Eメールを主なターゲットとする脅威が拡大する中、ITチームは、十分なスピードで進化していない従来のEメールセキュリティの手法をはるかに超えることが必要です。過去の攻撃データに基づいて訓練されているため、以前に見たことのあるものしか検知できないのです。
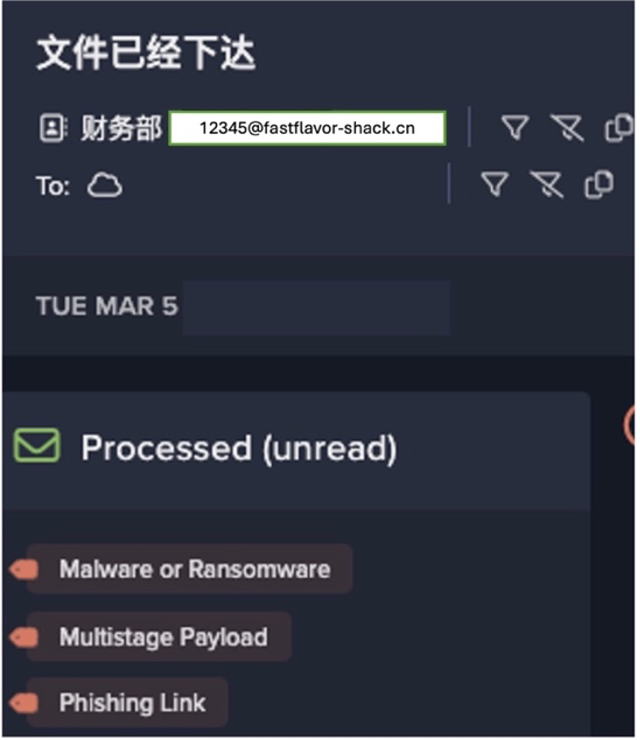
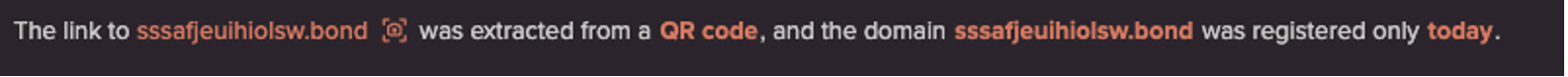
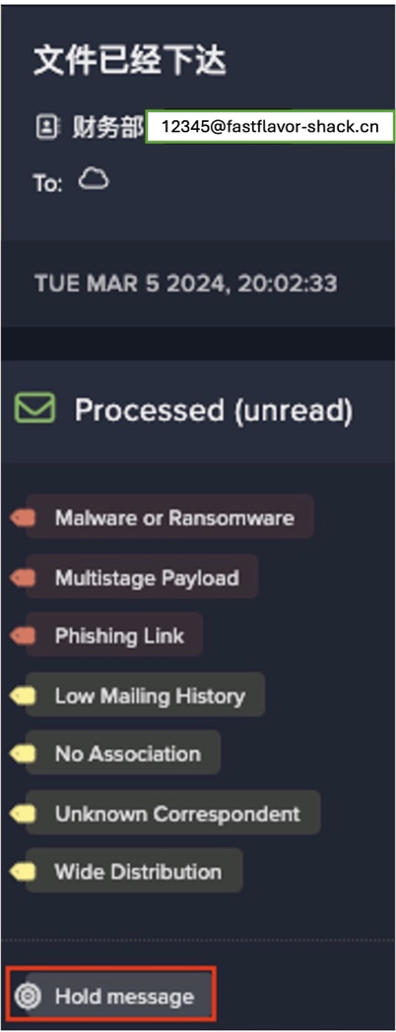
フィッシング攻撃は、攻撃者が配信戦術とソーシャルエンジニアリングという2つの重要な領域で革新を遂げるにつれて、より標的を絞り、洗練されてきています。マルウェアの配信面では、SharePointやOneDriveなどのサービスや、正規のメールアカウントなどの正規のインフラや評判を利用して、セキュリティツールを回避する攻撃者が増えてきています。
攻撃者は、Eメールの向こう側にいる人間から逃れるために、新しいソーシャルエンジニアリングの戦術を駆使し、これまでと同様に恐怖、不確実性、疑念(FUD)を悪用することで緊急性を喚起しています。
ChatGPTのようなツールの助けを借りて、脅威アクターはAI技術を活用し、信頼できる組織や連絡先になりすますことができます。具体的には、ビジネスメールの侵害、現実的なスピアフィッシング、スプーフィング、ソーシャルエンジニアリングなどの損害を与えることができます。実際、DarktraceはChatGPTのリリース以降、フィッシングメールの平均的な言語的複雑さが17%も跳ね上がったことを検知しています。
これは、攻撃の高度化が加速し、攻撃者の参入障壁が低くなり、攻撃結果が改善された一例です。これは、攻撃環境が、洗練度が低く、インパクトが小さい、一般的なフィッシング戦術(「スプレー&プレー」アプローチ)から、ルールやシグネチャに依存するあらゆるツールの典型的な検知範囲から外れる、より標的を絞った、洗練され、インパクトの大きい攻撃へと移行するという、より広いトレンドの一部を形成しています。攻撃者のツールキットに含まれる生成AIやその他のテクノロジーによって、こうした攻撃を大規模に行うことが可能になり、以前から見られていた既知の脅威を捕らえるだけでは、もはや十分ではなくなります。

Eメールを主なターゲットとする脅威が拡大する中、大半のEメールセキュリティツールは十分な進化を遂げていません。また、過去の攻撃データから次の攻撃を予測し、今日の攻撃を明日につなげるように設計されています。
