サマリー:
- エアギャップはサイバーリスクを低減するが、現代のサイバー攻撃を防ぐことはできない
- エアギャップされたネットワークを可視化することは、防御が完璧であると仮定して可視性がゼロになるよりも優れている
- Darktrace は、エアギャップの完全性を損なうことなく、可視性とレジリエンスを提供することができる
「エアギャップ」とは何ですか?
情報技術(IT)は、エンドポイントやメールシステムからクラウドやハイブリッドインフラまで、デジタル情報のフローを流すために、外部と流動的に接続する必要があります。一方で、このような高度な接続性は、ITシステムをサイバー攻撃に対して特に脆弱なものにしています。
Operational technology (OT), which controls the operations of physical processes, are considerably more sensitive. OT often relies on a high degree of regularity to maintain continuity of operations. Even the slightest disturbance can lead to disastrous results. Just a few seconds of delay on a programmable logic controller (PLC), for example, can significantly disrupt a manufacturing assembly line, leading to downtime at a considerable cost. In worst-case scenarios, disruptions to OT can even threaten human safety.
エアギャップとは、データを手動で転送しない限り、OT環境に出入りできない「デジタル堀」(Digital Moat) のことです。
OTを導入している組織では、従来、このITとOTの対立を調整するために、両者を完全に分離することを試みてきました。基本的には、ITが得意とする通信やデータ転送を高速で行い、人々が互いにつながり、情報やアプリケーションに効率的にアクセスできるようにする、という考え方です。しかし同時に、ITとOTの間にエアギャップを設け、ITシステムに入り込んだサイバー脅威が、機密性が高くミッションクリティカルなOTシステムに横展開しないようにもします。このエアギャップは本質的に「デジタル堀」であり、手動で転送しない限り、データはOT環境に出入りすることができません。
エアギャップの限界
エアギャップのアプローチは理にかなっていますが、完璧とは言い難いものです。まず、完全にエアギャップされたシステムを持っていると思っている多くの組織が、実際には未知のIT/OTコンバージェンスポイント、つまりITとOTのネットワーク間の接続に気づいていないことがあるのです。
今日、多くの企業がIT/OTの融合を意図的に取り入れ、しばしばインダストリー4.0と呼ばれるようなOTのデジタル変革のメリットを享受しています。例えば、産業用クラウド(またはICSaaS)、産業用IoT(IIoT)、その他のタイプのサイバーフィジカルシステムは、従来のOTの形態と比較して、効率の向上と機能の拡張を提供します。また、IT/OTの融合は、プロセスをよりシンプルで効率的にすることができるため、人的資本の不足を理由にIT/OTの融合を受け入れる組織もあります。
たとえ組織が真のエアギャップを有していたとしても(ITとOT環境を完全に可視化しなければ確認することはほぼ不可能)、攻撃者が「エアギャップを飛び越える」ための様々な方法が存在するのが実情です。したがって、ITとOTのエコシステムを一枚のガラスで完全に可視化することは、OTの安全確保を目指す組織にとって不可欠です。これは、ITとOTの融合点を明らかにし、そもそもエアギャップが存在することを検証するためだけでなく、攻撃がエアギャップをすり抜けるタイミングを確認するためでもあります。
.png)
エアギャップの攻撃ベクトル
完璧なエアギャップであっても、以下を含む(ただし、これに限定されない)様々な異なる攻撃ベクトルに対して脆弱です:
- 物理的な侵害:敵は物理的なセキュリティをバイパスして、エアギャップされたネットワークデバイスに直接アクセスすることができます。物理的なアクセスは、最も効果的で明白な手法です。
- 内部脅威:組織の一員であり、エアギャップされた安全なシステムにアクセスできる者が、意図的または非意図的にシステムを侵害すること
- Supply chain compromise: A vendor with legitimate access to air-gapped systems unwittingly is compromised and brings infected devices into a network.
