Qakbotの機能を活用して独自の目的を追求したりすることがあります[6]。Qakbotを使用するアクターの共通の目的は、感染したシステム上にCobalt Strikeビーコンを投下することです。そして、脅威アクターは、Cobalt Strikeが提供するインタラクティブなアクセスを活用して、広範なランサムウェアの展開に備えた広範な偵察とラテラルムーブメントを行います。Qakbotは、そのモジュール性と汎用性に加え、ランサムウェアの活動と密接な関係があるため、組織のデジタル環境にとって重大な脅威となるマルウェアです。
活動の詳細とQakbotの配信方法
6月の1か月間、いくつかのクライアントネットワークにおいて、以下のようなネットワーク活動のバリエーションが観察されました。
1. ユーザーの端末がoutlook.office[.]com や mail.google[.]comなどのメールサービスにコンタクトを取る
2. ユーザーの端末が、185.234.247[.]119に対して、Officeユーザーエージェント文字列とターゲットURI「/123.RES」を指定してHTTP GETリクエストを実行し、このリクエストに対して、Follina脆弱性(CVE-2022-30190)を悪用したHTMLファイルが応答する
3. ユーザーのデバイスは、cURL User-Agent文字列と '.dat' で終わるターゲットURIを使用して、通常とは異なる外部エンドポイントにHTTP GETリクエストを実行し、このリクエストには、QakbotのDLLサンプルが応答する
4. ユーザーのデバイスが443、995、2222、32101などのポートを介してQakbot Command and Controlサーバーにコンタクトする
ステップ1と4だけが見える場合もあれば、ステップ1、3、4だけが見える場合もあります。このパターンの違いは、Qakbotの配信方法の違いに対応しています。

Qakbotは、悪意のあるEメールの添付ファイルを介して配信されることが知られています [7]。6月中にDarktraceのクライアントベースで観測されたQakbotの感染は、HTMLの添付ファイルに悪意のあるコードを埋め込む手法であるHTMLスマグリングによって開始された可能性が高いと思われます。オープンソースのレポート [8]-[14] と観察されたネットワークトラフィックのパターンに基づき、2022年6月にDarktraceのクライアントベースで観察された Qakbot 感染は以下の3つの方法のいずれかによって開始されたと、中程度から高い信頼度で評価しています:
- ユーザーはHTMLの添付ファイルを開き、ZIPファイルをデバイスにドロップします。ZIPファイルにはLNKファイルが含まれており、これを開くと、ユーザーのデバイスはcURLユーザーエージェント文字列とターゲットURI「.dat」を指定して外部HTTP GETリクエストを行います。成功すると、HTTP GETリクエストにQakbot DLLが応答します。
- ユーザーはHTMLの添付ファイルを開き、ZIPファイルをユーザーのデバイスにドロップします。ZIPファイルにはdocxファイルが含まれており、これを開くと、ユーザーのデバイスは、Officeユーザーエージェント文字列と「/123.RES」ターゲットURIを持つ185.234.247[.] 119に対してHTTP GETリクエストを行います。成功すると、HTTP GETリクエストに対して、Follinaエクスプロイトを含むHTMLファイルが応答します。Follina エクスプロイトは、ユーザーのデバイスに、ターゲット URI が「.dat」である外部 HTTP GET を実行させるように仕向けます。成功すると、HTTP GET リクエストに Qakbot DL が応答します。
- ユーザーがHTMLの添付ファイルを開くと、ZIPファイルがデバイスにドロップされます。ZIPファイルには、Qakbot DLLとLNKファイルが含まれており、開くとDLLが実行されます。
これらの配信方法は、マクロを埋め込んだOfficeドキュメントから、コンテナファイル、Windowsショートカット(LNK)ファイル、新しい脆弱性のエクスプロイトへと、マルウェア配信技術を変化させ、脅威アクターがポストマクロの世界にいかに適応しているかを示しています。[4]
Darktraceのクライアントベースで観察されたQakbot感染は、その提供方法が異なるだけでなく、フォローアップ活動の点でも異なっていました。中には、フォローアップ活動が見られないケースもありました。しかし、Qakbotを利用してデータを流出させ、Cobalt StrikeやDark VNCといった後続のペイロードを配信しているケースも確認されています。これらのフォローアップ活動は、ランサムウェアを展開するための準備であると考えられます。Darktraceセキュリティチームは、クライアント環境内の Qakbot の活動を早期に検知することで、ランサムウェアの展開を防ぐことができたと思われる措置をとることができました。
Darktrace のカバレッジ
