クラウドの広範な利用がビジネスを変革し続ける一方で、サイバーセキュリティソリューションもそれに追いつこうと競争しています。今日のマルチクラウド環境は、複雑さと可視性のギャップをもたらし、攻撃者に門戸を開いています。クラウドは動的な性質を持っているため、これらの盲点は常に変化しています。また、クラウドの拡張性を考えると、ちょっとした設定ミスなどの単純なミスが、不釣り合いなほど大規模なセキュリティインシデントにつながる可能性もあります。
企業はもはや、バラバラのツールや静的でポイント・イン・タイムのリスクビューに頼る余裕はありません。クラウドは本質的に複雑であり、セキュリティツールはその複雑さを単純化することを目的とするのではなく、そのスケールと複雑さを利用することで、そのメリットを活かすべきです。
クラウドが高度にカスタマイズ可能で、クラウドごとに異なる世界では、クラウドセキュリティに対する画一的なアプローチでは、個々の環境のニュアンスに対応できません。このブログでは、独自の組織を機械学習・理解するAIを活用することで、セキュリティチームがクラウドにおけるセキュリティ確保に必要な可視性、理解、リアルタイムの検知と対応をどのように実現できるかを探ります。
セキュリティは行動にかかっている
一般的に、クラウドのセキュリティは2つの陣営のどちらかに分類される傾向があります:
- ほとんどのクラウドセキュリティポスチャ管理(CSPM)ベンダーが採用しているエージェントレスのアプローチは、運用の中断を最小限に抑え、迅速かつ容易なインストールを約束する
- エージェントベースのアプローチは、より細かい粒度を提供するが、セットアップに時間がかかり、コストがかかる可能性がある
どちらのアプローチにも固有の欠点があります。エージェントレスのソリューションは通常、悪意のあるインサイダーやゼロデイエクスプロイトなど、新たな脅威を検知するために必要なリアルタイムの認識をセキュリティチームに提供しません。一方、エージェントベースのソリューションでは、到達範囲と拡張性に限界があり、通常、セキュリティチームがすでにリスクがあることを知っているクラウドの領域に導入されるため、新たな洞察が得られず、死角がそのまま残ってしまいます。
そのため、今日のクラウドセキュリティはジレンマに陥っているようです。そして、どちらの方法にも共通するもう1つの問題は、これらの製品では、何か問題が発生したときにアナリストに警告を発することはできても、本格的な対応を行う能力がないということです。自動対処を謳う新しいソリューションでさえ、通常はアラートの送信やチケットの開設のプロセスを自動化することを指していることが多いのです。
迅速な対処は見果てぬ夢