- 設定の誤り:アクセス制御やアクセス許可の設定ミスにより、攻撃者がネットワーク上の別のデバイスを経由してエアギャップシステムにアクセスすることができます。
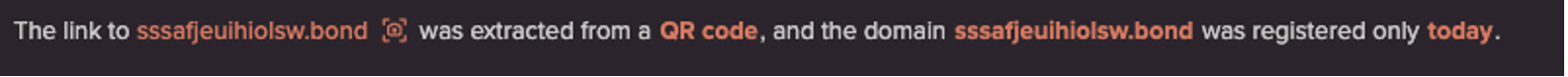
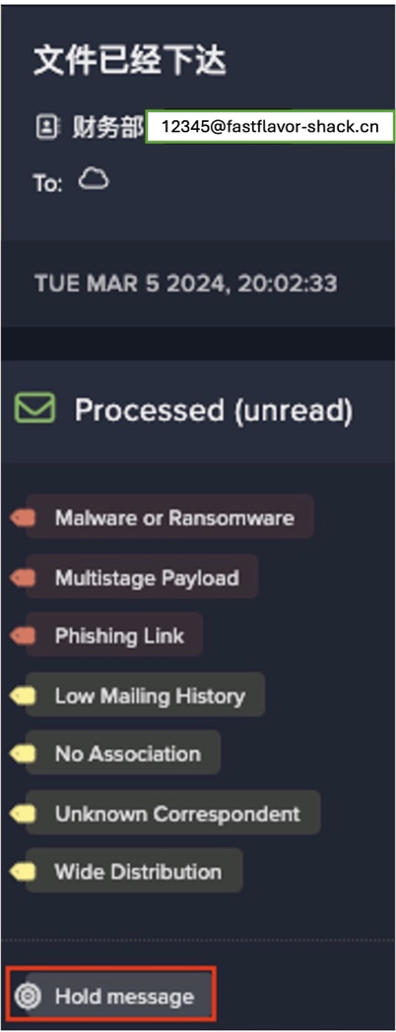
- ソーシャルエンジニアリング(メディアドロップ):攻撃者が悪意のあるUSB/メディアドロップを成功させ、従業員がそのメディアをエアギャップシステム内で使用した場合、ネットワークが侵害される可能性があります。
- その他の高度な戦術:熱操作、隠された表面振動、LED、超音波通信、無線信号、磁場など、ベングリオン大学の研究者が記録し、実証した高度な戦術の数々です。
エアギャップ式システムの脆弱性
熱操作や磁場などの高度な技術・戦術・手順(TTP)の影響を受けやすいことはもちろんですが、空中に設置された環境に関連するより一般的な脆弱性として、パッチ未適用のシステムが気づかれない、ネットワークトラフィックを可視化できない、潜在的に悪意のある機器がネットワーク上に検知されない、ネットワーク内で取り外し可能メディアが物理的に接続されるといった要因が挙げられます。
ひとたび攻撃がOTシステム内部に及べば、エアギャップの有無にかかわらず、その結果は悲惨なものになる可能性があります。しかし、エアギャップの存在が、インシデント発生時の対処や修復に要する時間にどのような影響を及ぼすかは、検討する価値があります。例えば、エアギャップの存在は、インシデント対応ベンダーがデジタルフォレンジックと対応のためにネットワークにアクセスする能力を著しく制限する可能性があります。
エアギャップを飛び越えるクレムリンのハッカー達
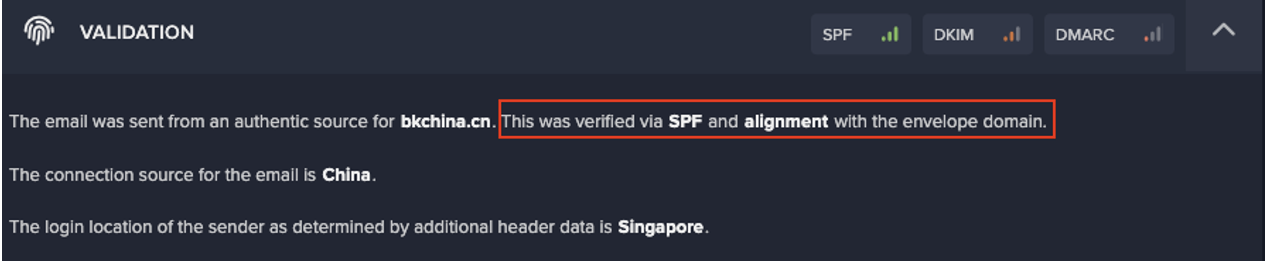
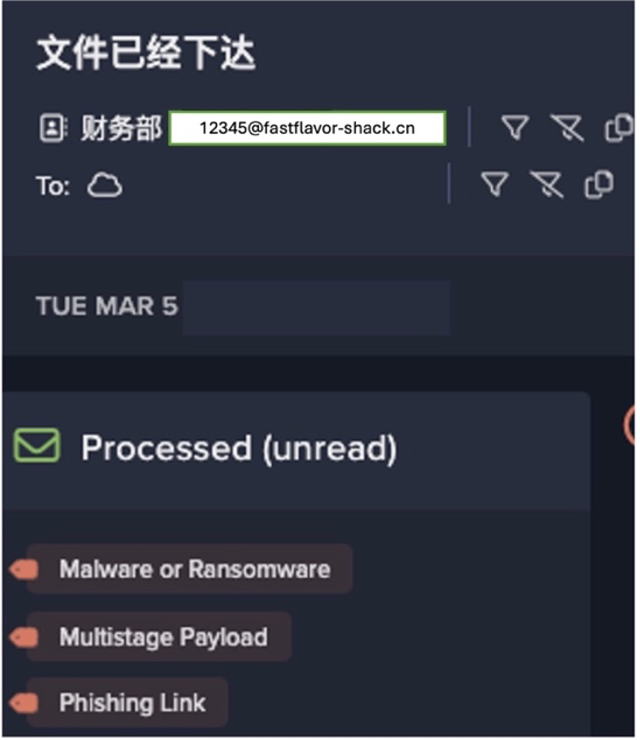
2018年、米国国土安全保障省(DHS)は、DragonflyとEnergetic Bearとして知られるロシアの脅威アクターが使用するTTPを記録したアラートを発表しました。さらなる報告では、これらのグループが「エアギャップを飛び越え」、さらに気になることに、好きなタイミングで送電網を無効化する能力を獲得したと主張したのです。
これらの攻撃者は、スピアフィッシングメールや水飲み場攻撃を通じてベンダーやサプライヤーを標的とし、エネルギー部門やその他の重要なインフラ部門における機密性の高いエアギャップシステムへのアクセスを成功させました。これらのベンダーは、エアギャップシステムに合法的にアクセスすることができ、パッチの配布などのサポートサービスを提供する際に、意図せずこれらのシステムに感染させてしまったのです。
このインシデントは、たとえ機密性の高いOTシステムがデジタル的に完全に隔離されていたとしても、この強固なエアギャップでは、あらゆるシステムの最大の脆弱性の一つであるヒューマンエラーを完全に排除できないことを明らかにしました。電磁波を除去するためにファラデーケージを作るという極端な方法をとったとしても、ヒューマンエラーは依然として存在するのです。DragonflyとEnergetic Bearがサプライヤーを騙すために使った手口に見られるように、エアギャップされたシステムは、人間の脆弱性を突くソーシャルエンジニアリングに対して依然として脆弱なのです。
