Update: On January 26, 2023, the Hive ransomware group was dismantled and servers associated with the sale of the ransomware were taken offline following an investigation by the FBI, German law enforcement and the National Crime Agency (NCA). The activity detailed in this blog took place in 2022, whilst the group was still active.
RaaS in Cyber Security
ランサムウェアの脅威は、サイバー脅威を取り巻く環境において、セキュリティチームにとって常に懸念され続けています。ランサムウェア・アズ・ア・サービス(RaaS)の普及に伴い、経験の浅い「自称」攻撃者にとっても、ランサムウェアはますますアクセスしやすくなっています。このような参入障壁の低さの結果、ランサムウェア攻撃の量は大幅に増加すると予想されます。
さらに、RaaSは、購入者がランサムウェアの展開に使用する様々なキットや機能を選択できる、非常にカスタマイズ可能な市場であるため、攻撃の挙動が同じになることはほとんどありません。このような差異を効果的に検知し、保護するためには、ランサムウェアの進化のスピードに追いつけない攻撃チェーンに焦点を当てた、減価したIoCリストやプレイブックに頼るのではなく、異常の検知と予想される動作の逸脱に重点を置いたセキュリティ対策を実施することが極めて重要です。
2022年初頭、Darktraceの DETECT /Network™は、複数の顧客のネットワーク上でHiveランサムウェアの複数のインスタンスを確認しました。 Darktrace は、その アノマリベースの検知機能を使用して、コマンド&コントロール(C2)活動、ラテラルムーブメント、データ流出、そして最終的にはデータの暗号化と身代金のメモの書き込みなど、攻撃とキルチェーンの複数の段階を正常に検知することができました。
Hiveランサムウェア
Hiveランサムウェアは、2021年6月に初めて野生で観測された比較的新しいマルウェア株です。ヘルスケア、エネルギープロバイダー、小売業者などさまざまな業界をターゲットにすることが知られており、これまでに1,500以上の組織を攻撃し、1億米ドル以上の身代金の支払いを徴収したと報告されています。[1]
HiveはRaaSモデルで配布され、開発者は最終的な身代金の支払額の一定割合を受け取る代わりに、コードの更新と保守を行い、ユーザー(またはアフィリエイト)には、通常では使用できない高度で複雑なマルウェアを使用して攻撃を実行できるツールを提供します。Hiveは、ランサムウェアに関連する典型的な戦術、技術、手順(TTP)を使用しますが、それらは攻撃を実行するHiveのアフィリエイトによって変化します。
ほとんどの場合、身代金を要求する前に、まずデータを抜き取り、次に暗号化する二重の恐喝攻撃が行われます。被害者は、HiveLeaks のTORサイトなどで機密データが一般に流出する危険性があるため、攻撃者に有利に働くことになります。
