SaaS(Software-as-a-Service)の広範かつ迅速な採用により、ITチームにとって幅広いセキュリティリスクの可能性が新たに生じました。すぐに使える商用のソフトウェア(COTS: commercial off-the-shelf)と異なり、SaaSのセキュリティは最終顧客ではなくサードパーティベンダーが管理することが多くなっています。したがってセキュリティチームは、これらの環境に対して、状況が見えづらく管理しづらい中で苦労しなければならず、サイバー犯罪者はすばやく状況を利用して、ベンダーのEメールの侵害から内部アカウントの乗っ取りまで、クラウドベースの攻撃を次々と展開しています。
攻撃者はしばしば、同じドメイン上の複数のアカウントに対するアクセス権を得て、複数の角度から攻撃できるようにします。たとえば、数百通のメールを1つのアカウントから送信しつつ、別のアカウントで永続性を維持します。これによりハッカーは、SaaS環境のネイティブツールとともに外部ペイロードも利用して、複数の攻撃経路を試みることができます。
多要素認証(MFA)のような予防的な管理を行うことで、保護のレイヤーを1つ増やすことはできますが、ゼロトラストアプローチを迂回する多くのテクニックが存在します。リモートワークやフレキシブルな働き方は、今後もさまざまな地域と業界で多かれ少なかれ継続するため、企業は今すぐクラウドアーキテクチャのセキュリティ確保と、積極的なサイバーセキュリティ手法の開発に注力する必要があります。
このブログでは、ヨーロッパのある不動産会社を標的とした、複数の侵害されたMicrosoft 365アカウントを使用した持続的なサイバー攻撃を分析します。こうしたSaaSアカウント乗っ取りは急激に新たな標準となりつつありますが、業界全体ではいまだに誤解されているうえに、文書化も貧弱です。サイバーAIは、この侵入のすべての段階を、シグネチャや静的なルールを使用せずにリアルタイムで検知しました。
アカウントA、B: Microsoft 365アカウントの乗っ取り
この企業の環境には約5000台のデバイスと、1000のアクティブなSaaSアカウントがありました。次のタイムラインは、脅威アクターが5つの異なるユーザーのSaaSアカウントを利用して作戦を実行し、さらに最終日には他の複数のアカウントも不正使用した様子を示しています。

図1:3日間にわたって発生した感染の連鎖4日目にも攻撃者による試行がありましたが、失敗しました。
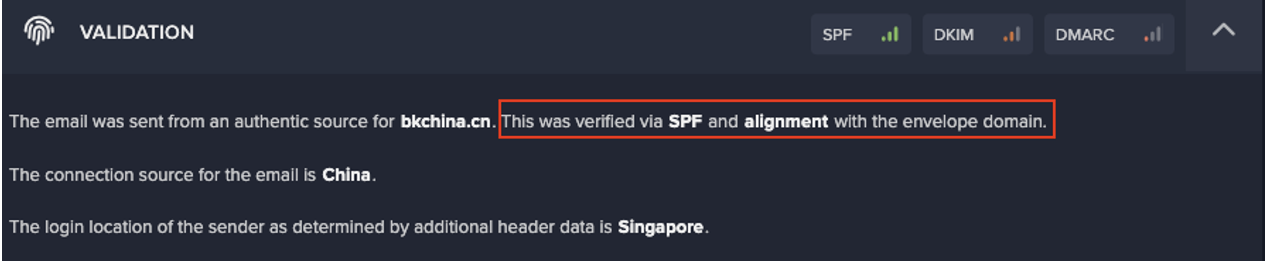