組織ではAIシステムへの移行が進んでいますが、すべてのAIが同じというわけではなく、そのAIの応用が重要です。ITおよびセキュリティチームは、コンテキストを認識し、AIを活用して深い行動分析を行うメールセキュリティに移行する必要があります。これは、何千もの組織で、他のツールをすり抜ける攻撃を見事にキャッチしてきた、実績のあるアプローチです。また、今日のEメールセキュリティは、受信トレイを保護するだけではありません。悪意のあるメールだけでなく、メールメッセージやアカウントなど、ユーザーの全方位的な視点、さらにメールがコラボレーションツールやSaaSに侵入するような範囲にも対応する必要があるのです。多くの企業にとって、問題はメールセキュリティをアップグレードすべきかどうかではなく、いつアップグレードするか、つまり、過去にとらわれたメールセキュリティにいつまで頼ることができるのかということです。
メールセキュリティ業界はいたちごっこの世界
ゲートウェイやICES(Integrated Cloud Email Security)プロバイダーには、未来を予測するために過去の攻撃に目を向けるという共通点があります。これらのツールは、過去の脅威インテリジェンスや、すでに悪意があると判断されたメールの既知の悪い要素を集めた「拒否リスト」に頼ることが多く、現代の脅威状況の現実に対応できていないのです。これらのツールの中には、AIを使用してこの欠陥のあるアプローチを改善しようとするものもあり、直接一致するものを探すだけでなく、「データ拡張」を使用して類似したメールを見つけようとします。しかし、このアプローチでは、本質的に新しい脅威が見えないことに変わりはありません。
このようなツールは、リソースを過剰に必要とする傾向があり、常にポリシーを維持し、保持されている正当なメールを解放し、悪意のあるフィッシングメールを阻止するための手作業が必要となります。個々のEメールを手動で解除するこの負担は、通常、セキュリティチームに課せられますが、このチームは小規模で複数の担当領域を持つことが多いのです。解決策としては、悪質なメールを自律的に阻止 し、正規のメールを通過させ、組織の変化に適応するテクノロジー、つまり「セット&フォーゲット」という定義に実際に適合するテクノロジーを導入することです。
挙動と文脈を意識する
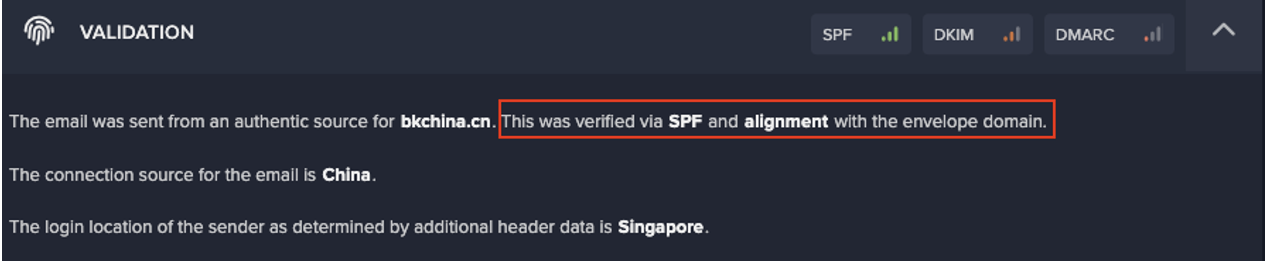
業界では、「安全な」メールゲートウェイから、AIを活用したインテリジェントな思考への激変が進行中です。正しいアプローチは、エンドユーザーの行動を理解すること、つまり、各人が受信トレイをどのように使っているか、各ユーザーにとって何が「普通」であるかを理解することで、普通でないことを検知することです。また、いつ、どのように、誰と、どのようにコミュニケーションしているかというコンテキストを利用して、異常な点を発見し、何かおかしいと思ったら、その理由とともにユーザーに警告を発します。基本的には、(過去の攻撃ではなく)あなたを理解するためのシステムです。
Darktrace は、過去のデータから危険なものを学習するのではなく、各組織とそのユーザーを深く継続的に理解することで、根本的に異なるアプローチのAIを開発しました。各従業員の通常の日々の行動を複雑に理解してこそ、メールが実際にその受信者の受信箱に属するかどうかを正確に判断することができるのです。