攻撃のタイムライン
RaaSは高度にカスタマイズ可能なため、Hiveの攻撃者が採用する戦術や方法はケースバイケースで異なることが予想されます。しかし、Darktrace の顧客環境で確認されたHiveランサムウェアのインシデントの大半では、以下のような一般的な攻撃段階と特徴が確認されています、 Darktrace DETECTは、以下のような一般的な攻撃の段階と特徴を観察しました。これは、同じ脅威アクターから発生した攻撃、または特定の構成を持つバッチが様々な行為者に広く販売されていることを示している可能性があります。

初期アクセス
Hiveのアクターは、複数の異なるベクトルを通じてネットワークに初期アクセスすることが知られていますが、セキュリティ研究者によって報告された2つの主要な方法は、Microsoft Exchangeの脆弱性の悪用、または悪意のある添付ファイルを含むフィッシングメールの配信です。[2][3]
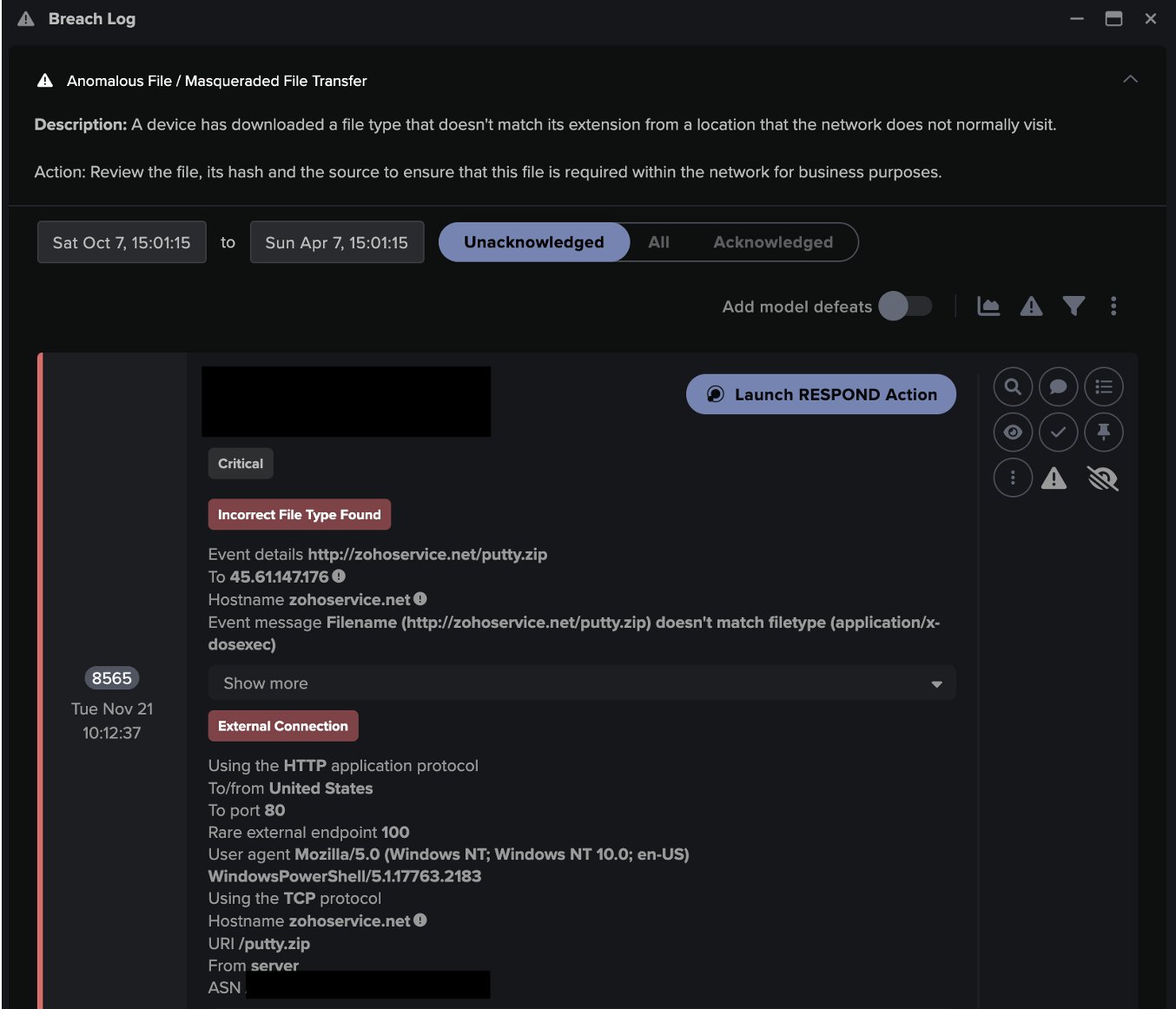
例えば、Darktrace の顧客のネットワーク上で観測されたある Hive ランサムウェア攻撃の初期段階で、Darktrace は、HTTP 経由で PowerShell ユーザーエージェントを使用して、稀な外部ロケーション 23.81.246[.]84 に接続するデバイスを検知しました。この接続中、デバイスは「file.exe」という名前の実行可能ファイルをダウンロードしようとしました。このファイルは、最初にフィッシングメール経由でアクセスされ、配信された可能性があります。しかし、攻撃時にDarktrace/Email が有効になっていなかったため、これはDarktraceの権限の範囲外でした。幸いにも、図2のパケットキャプチャ(PCAP)にあるように、接続はプロキシ認証に失敗し、ブロックされました。
このダウンロードの試みの直後、同じデバイスが、珍しい外部エンドポイントである 146.70.87[.]132から大量の受信SSL接続を受け始めました。Darktrace は、このエンドポイントがGo Daddy CAという簡単に入手してアクセスできるSSL証明書を使用しており、このエンドポイントからの受信SSL接続が増えたことはこのデバイスにとって珍しい挙動であると記録しました。
Darktrace が検知したこの非常に異常なアクティビティは、ランサムウェア攻撃がいつ始まったかを示していると思われ、おそらく最初のペイロードのダウンロードだと思われます。
Darktrace DETECT のモデル:
- Anomalous Connection / Powershell to Rare External
- Anomalous Server Activity / New Internet Facing System

C2 ビーコニング
初期アクセスに成功した後、Hiveアクターは、C2サーバーへの多数の接続と追加のステージャのダウンロードを通じて、感染したネットワーク上にC2インフラを確立し始めます。
Hiveランサムウェアに感染した顧客ネットワークにおいて、Darktrace は複数の希少なエンドポイントへの接続を大量に開始するデバイスを確認しました。これは、攻撃者のインフラに対するC2ビーコンである可能性が非常に高いです。ある特定の例では、オープンソースインテリジェンス(OSINT)のさらなる調査により、これらのエンドポイントがCobalt Strikeに関連していることが判明しました。
