VIPなりすましとは?
VIP impersonation involves a threat actor impersonating a trusted, prominent figure at an organization in an attempt to solicit sensitive information from an employee.
VIPへのなりすましは、セキュリティチームにとって優先順位の高い問題ですが、そのリスクを正確に評価することは難しく、また、そのリスクが他のタイプの侵害よりも重大であるかどうかを判断することも困難です。このブログでは、Darktrace/Email™を導入しているさまざまなお客様を対象に、なりすましの標的となる個人のパターンを調査し、これらの標的の優先順位が、重要な資産への攻撃経路を保護することに重点を置いているセキュリティチームの姿勢と一致しているかどうかを評価します。
セキュリティチームはVIPなりすましをどのように阻止するか?
組織内のVIPエンティティの保護は、セキュリティチームにとって長い間、伝統的な焦点でした。VIPは目立つ存在であるため、重要な資産への最大のアクセス権を持っており、サイバー脅威の格好の標的であるという前提があるのです。
Eメールは依然として攻撃の主要なベクトルであり、侵害の90%以上が悪意のあるEメールに起因しています。しかし、Eメールベースの攻撃の力学は変化しています。生成AIの普及により、敵対者は最小限のエラーで超リアルなEメールを作成できるようになり、参入障壁が低くなっています。
このような動きを踏まえると、どのようなエンティティ(VIP/非VIP)がEメールを介して脅威アクターに最も狙われているのでしょうか?そしてさらに重要なことは、どのエンティティ(VIP/非VIP)が侵害に成功した場合、より価値があるかということです。
VIPには2種類が存在:
1. Eメールやフィッシングについて言及する場合、VIPとは組織内で世間によく知られているユーザーのことである。
2. 攻撃経路について言及する場合、VIPとは、一般に知られており、非常に特権的な資産にアクセスできる組織内のユーザーを指す。
すべての重要なユーザーが重要な資産にアクセスできるわけではなく、重要な資産にアクセスできるすべてのユーザーが重要なわけでもありません。
DarktraceによるVIPなりすましの分析
私たちは、多様な組織を網羅する大規模かつランダムな集合から、20の顧客の展開における攻撃経路とフィッシング試行のパターンを分析しました。
攻撃経路を理解する
我々の観察によると、難易度の低い攻撃経路の57%はVIPエンティティから発生しているのに対し、重要な資産やエンティティに向かう難易度の低い攻撃経路の43%はVIP以外のユーザーから発生していることが明らかになりました。このことは、攻撃者が重要な資産に到達する唯一の方法はVIPを標的とすることではなく、VIP以外のユーザーも考慮しなければならないことを意味します。
サンプル数が少ないため、すべての顧客について統計的な有意性を立証することはできませんが、無作為に選択されたことで、他の環境に対するこれらの調査結果を一般化する可能性については信じることができます。