理想的なのは、攻撃がサプライヤー、無線信号、電磁波のいずれによって引き起こされたかに関係なく、攻撃を識別できる技術です。自己学習型AIは、デバイス、人間、ネットワークの通常の「生活パターン」からの微妙な逸脱を発見することで、脅威の発生源や原因に関係なく、最も微妙な形の脅威的行動もその発生時に検知します。
エアギャップ環境向けのDarktrace/OT
エアギャップ環境向けのDarktrace/OT は、エアギャップシステムに直接配備される物理アプライアンスです。OT ネットワークからの生のデジタルデータを使用して、通常の生活パターンを理解します。Darktrace/OT は、第三者のサポートなしに AI が自己の生得的理解を構築するため、外部ソースからのデータまたは脅威フィードを一切必要としません。
データ処理と分析はすべてDarktrace アプライアンス上でローカルに実行されるため、Darktrace がインターネットに接続されている必要はありません。その結果、Darktrace/OTは、エアギャップまたは高度にセグメント化されたネットワークに対して、その完全性を損なうことなく可視性と脅威の検知を提供します。人間や機械が最も微妙な形の脅威的行動を示した場合、このソリューションはリアルタイムでこれを明らかにすることができます。
セキュリティ担当者は、Web ブラウザと暗号化された HTTPS を使用して、ネットワーク内のどこからでも、組織のネットワークポリシーに沿って、Darktrace アラートに安全にアクセスすることができます。

この展開で、 Darktraceは他のDarktrace/OT の展開で実証された、以下を含むすべての重要な洞察を提供します(ただし、これらに限定されません):
- エアギャップ環境における未知のIT/OT融合ポイントを含む、あらゆるIT/OTコンバージェンスポイントを照らし出す。
- すべてのPurdueレベルからフィールドコントローラーレベルまでのOTネットワークの可視性
- OTアセットインベントリー
- CVEトラッキング
- ネットワーク上の新しいデバイス、最初に見たデバイス、最後に見たアクティブなデバイスを識別
- ITチーム、セキュリティ担当者、オペレーター、エンジニアが読みやすい脅威対処とインシデントレポート
そもそもエアギャップがあるのかどうかを検証し、IT/OT環境の進化に合わせてエアギャップを維持しようとする組織は、Darktraceの自己学習型AIが提供する包括的な可視性と継続的な状況認識から大きな恩恵を受けることができます。また、ITとOTの融合のメリットを享受するためにエアギャップに穴を開けたいと考えている組織は、自己学習型AIによる警戒心が、すり抜けるサイバー攻撃を発見することに気づくでしょう。
IIoTの導入や本格的なDMZの構築など、組織の目標が何であれ、「あなた」を学ぶことによって、Darktraceの自己学習型AIは、安全かつセキュアにその目標を達成できるように支援します。
Daniel Simonds と Oakley Cox の貢献に感謝します。