Darktrace DETECT のモデル:
- Anomalous Connection / Multiple Connections to New External TCP
- Anomalous Server Activity / Anomalous External Activity from Critical Network Device
- Compromise / High Volume of Connections with Beacon Score
- Compromise / Sustained SSL or HTTP Increase
- Compromise / Suspicious HTTP Beacons to Dotted Quad
- Compromise / SSL or HTTP Beacon
- Device / Lateral Movement and C2 Activity
内部偵察、ラテラルムーブメント、特権のエスカレーション
C2インフラが確立された後、Hiveアクターは通常、ネットワーク上で検知されないようにするため、アンチウイルス製品のアンインストールを開始します[3]。また、脆弱性やオープンチャネルを探すために内部偵察を行い、ネットワーク全体を横方向に移動することを試みます。
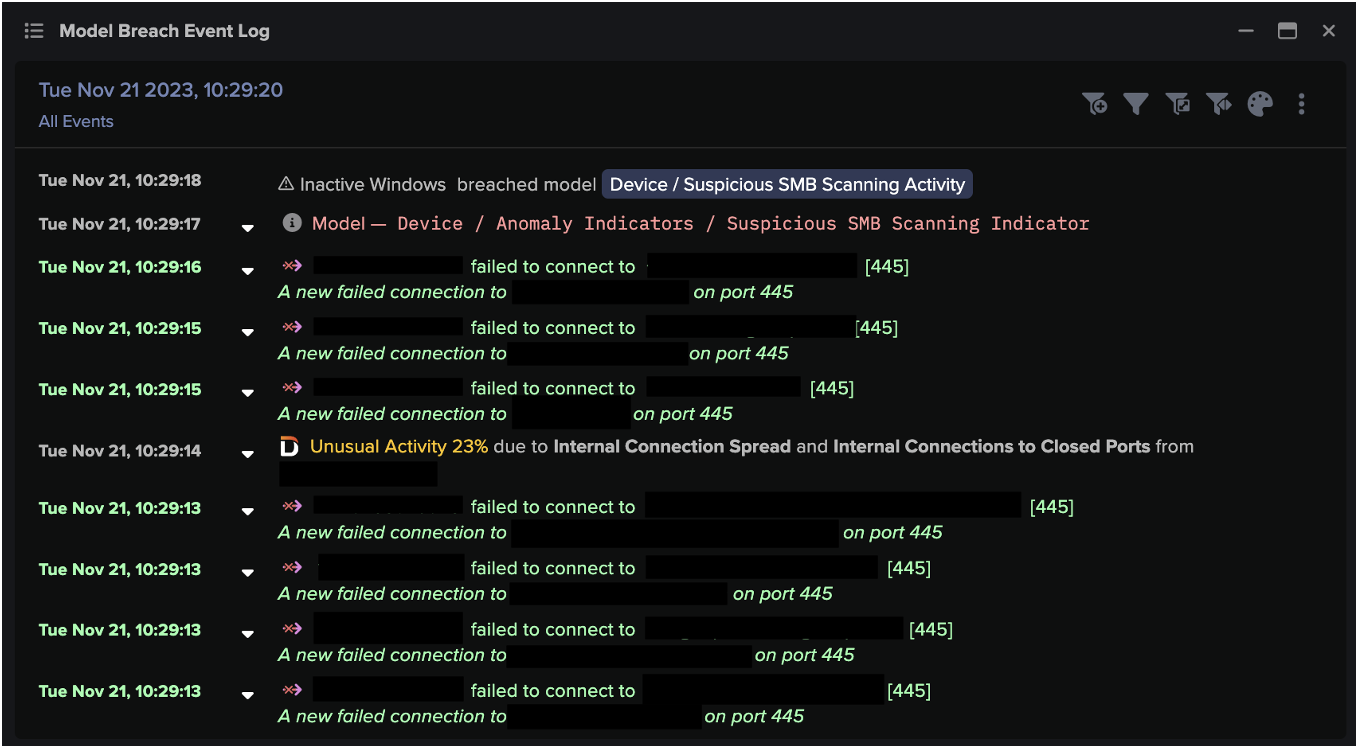
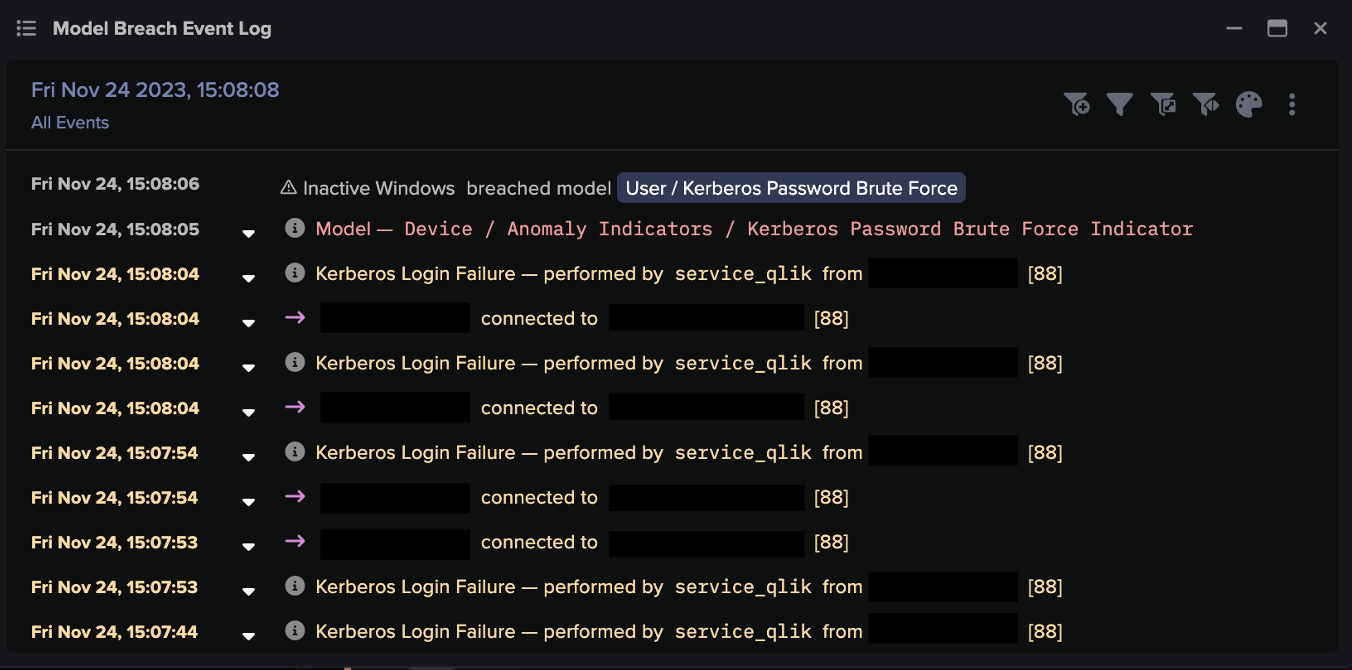
C2接続が行われる中、Darktraceは、ある顧客ネットワーク上のデバイスが他の内部デバイスへの接続を異常に大量に開始したことを確認し、攻撃に関連するネットワークスキャン活動を検知することができました。また、ある重要なネットワークデバイスがSMB経由で実行ファイル mimikatz.exe を書き込んでいるのが確認されましたが、これは一般的にクレデンシャルハーベスティングに用いられるMimikatz攻撃ツールであると思われます。
また、RDPおよびDCE-RPCを介したラテラルムーブメントの試みが複数検知され、攻撃者はAdministratorクレデンシャルを使用して認証に成功しました。あるケースでは、デバイスが ITaskScheduler のアクティビティを実行していることも観察されました。このサービスは、マシン上で実行されているタスクをリモートで制御するために使用され、悪意のあるラテラルムーブメントの一部として一般的に観察されます。Darktrace DETECTは、上記の活動がデバイスの通常の行動パターンからの逸脱であり、以下のモデルが侵害されたものであると理解しました:
Darktrace DETECT のモデル:
- Anomalous Connection / Anomalous DRSGetNCChanges Operation
- Anomalous Connection / New or Uncommon Service Control
- Anomalous Connection / Unusual Admin RDP Session