組織にとってクラウドが非常に便利で魅力的なのは、スピード、敏捷性、可用性、スケールといった同じ属性が、攻撃者にとっても対称的に魅力的だからです。クラウド上でサイバー攻撃が急速に展開される場合、単にチケットを発行し、相手側の誰かが対応してくれるのを待つだけでは不十分です(むしろ、あまりに多くのチケットに対応することは、トリアージや調査をかえって停滞させ、対応を早めるどころか遅らせることになりかねません)。有用なレスポンスの最終的なテストは、セキュリティチームがそのレスポンス機能を使いたがるかどうかに帰着します。セキュリティチームが中断を恐れて、一向にオンにならないレスポンス機能は、まったく的外れなのです。
効果的な対処には、いつ、どのように対応すべきかを理解することと、対応を実行するためのクラウドネイティブなメカニズムが必要です。これは3つのステップに分けることができます:
ステップ1:可視性を超える:リアルタイム理解
今日の静的なクラウドセキュリティソリューションは、統合やインストールの前に環境のスナップショットを提供します。静的な洞察は、導入前のコントロールの検証と設定に役立ちますが、クラウド移行に関連する真のリスクは後から現れるのです。
適切な対処を推進するためには、セキュリティソリューションが、組織のクラウド環境について一般的な感覚ではなく、リアルタイムで全体的なビューを提供する必要があります。
クラウドに関連するリスクを理解するには、単に可視化するだけでは不十分です。環境全体の様々な行動パターンを理解し、アプリケーションやワークロードのアーキテクチャのニュアンスを知る必要があります。誰が何にアクセスできるのか?通常、どの仮想マシンが互いに接続しているのか?このコンテナは期待通りに動作しているか?この新しいLambda関数は期待通りか?などです。
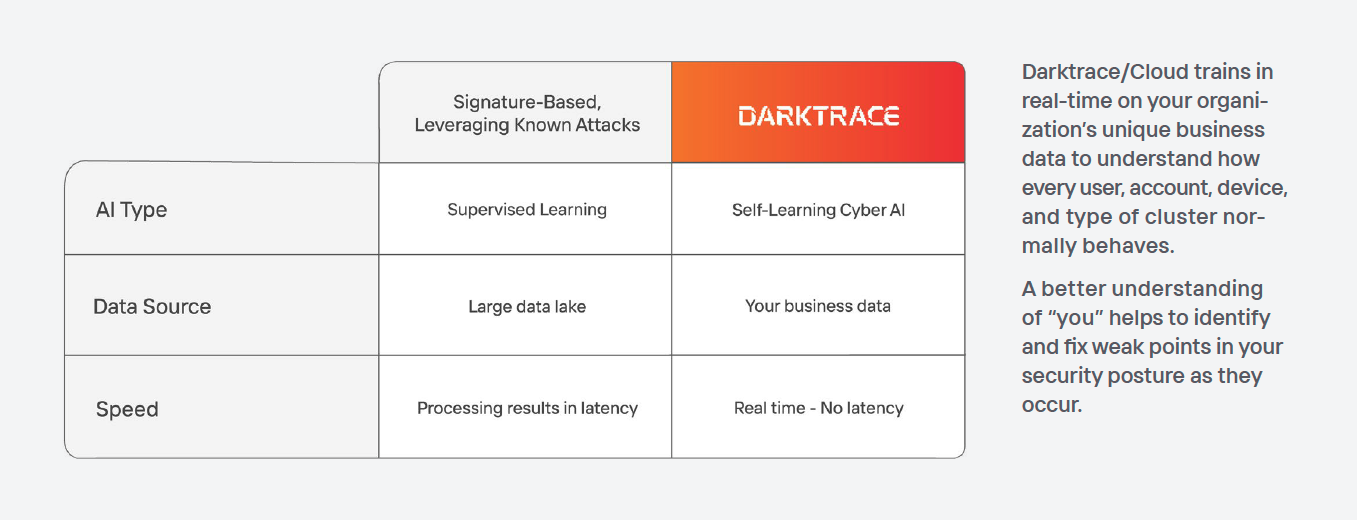
Darktrace/Cloudは、自己学習型AIを使用して、クラウドネットワーク、アーキテクチャ、管理の各レイヤーでお客様独自の組織を学習し、理解します。膨大な量のデータからパターンを認識するAIの能力は、セキュリティチームにクラウド環境で今何が起きているのかについての真の洞察を与えるユニークな立場にあります。
AIの導入や具体的な使用方法は(個々の組織の環境に基づいて)それぞれ異なりますが、導入ライフサイクル全体を通じてセキュリティチームとDevOpsチームを連携させるクラウドフットプリントのアーキテクチャビューが常に含まれます。
あるベータ版の顧客は、Darktrace/Cloudを導入した際の感想として、次のように述べています:
暗い部屋で電気のスイッチを入れるような感覚です。
ステップ2:検知はコンテキストを適用する必要がある
どのユーザーがどのリソースに接続しているのか、誰が特定のワークロードにアクセスできるのか、グループ、重複、権限など、クラウドにおける「正常」を正確に理解することで、ソリューションは、普通でないことを発見するよう自らに教え込むことで、対処に向けて前進します。