フィッシングの試み
これらの顧客に送信されたEメール全体の平均1.35%に、フィッシングや何らかのなりすましに関連する著しく悪質な性質が見られました。驚くべきことに、これらの悪意のあるメールの約半数(49.6%)がVIPに向けられ、残りは非VIPに向けられたものでした。攻撃経路は、VIP以外も重要な資産を標的とする潜在的な侵入口として機能することを示しているため、このほぼ均等な割合は注目に値します。

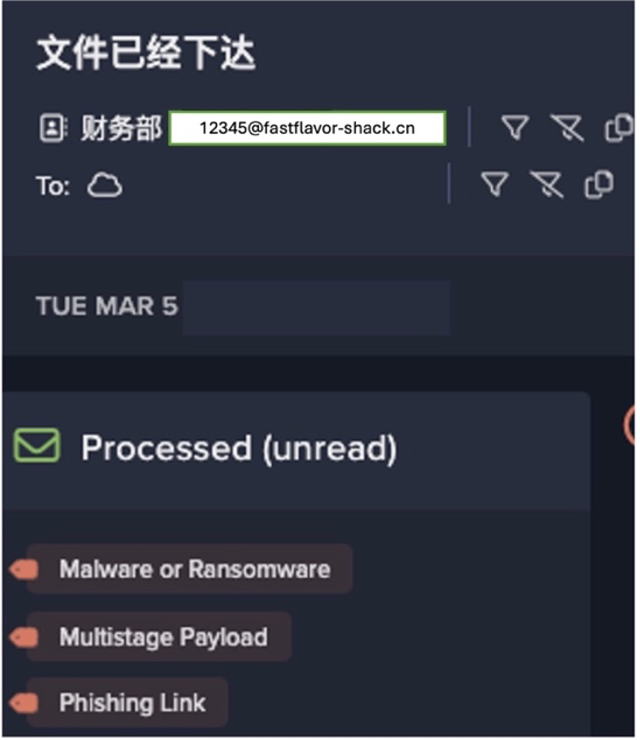
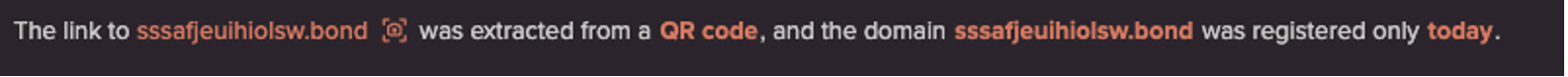
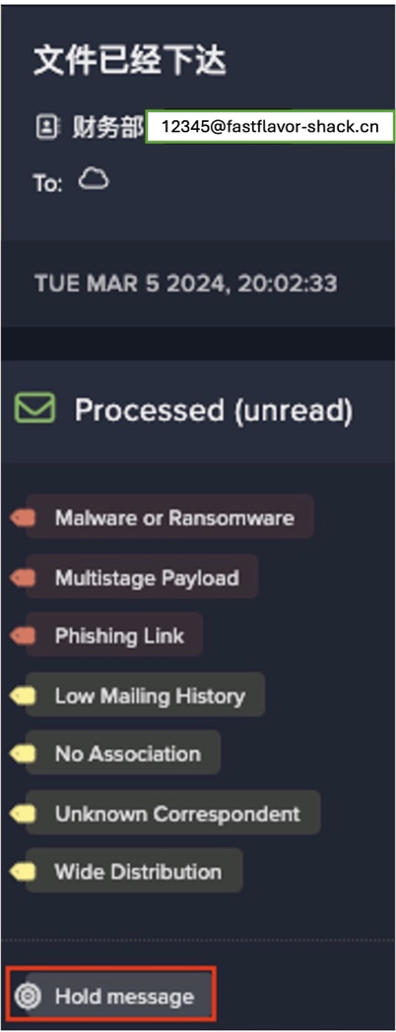
例えば、最近行われたフィッシングキャンペーンでは、13通のメールのうち5通がVIPユーザーを標的としたものでした。Darktrace/Emailは、リンクを二重にロックし、メッセージを保留し、添付ファイルを削除することで、悪意のあるEメールに対処しました。
非VIPユーザーがフィッシングやなりすましメールの半数近くを受信していることを考えると、セキュリティチームが重要な資産を保護する上での盲点を認識することの重要性が浮き彫りになりました。非VIPエンティティから発信される潜在的な脅威を見過ごすと、深刻な結果を招きかねません。例えば、非VIPユーザーがフィッシング攻撃の犠牲になったり、危険にさらされたりした場合、その認証情報を悪用されて組織内で横方向に移動し、重要な資産に到達する可能性があります。
このため、大規模なカスタマイズを必要とせず、VIPのステータスに関係なく、標的となるユーザーを特定できる高度なセキュリティツールの必要性が高まっています。勧誘、フィッシング、なりすましなど、標的となるユーザーのステータスに関係なく、Eメールの脅威に迅速に対応できるソリューションを導入することで、セキュリティチームは防御体制を大幅に強化することができます。
Darktrace と従来のEメール攻撃検知技術との比較
従来のルールやシグネチャベースの検知メカニズムでは、Eメールを分類するために過去の攻撃に関する知識に依存しているため、私たちが観測した進化する脅威を特定するには不十分です。
セキュアEメールゲートウェイ(SEG)や統合型クラウドメールセキュリティ(ICES)ツールは、既知の攻撃や既知の攻撃に基づいてEメールを分類し、既知の「善玉」モデルや既知の「悪玉」モデルで稼働するのみです。たとえツールがAIを活用してこのプロセスを自動化したとしても、そのアプローチは基本的に過去のものであるため、未知の脅威やゼロデイ脅威に対して脆弱であることに変わりはありません。
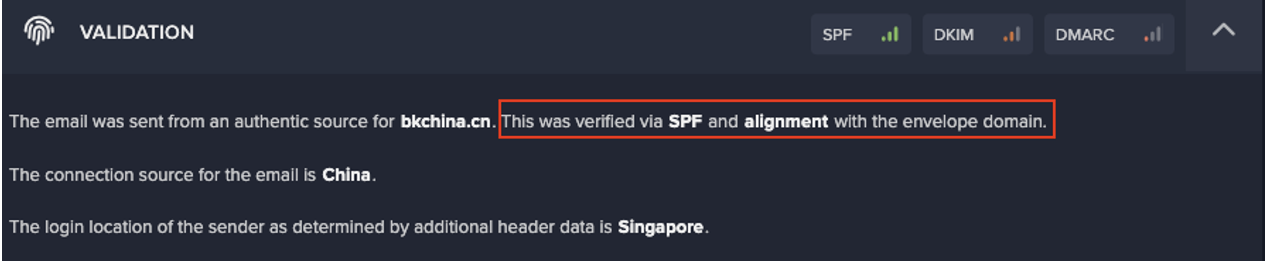
Darktrace は、各組織の特徴を理解し、そのEメール環境がネットワーク上の各ユーザーやデバイスとどのように相互運用されているかをAIで把握します。その結果、疑わしいと判断される通常の行動からの微妙な逸脱を特定することができます。このアプローチは単純な分類を超え、送信者の履歴や受信者の露出スコアなどの要因まで考慮します。