- Anomalous Connection / Unusual SMB Version 1 Connectivity
- Compliance / SMB Drive Write
- Device / Anomalous ITaskScheduler Activity
- Device / Attack and Recon Tools
- Device / Attack and Recon Tools In SMB
- Device / EXE Files Distributed to Multiple Devices
- Device / Suspicious Network Scan Activity
- Device / Increase in New RPC Services
- User / New Admin Credentials on Server
データ漏えい
攻撃の現段階では、Hiveアクターは様々な異なる方法を用いて感染したネットワーク上でデータ流出活動を行うことが知られています。米国サイバーセキュリティ・社会基盤安全保障庁 (CISA) は、「Hiveアクターは、RcloneとクラウドストレージサービスMega[.]nzを組み合わせて使用してデータを流出させている可能性が高い」と報告しています [4]。Darktrace DETECT は、ある顧客ネットワーク上のデバイスが、ユーザーエージェント "rclone/v1.57.0" で "w.apa.mega.co[.]nz" など Mega関連のエンドポイントにHTTP接続し、外部へと少なくとも3Gibが移動したことが観察されています(図3)。また、同じデバイスがSSL経由で、希少な外部IPである 158.51.85[.]157 に少なくとも3.6GBのデータを転送していることが確認されました。

別のケースでは、デバイスがSSH経由で珍しい外部エンドポイント93.115.27[.]71に16GB以上のデータをアップロードしていることが観測されました。このエンドポイントは、以前のビーコン活動で確認されており、これは流出イベントである可能性が高いことが示唆されました。
しかし、Hiveランサムウェアは、他のRaaSキットと同様に、その技術や機能が大きく異なる可能性があり、Hiveランサムウェアの攻撃においてデータ流出が常に存在するとは限らないことに注意することが重要です。Darktrace が検知したあるインシデントでは、顧客環境からデータが流出した形跡はなく、データ流出がHiveの実行者の目的の一部ではなかったことを示しています。
Darktrace DETECT のモデル:
- Anomalous Connection / Data Sent to Rare Domain
- Anomalous Connection / Lots of New Connections
- Anomalous Connection / Multiple HTTP POSTs to Rare Hostname
- Anomalous Connection / Suspicious Self-Signed SSL
- Anomalous Connection / Uncommon 1 GiB Outbound
- Device / New User Agent and New IP