ユーザーが悪意のあるEメールの添付ファイルを使用した場合、通常、ユーザーの端末は、空のHostヘッダーと「.dat」で終わるターゲットURI(「/24736.dat」や「/noFindThem.dat」など)でcURL HTTP GETリクエストを、稀な外部のエンドポイントに送信することになりました。Follinaの脆弱性が悪用されたと考えられるケースでは、ユーザーの端末がcURLのHTTP GETリクエストを行う前に、Microsoft OfficeのUser Agent文字列を含む 185.234.247[.]119 にHTTP GETリクエストを行ったことが確認されています。これらのHTTPアクティビティの結果として典型的に侵入されたのは、以下のDarktrace DETECT/Networkモデルです。
- Device / New User Agent
- Anomalous Connection / New User Agent to IP Without Hostname
- Device / New User Agent and New IP
- Anomalous File / EXE from Rare External Location
- Anomalous File / Numeric Exe Download
これらのDETECT モデルは、影響を受けたデバイスにおけるOfficeとcURLのユーザーエージェント文字列の異常な使用と、稀な外部エンドポイントからのQakbot DLLのダウンロードを捕捉することが出来ました。これらのモデルは、悪意のあることが知られているユーザーエージェント文字列、URI、ファイル、および外部IPを含む活動ではなく、デバイスの通常の動作パターンから外れた異常な活動を探します。
有効化すると、Darktrace RESPOND/Networkが自律的に介入し、「グループの生活パターンを強制する」や 「接続をブロックする」などのアクションを取り、Qakbotインフラへの接続を迅速に遮断します。



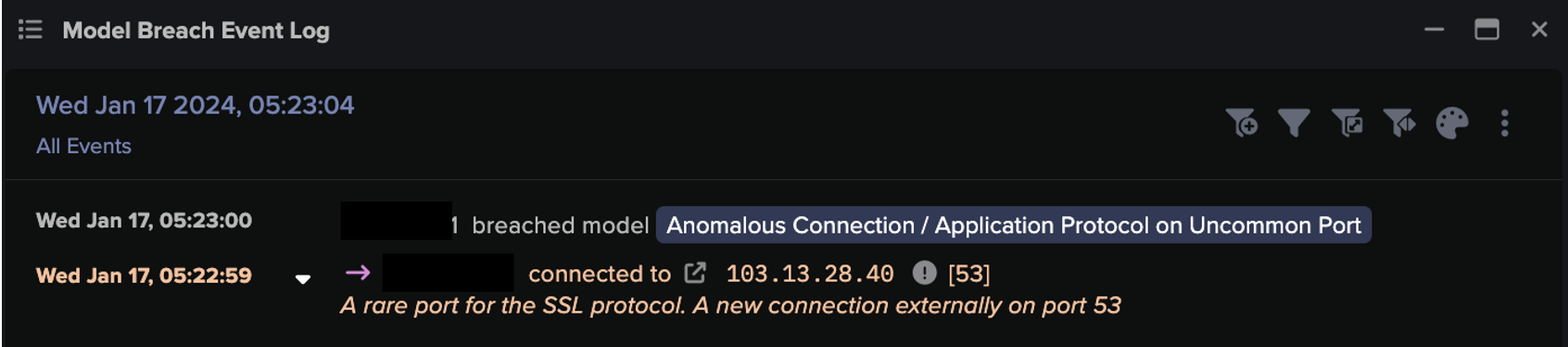
Qakbotのインストール後、ユーザーのデバイスは443、22、990、995、1194、2222、2078、32101などのポート上でコマンド&コントロール(C2)エンドポイントに接続するようになりました。Cobalt StrikeとDark VNCは、これらのC2接続を介して配信された可能性があり、Cobalt StrikeとDark VNCに関連するエンドポイントへのその後の接続で証明されます。これらのC2活動は通常、以下のDarktrace DETECT/Networkモデルの侵害を引き起こしました。
- Anomalous Connection / Application Protocol on Uncommon Port
- Anomalous Connection / Multiple Connections to New External TCP Port
- Compromise / Suspicious Beaconing Behavior
- Anomalous Connection / Multiple Failed Connections to Rare Endpoint
- Compromise / Large Number of Suspicious Successful Connections
- Compromise / Sustained SSL or HTTP Increase
- Compromise / SSL or HTTP Beacon
- Anomalous Connection / Rare External SSL Self-Signed
- Anomalous Connection / Anomalous SSL without SNI to New External
- Compromise / SSL Beaconing to Rare Destination
- Compromise / Suspicious TLS Beaconing To Rare External
- Compromise / Slow Beaconing Activity To External Rare

これらのC2活動を検知したDarktrace DETECT/Network モデルは、既知の悪意のあるエンドポイントに接続するデバイスを探すのではありません。むしろ、通常の活動パターンから逸脱し、内部デバイスが通常接続しない外部エンドポイントに、通常接続しないポートを介して接続するデバイスを探します。
Qakbotに感染したシステムからデータを流出させ、Cobalt Strikeを投下して、大規模な調査を行うケースも確認されています。これらの侵入活動は、通常、以下のモデルの侵入を引き起こしました:
- Anomalous Connection / Data Sent to Rare Domain
- Unusual Activity / Enhanced Unusual External Data Transfer
- Anomalous Connection / Uncommon 1 GiB Outbound
- Anomalous Connection / Low and Slow Exfiltration to IP
- Unusual Activity / Unusual External Data to New Endpoints
脅威アクターが行った偵察とブルートフォース活動は、通常、以下のモデルブリーチをもたらしました:
- Device / ICMP Address Scan