この行為者は、最初に少なくとも2つのSaaS認証情報(ここでは単にアカウントAとアカウントBと呼ぶことにします)を侵害し、おそらくVPNを使用して、いくつかの通常とは異なる地理的位置からログインしました。Darktraceはこれを、SaaSアカウントに対する不審なログインイベントとして検知しました。
アカウントAは、攻撃者は顧客の情報が含まれると思われるファイルをプレビューしている様子がみられましたが、その他のフォローアップアクティビティは行っていませんでした。アカウントBでは、当初の侵害から3時間後に受信トレイルールが新たに設定され、重大度の高い警告が発生しました。
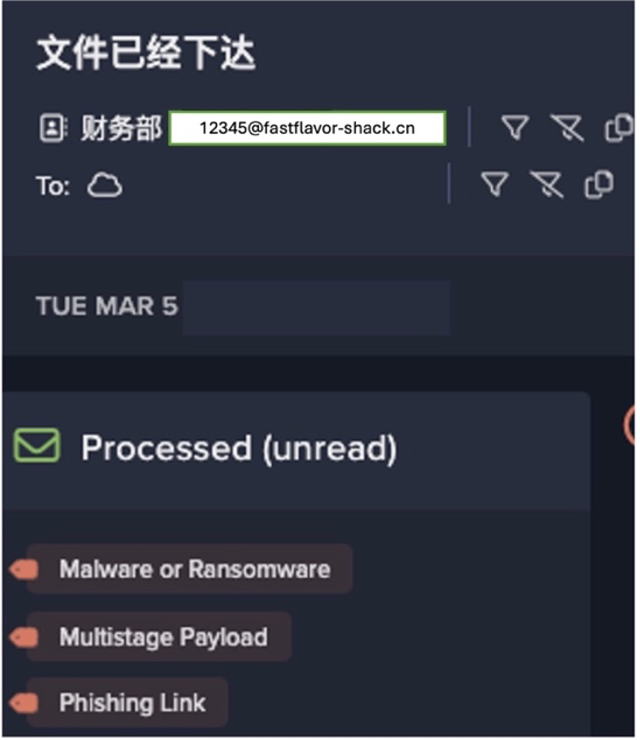
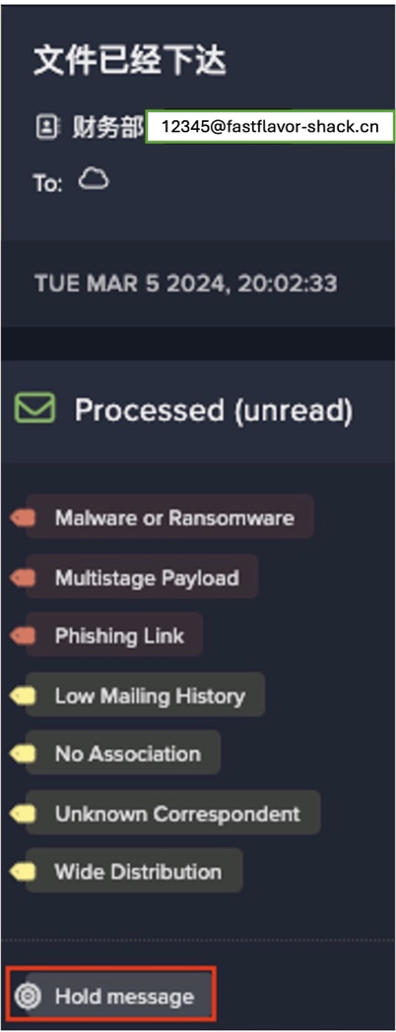
この頃、脅威アクターはいくつかのフィッシングメールをアカウントBから送信しました。無害で本物らしいOneDriveフォルダを共有すると見せかけたメールです。このリンクは、おそらく次のような偽のMicrosoftログインページに通じていて、被害者のアカウントを記録して攻撃者に直接送信する機能を備えていたものと考えられています。

図2:一見正しいMicrosoftログインページ
フィッシングの試みは、DarktraceのEメールセキュリティテクノロジーであるDarktrace Emailによって検知されました。Darktrace Emailは当時パッシブモードだったため、こうした脅威のあるメールに対処するようには設定されていませんでした。しかし、きわめて異常な送信数増加と、不審なログイン場所の組み合わせを考えれば、おそらくすべてのメールを自動的に差し止め、攻撃の影響を緩和することができていたでしょう。
攻撃者はやがてアカウントBからロックアウトされました。その後攻撃者はレガシーユーザーエージェントを使用して、アカウントに対して強制されているMFAを回避しようとしましたが、失敗しました。Darktraceはこれを疑わしいログインとして検知し、この試みをブロックしました。
アカウントC、D、E: 脅威の進展
翌日、攻撃者は、同一のASN(自律システム番号)から新しいアカウント(アカウントC)にログインしました。これは、このアカウントがOneDriveフィッシングEメールに感染したことを示しています。言い換えると、攻撃者はアカウントBを利用して、社内の新しいユーザーを侵害し、複数の侵入ポイントを確保したことになります。
Darktrace detected each stage of this, piecing together the different events into one meaningful security narrative.