- Unusual Activity / Unusual External Data to New Endpoints
- Unusual Activity / Unusual External Data Transfer
- Unusual Activity / Enhanced Unusual External Data Transfer
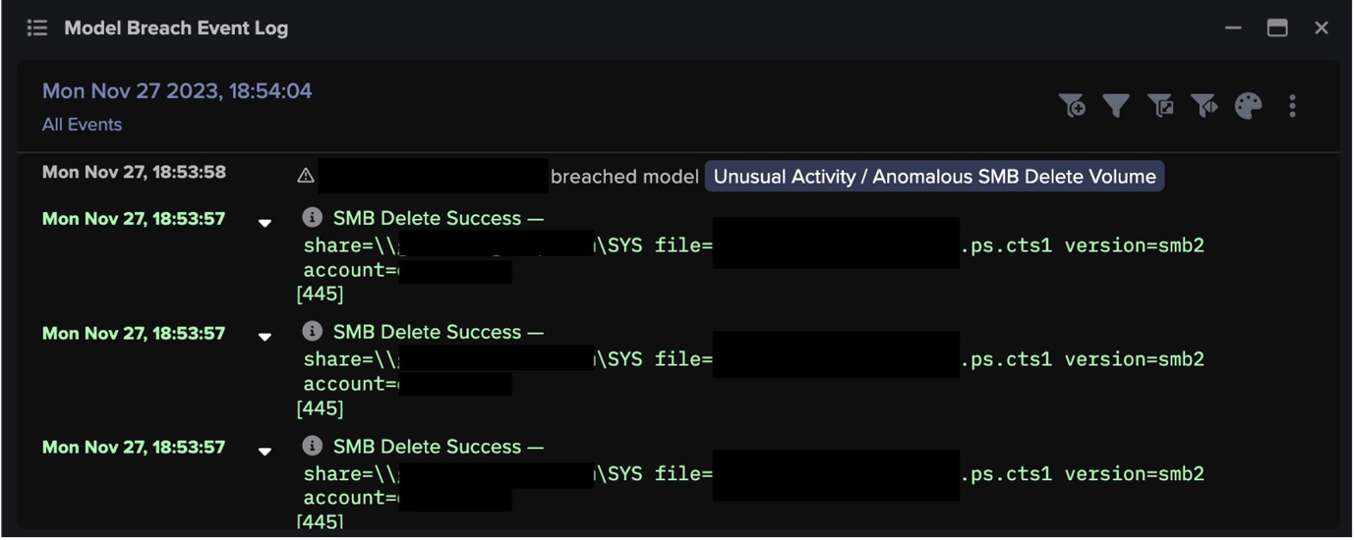
ランサムウェアの展開
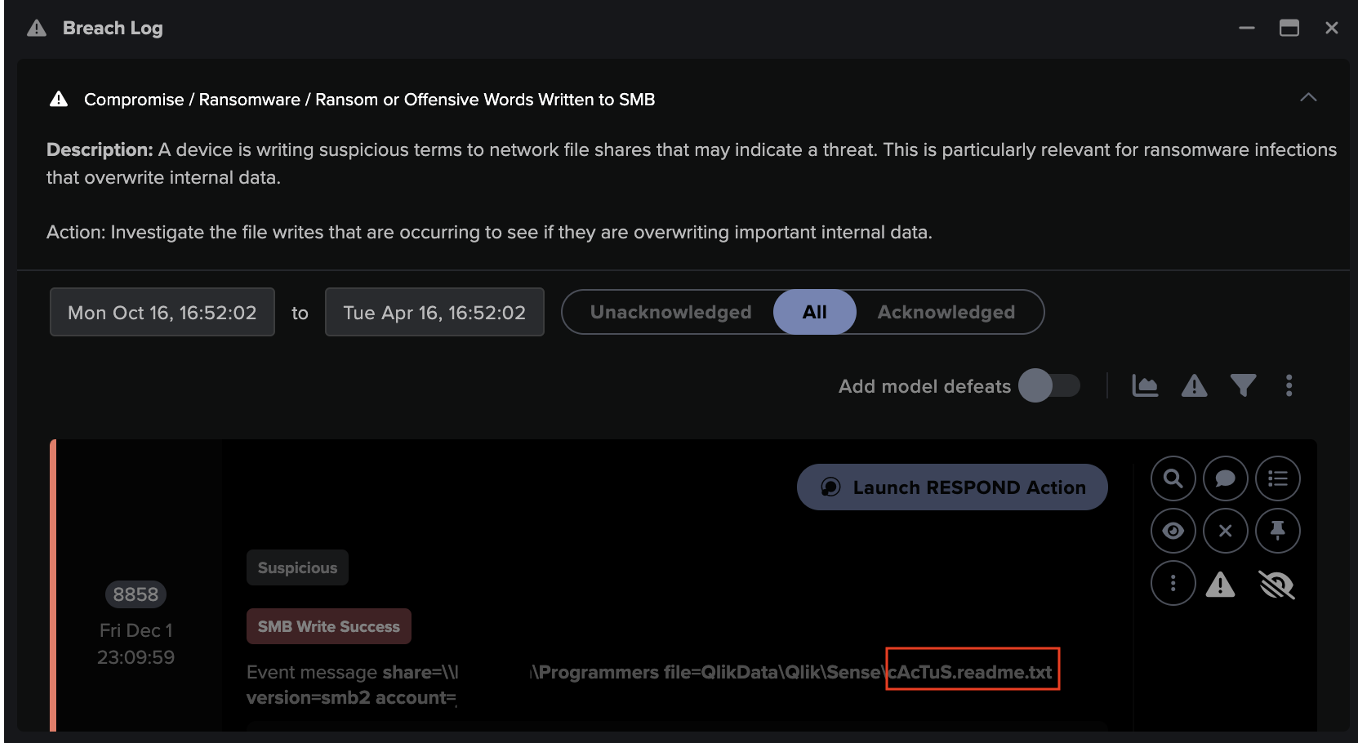
典型的なHiveランサムウェア攻撃の最終段階では、ランサムウェアのペイロードが展開され、感染したデバイス上のファイルを暗号化し始めます。あるお客様のネットワークで、Darktrace 、ドメインコントローラー(DC)に接続して「xxx.exe」という名前のファイルを読み込む複数のデバイスを検知しました。複数のソースが、このファイル名をHiveランサムウェアのペイロードと関連付けています。[5]
別の例ですが、Darktrace DETECTは、複数のデバイスが 194.156.90[.]25という珍しい外部の場所から実行ファイル「nua64.exe」および「nua64.dll」をダウンロードするのを観測しました。OSINTの調査により、このファイルがHiveランサムウェアに関連していることが判明しました。

この実行ファイルをダウンロードした直後、複数のデバイスで、ファイルの拡張子にランダムに生成された文字列を付加する、異常な量のファイル暗号化が行われていることが確認されました。
Hiveランサムウェアの初期バージョンでは、拡張子が「.hive」のファイルが暗号化されることが報告されていますが [7]、Darktraceは、暗号化されたファイルの拡張子が、部分的にランダム化されているものの、一貫して20文字で、正規表現 “[a-zA-Z0-9\-\_]{8}[\-\_]{1}[A-Za-z0-9\-\_]{11}” と一致していたことが複数のお客様によって確認されました。

ファイルの暗号化に成功すると、Hiveは「HOW_TO_DECRYPT.txt」と名付けられた身代金メモを、影響を受けた各ディレクトリに投下するようになります。通常、身代金要求書には、Hiveの「営業部」へのリンクと、流出が行われた場合には、攻撃者が要求が満たされない場合に流出したデータを公開すると脅す「HiveLeaks」サイトへのリンクが含まれています(図6)。 Darktrace で検知されたHiveランサムウェアのケースでは、複数のデバイスが「HiveLeaks」のTORドメインにコンタクトしようとする様子が観察されており、エンドポイントユーザーがランサムノートに記載されたリンクに従っていたことが示唆されています。

ファイル拡張子の例:
- 36C-AT9-_wm82GvBoCPC
- 36C-AT9--y6Z1G-RFHDT
- 36C-AT9-_x2x7FctFJ_q
- 36C-AT9-_zK16HRC3QiL
- 8KAIgoDP-wkQ5gnYGhrd
- kPemi_iF_11GRoa9vb29
- kPemi_iF_0RERIS1m7x8
- kPemi_iF_7u7e5zp6enp
- kPemi_iF_y4u7pB3d3f3
- U-9Xb0-k__T0U9NJPz-_