この微妙な分析により、Darktraceは本物の通信と悪意のあるなりすましの試みを区別することができます。手動入力の必要なく、誰がVIPであるかを自動的に理解し、ユーザーのステータスに基づいて、受信した悪意のあるEメールに対してより強力なアクションを実行します。
Eメールは、手動入力の必要なく、誰がVIPであるかを判断し、悪意のあるEメールの着信に対してより強力に対処します。
Darktrace/Email はまた、Darktraceの予防的セキュリティツールにフィードされ、相互接続された各AIエンジンに受信トレイから始まる重要な内部システムや資産への価値の高いターゲットや経路を評価するためのさらなるコンテキストを与えます。
AIを駆使して組織全体の保護を強化
AIを活用したセキュリティソリューションの有効性は、リアルタイムのビジネスデータに基づいて、情報に基づいた意思決定とレコメンデーションを行う能力にあります。このデータを活用することで、AI駆動型ソリューションは、悪用可能な攻撃経路と組織の最も重要な資産を特定することができます。Darktrace は独自の方法で複数のAIを駆使し、セキュリティチームがどの経路を保護すべきかについて情報に基づいた意思決定を行うために必要な洞察力を備え、VIPを保護することの重要性に関する人間のバイアスを低減します。
AutoGPTのようなツールの出現により、フィッシング攻撃の潜在的な標的の特定はますます簡素化されてきています。しかし、真の課題は、組織内の重要な資産やIDにつながる可能性のある難易度の低い攻撃経路をすべて包括的に理解することにあります。
同時に組織は、ユーザーの理解を活用し、Eメールによる脅威の成功を未然に防ぐことができるEメールツールを必要としています。Darktrace/Emailは、すべてのEメールとユーザーに対して、送信者、受信者、コンテンツ、言語、その他多くの要因による行動の変化を考慮します。
Darktrace/Email をDarktraceの攻撃経路モデリング機能と統合することで、包括的な脅威のコンテキストの可視化が可能になり、攻撃経路のより深い理解が促進されます。この全体的なアプローチにより、ユーザーのステータスに関係なく、すべての潜在的な脆弱性に対処できるようになり、全体的なセキュリティ体制が強化されます。
結論
従来の常識に反して、我々の分析によると、なりすましや 難易度の低い攻撃経路の影響を受けやすいという点で、VIPとそうでない人の区別は、推定されているほど顕著ではないことが示唆されました。したがって、セキュリティチームは、VIPのみに焦点を当てるのではなく、すべての経路を保護する積極的な姿勢を採用する必要があります。
攻撃経路のモデリングは、潜在的な影響、被害、露出、弱点に関する重要なメトリックを提供することにより、Darktrace/Emailの機能を強化し、よりターゲットを絞った効果的な脅威緩和戦略を実行可能にします。例えば、侵害された場合に潜在的な影響が大きいことが判明しているユーザーに対して、より強力なEメール対処アクションを取ることができます。
サイバー脅威が複雑化し進化し続ける時代には、受信トレイ、優先度の高い個人、重要な資産を保護するための、適応的でサイロ化しないアプローチが不可欠なのです。