図3:アカウントC、D、Eの異常なアクティビティ
そして、アカウントCを使用して、連絡先情報が含まれていると思われるファイルのプレビューが行われました。
翌日ログインしようとしたときにアカウントCにから締め出されると、ハッカーはさらに、以前のフィッシングで乗っ取った2つのアカウント(アカウントDおよびE)に入り込みました。しかし、普段とは異なるログインを行い、それと同時に新たな受信トレイルールを作成するたびに、アラートが生成され、ハッカーは締め出されました。
AからZ: 悪事の終わり
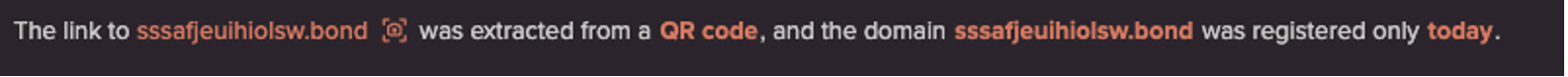
選択肢がなくなったため、攻撃者はアカウントAに戻り、新しい受信トレイルールを作成して、Microsoft以外のクラウドストレージドメイン(Tresorit)へのリンクを記載した新たなフィッシングEメールを送信しました。Darktraceは再びこれを、普段とは大きく異なる動作として認識し、ハッカーは速やかにアカウントから締め出されました。
この一連のアクティビティの間に、Darktraceは疑わしいASNの1つによるMicrosoft Teamsセッションも観測しました。これはおそらくソーシャルエンジニアリングの試みで、別の攻撃経路の可能性があると考えられました。Microsoft Teamsは、インスタントメッセージ経由の悪意あるリンクの共有、機密情報の抽出、チャット機能を使用した社内外へのスパム送信などに利用されていたおそれがあります。
脅威アクターはさらにこれを使用してさまざまなアプリケーションやアカウントに展開していった可能性もあります。この企業がサイロ化したセキュリティアプローチを使用していて(クラウド、SaaS、メール、エンドポイントに異なるツールを採用していた)、悪意のあるクロスプラットフォームの動きについていけないと想定していればそうしたでしょう。
翌日、攻撃者は再び複数のアカウントにわたってログインを試みましたが失敗しました。Cyber AIがすべての異常な活動を、発生源にかかわらず発見し、即座にセキュリティチームに警告したのです。
SaaS攻撃を詳しく分析する
複数アカウントの侵害は非常に持続性が高く、従来のセキュリティツールでは識別が難しい場合があります。ハッカーは、顧客の既存のメールセキュリティ製品を回避するために複数の戦術を利用しました。
- アカウントAとアカウントBの2つの認証情報を使用することで、ハッカーは目立たずに活動し、1つのアカウントであまりに大きな疑いを持たれずに済みました。アカウントAは、他の経路が枯渇するまで沈黙を保ちました。
- アクティビティは、少なくとも3つの異なる地理的ロケーションにある複数のASNから、おそらくVPNを使用して生成されました。1つはアフリカにあり、ほとんどのアクティビティの発生源となっていました。2つは北米にありましたが、その中には広く使われているASNもあり、これはこの顧客にとって非常に珍しいことでした。
- 攻撃者は最後のEメールまですべてMicrosoftサービスを使用しました。これは、ゲートウェイによって捕捉されてしまうリンクを使うのではなく、‘live off the land’(環境に寄生する)方法を選択したことになります。
- 攻撃者は、最後の行動としてMicrosoft Teamsにログインしました。これは一見無害に映るイベントですが、検知されないまま、アカウントをさらに侵害したり水平移動したりするために利用できる可能性があります。
Darktraceは攻撃のすべての段階を識別し(その中には異常なASNの特定も含まれています)、Cyber AI Analystによる自動的かつ詳細な調査を開始しました。そのため、この企業は損害を被る前に対処することができました。

図4:DarktraceのSaaS Consoleは、さまざまなアプリケーションの概要を明確に表示
SaaSセキュリティのABC
各種のアカウントを用いて攻撃を実行しつつ、1つのアカウントで存在を持続させるアプローチによって、この侵入は長引きました。近い将来、このような戦術が再び観測されるでしょう。
複数のアカウント、攻撃経路、攻撃者IPアドレスを用いる攻撃に関連した大量の要素を追跡するのは、深刻な課題です。このような状況においては、さまざまなアプリケーションにわたるアクティビティを検知し、デジタルエンタープライズ全体の、統一された包括的な理解を形成することのできるセキュリティソリューションを導入することがきわめて重要です。
このケースでは有効化されていませんでしたが、 Darktrace SaaSが導入されていれば、Darktrace SaaSの自動対処により通常の動作が強制されることで、ハッカーによる悪意のあるインフラからのログインや、新しい受信トレイルールの作成など異常なSaaSアクションの実行を防げたはずでした。
この侵入事例の後、この企業はDarktrace SaaSの導入を決定しました。これにより、クラウドセキュリティリスクが緩和され、機密データの損失と評判の毀損から保護されています。
この脅威事例についての考察はDarktraceアナリストDaniel Gentleが協力しました。
Darktraceによるモデル検知:
- SaaS / Compromise / Unusual Login and New Email Rule
- SaaS / Compliance / New Email Rule
- SaaS / Unusual Activity / Unusual External Source for SaaS Credential Use
- SaaS / Access / Suspicious Login Attempt
- Antigena Email: Unusual Login Location + Sender Surge