- U-9Xb0-k_6SkA8Njo5pa
- zm4RoSR1_5HMd_r4a5a9
Darktrace DETECT のモデル:
- Anomalous Connection / SMB Enumeration
- Anomalous Connection / Sustained MIME Type Conversion
- Anomalous Connection / Unusual Admin SMB Session
- Anomalous File / Internal / Additional Extension Appended to SMB File
- Compliance / SMB Drive Write
- Compromise / Ransomware / Suspicious SMB Activity
- Compromise / Ransomware / Ransom or Offensive Words Written to SMB
- Compromise / Ransomware / Possible Ransom Note Write
- Compromise / High Priority Tor2Web
- Compromise / Tor2Web
- Device / EXE Files Distributed to Multiple Devices
結論
Hiveランサムウェアの攻撃は、さまざまなアフィリエイトがさまざまな展開キットを使用して実行されるため、採用される戦術は異なる傾向にあり、新しいIoCが定期的に確認されています。さらに、2022年には、プログラミング言語Rustを使用してHiveの新しい亜種が作成されました。これはHiveの大幅なアップグレードであり、防御回避技術を向上させ、検知をさらに困難にしています [8]。
Hiveは、現在市場にある数多くのRaaSの1つに過ぎず、この市場は利用率とプレゼンテーションの多様性が高まる一方であると予想されます。 ランサムウェアがより身近になり、展開が容易になるにつれ、組織はランサムウェアをできるだけ早い段階で特定するための効率的なセキュリティ対策を導入することが不可欠となります。
Darktrace DETECTの自己学習型AIは、顧客ネットワークを理解し、組織のデジタルエステート全体で予想される行動パターンを学習します。このようなアノマリーベースのツールである Darktrace を使用すると、ルールやシグネチャ、既知のIoCに依存することなく、異常な動作や予期せぬ動作の自律検知を通じて新たな脅威を瞬時に特定することができます。
寄稿者:Emily Megan Lim(Cyber Analyst)、Hyeongyung Yeom(Senior Cyber Analyst & Analyst Team Lead)
付録
MITRE AT&CK マッピング
偵察
T1595.001 – Scanning IP Blocks
T1595.002 – Vulnerability Scanning
リソース開発
T1583.006 – Web Services
初期アクセス
T1078 – Valid Accounts
T1190 – Exploit Public-Facing Application