- Device / Network Scan
- Anomalous Connection / SMB Enumeration
- Device / New or Uncommon WMI Activity
- Unusual Activity / Possible RPC Recon Activity
- Device / Possible SMB/NTLM Reconnaissance
- Device / SMB Lateral Movement
- Device / Increase in New RPC Services
- Device / Spike in LDAP Activity
- Device / Possible SMB/NTLM Brute Force
- Device / SMB Session Brute Force (Non-Admin)
- Device / SMB Session Brute Force (Admin)
- Device / Anomalous NTLM Brute Force
結論
2022年6月、Qakbotは、MicrosoftのマクロのデフォルトブロックとFollina脆弱性の一般公開に対応する形で迅速に自己形成しました。2022年前半の脅威の進化により、Qakbotは配信方法を変更し、マクロを使用した配信方法からHTMLスマグリングによる配信方法へと移行しました。これらの新しい配信方法の有効性は、2022年6月に大量のQakbot感染が確認されたDarktraceのクライアントベースで浮き彫りにされました。自己学習型AIを活用し、Darktrace DETECT/Networkは、これらの新しいQakbot感染から必然的に生じる異常なネットワーク挙動を検知することができました。これらのQakbot感染の背後にいるアクターはランサムウェアを展開しようとしていた可能性が高いことを考えると、これらの検知は、Darktrace RESPOND/Networkの自律的な介入とともに、最終的に影響を受けたDarktrace の顧客を重大なビジネスの混乱から保護するのに役立ちました。
付録

IoC一覧
.png)
.png)
.png)
参考文献
[1] https://techcommunity.microsoft.com/t5/excel-blog/excel-4-0-xlm-macros-now-restricted-by-default-for-customer/ba-p/3057905
[2] https://techcommunity.microsoft.com/t5/microsoft-365-blog/helping-users-stay-safe-blocking-internet-macros-by-default-in/ba-p/3071805
[3] https://learn.microsoft.com/en-us/deployoffice/security/internet-macros-blocked
[4] https://www.proofpoint.com/uk/blog/threat-insight/how-threat-actors-are-adapting-post-macro-world
[5] https://twitter.com/nao_sec/status/1530196847679401984
[6] https://www.microsoft.com/security/blog/2021/12/09/a-closer-look-at-qakbots-latest-building-blocks-and-how-to-knock-them-down/
[7] https://www.zscaler.com/blogs/security-research/rise-qakbot-attacks-traced-evolving-threat-techniques
[8] https://www.esentire.com/blog/resurgence-in-qakbot-malware-activity
[9] https://www.fortinet.com/blog/threat-research/new-variant-of-qakbot-spread-by-phishing-emails
[10] https://twitter.com/pr0xylife/status/1539320429281615872
[11] https://twitter.com/max_mal_/status/1534220832242819072
[12] https://twitter.com/1zrr4h/status/1534259727059787783?lang=en
[13] https://isc.sans.edu/diary/rss/28728
[14] https://www.fortiguard.com/threat-signal-report/4616/qakbot-delivered-through-cve-2022-30190-follina
Credit to: Hanah Darley, Cambridge Analyst Team Lead and Head of Threat Research and Sam Lister, Senior Cyber Analyst