クラウドセキュリティ体制の静的なスナップショットでは、パッチが適用されていない脆弱性や問題のある誤設定が表示されますが、洞察はそこで終わってしまいます。静的なビューとポイントインタイムの可視性に基づくクラウドセキュリティソリューションでは、最終目標であるリアルタイムの脅威を発見する能力を提供するために、点と点をつなぐことはできません。
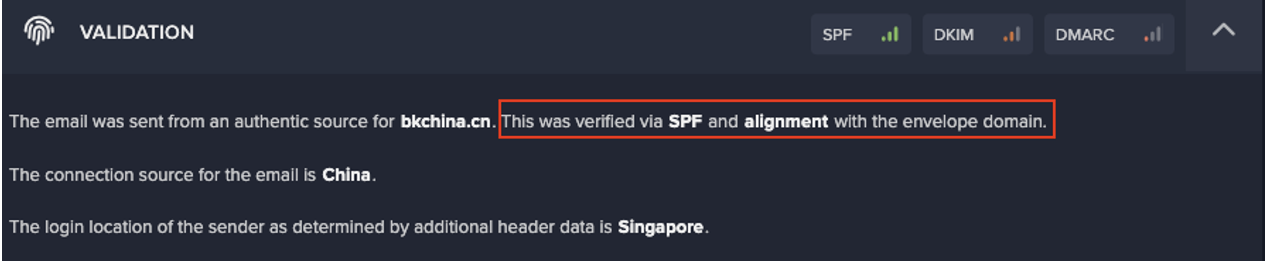
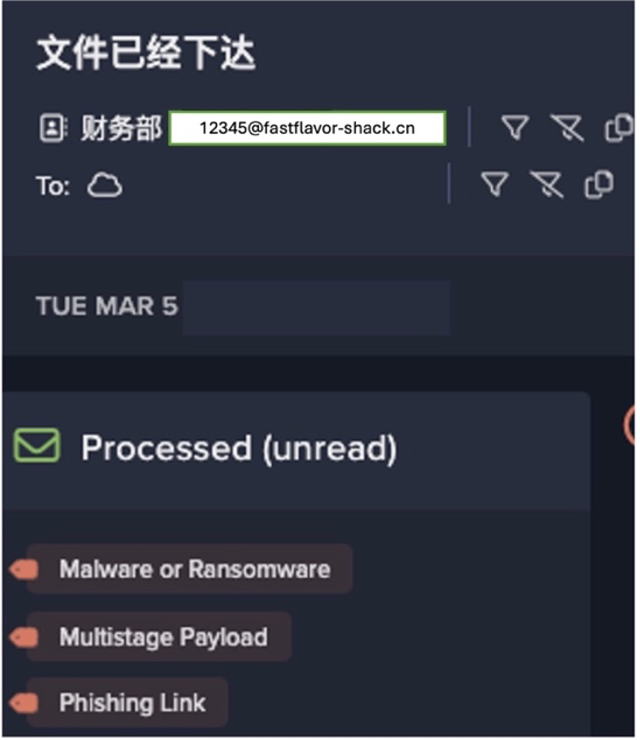
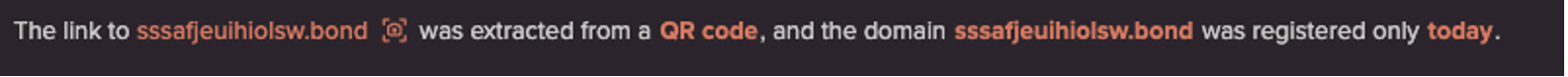
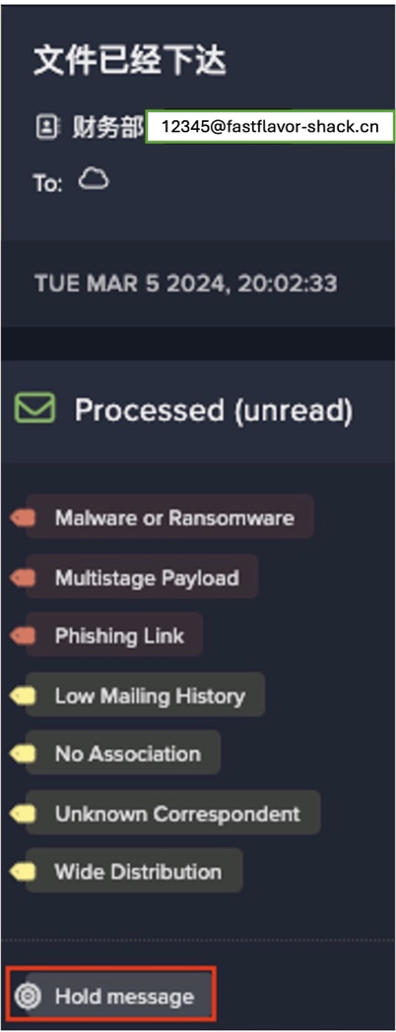
Darktrace/Cloudは、脆弱性や設定ミスに対する有意義な洞察を提供するだけでなく、そのリアルタイムの理解により、新たな脅威の検知も可能にします。また、Darktrace/Network や Darktrace/Email のような他の Darktrace モジュールと組み合わせることで、これらの調査結果をビジネスコンテキストで充実させ、新たな脅威を数秒で検知してシャットダウンします。それは、クラウドのフットプリントと、それがオンプレミスのインフラ、エンドポイント、アプリケーションとどのように相互作用するかを理解するためのビジネス全体のコンテキストです。
ステップ3:対処は真に自律的でなければならない
Darktrace/Cloudは、貴社独自のクラウドフットプリントを貴社ビジネスの文脈で理解することで、今すぐ対処が必要な異常事態が発生したことを独自に検知します。
お客様の環境を理解するためにAIを使用することで、真に自律的で正確なクラウドネイティブの対処が可能になります。プラットフォームは、通常の業務を中断することなく、脅威となる行動のみを停止させるため、ピンポイントかつ的を絞った行動を取ることができます。
プラットフォームはクラウドアーキテクチャを完全に理解しているため、どのようなクラウドネイティブのメカニズムが実際の対処を開始するために自由に使えるかも把握しています。自動化されたリアルタイムのレスポンスには、EC2インスタンスのデタッチや、リスクの高い資産を封じ込めるためのセキュリティグループの適用など、クラウドネイティブなアクションが含まれます。
実際に体験する
Darktrace は、Darktrace/Cloudの30日間無償トライアルを提供しています。このトライアルは、簡単なインストールとマルチクラウド環境に関するこれまでにない理解を組み合わせたものです。ご興味のある方はこちらをクリックしてご登録ください。