T1200 – Hardware Additions
実行
T1053.005 – Scheduled Task
T1059.001 – PowerShell
永続性/特権昇格
T1053.005 – Scheduled Task
T1078 – Valid Accounts
防衛回避
T1078 – Valid Accounts
T1207 – Rogue Domain Controller
T1550.002 – Pass the Hash
探索
T1018 – Remote System Discovery
T1046 – Network Service Discovery
T1083 – File and Directory Discovery
T1135 – Network Share Discovery
ラテラルムーブメント
T1021.001 – Remote Desktop Protocol
T1021.002 – SMB/Windows Admin Shares
T1021.003 – Distributed Component Object Model
T1080 – Taint Shared Content
T1210 – Exploitation of Remote Services
T1550.002 – Pass the Hash
T1570 – Lateral Tool Transfer
収集
T1185 – Man in the Browser
コマンド&コントロール
T1001 – Data Obfuscation
T1071 – Application Layer Protocol
T1071.001 – Web Protocols
T1090.003 – Multi-hop proxy
T1095 – Non-Application Layer Protocol
T1102.003 – One-Way Communication
T1571 – Non-Standard Port
持ち出し
T1041 – Exfiltration Over C2 Channel
T1567.002 – Exfiltration to Cloud Storage
影響
T1486 – Data Encrypted for Impact
T1489 – Service Stop
IoC一覧
23.81.246[.]84 - IP Address - Likely Malicious File Download Endpoint
146.70.87[.]132 - IP Address - Possible Ransomware Endpoint
5.199.162[.]220 - IP Address - C2 Endpoint
23.227.178[.]65 - IP Address - C2 Endpoint
46.166.161[.]68 - IP Address - C2 Endpoint
46.166.161[.]93 - IP Address - C2 Endpoint
93.115.25[.]139 - IP Address - C2 Endpoint
185.150.1117[.]189 - IP Address - C2 Endpoint
192.53.123[.]202 - IP Address - C2 Endpoint
209.133.223[.]164 - IP Address - Likely C2 Endpoint
cltrixworkspace1[.]com - Domain - C2 Endpoint
vpnupdaters[.]com - Domain - C2 Endpoint
93.115.27[.]71 - IP Address - Possible Exfiltration Endpoint
158.51.85[.]157 - IP Address - Possible Exfiltration Endpoint
w.api.mega.co[.]nz - Domain - Possible Exfiltration Endpoint
*.userstorage.mega.co[.]nz - Domain - Possible Exfiltration Endpoint
741cc67d2e75b6048e96db9d9e2e78bb9a327e87 - SHA1 Hash - Hive Ransomware File
2f9da37641b204ef2645661df9f075005e2295a5 - SHA1 Hash - Likely Hive Ransomware File
hiveleakdbtnp76ulyhi52eag6c6tyc3xw7ez7iqy6wc34gd2nekazyd[.]onion - TOR Domain - Likely Hive Endpoint
参考文献
[1] https://www.justice.gov/opa/pr/us-department-justice-disrupts-hive-ransomware-variant
[2] https://www.varonis.com/blog/hive-ransomware-analysis
[3] https://www.trendmicro.com/vinfo/us/security/news/ransomware-spotlight/ransomware-spotlight-hive
[4]https://www.cisa.gov/news-events/cybersecurity-advisories/aa22-321a
[5] https://www.trendmicro.com/en_us/research/22/c/nokoyawa-ransomware-possibly-related-to-hive-.html
[6] https://www.virustotal.com/gui/file/60f6a63e366e6729e97949622abd9de6d7988bba66f85a4ac8a52f99d3cb4764/detection
[7] https://heimdalsecurity.com/blog/what-is-hive-ransomware/
[8] https://www.microsoft.com/en-us/security/blog/2022/07/05/hive-ransomware-gets-upgrades-in-rust/































![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)