フィッシング、ランサムウェア、請求書詐欺、役員なりすまし、あるいはもっと斬新な手法であっても、行動分析にAIを活用することでより迅速な意思決定が可能になります。悪質な脅威を初見で阻止できるため、新しい攻撃を封じるためにゼロ号患者を待つ必要がありません。検知の信頼性が高まることで、より的確な対応、つまり、警戒心から広範な包括的対応を行うのではなく、メールの最も危険な部分のみを削除する標的型対応を行うことができ、ビジネスの混乱を最小限に抑えながらリスクを低減することができます。
攻撃スペクトルに話を戻すと、マルウェアの配布や被害者の誘導に、斬新な、あるいは一見正当なインフラを使用する高度に洗練された攻撃への移行がますます進んでおり、こうしたインパクトの強い標的型攻撃を検知して適切な対応を行うことがかつてなく重要になってきています。

お客様を理解し、エンドユーザーを全方位で見渡す
現代のEメールセキュリティは、受信箱だけに限定されるものではなく、Eメールやそれ以外の場所でのユーザーの通常の行動を完全に理解する必要があることを私たちは知っています。従来のEメールツールは、侵入のポイントとしてインバウンドメールにのみ焦点を当てており、アカウントが侵害された後、Eメール攻撃の成功によって引き起こされる潜在的に壊滅的なダメージから保護することができません。

Microsoft 365、Google Workspace、Salesforce、Dropbox、そしてネットワーク上のデバイスでのユーザーの行動を把握することは、そのユーザーにとって何が正常であるかを完全に把握するために極めて重要です。デバイス(および受信箱)の感染症状を監視することは、悪意のあるメールかどうかを判断し、今後同様のメールを送信しないようにする必要があるかどうかを判断するために非常に重要です。クラウドアプリのデータと組み合わせることで、IDベースの攻撃をより全体的に把握することができます。
また、メールセキュリティと攻撃対象の外部データを結びつけることで、悪意のあるドメインをプロアクティブに発見し、攻撃が開始される前に防御を強化することができます。
従業員への教育および啓蒙活動
最終的に、Eメールに接するのは従業員です。このようなユーザーをうまく活用することができれば、よりスマートな従業員、より少ない攻撃回数、そしてより戦略的な業務に時間を割くことができるセキュリティチームを手に入れることができるのです。
最も成功するツールは、AIを活用して従業員のセキュリティ意識を向上させることができるものでしょう。明らかに悪意があり、従業員の受信トレイに決して入ってはいけないメールもありますが、潜在的に危険な要素を持つメールには、かなりのグレーゾーンが存在します。大半のセキュリティツールは、これらのメールを、たとえビジネスクリティカルなものであったとしても、完全に受信を拒否するか、あるいは無傷で通過させるかのどちらかです。しかし、このようなグレーゾーンのメールが、実はトレーニングの機会として活用できるとしたらどうでしょうか。
フィッシングシミュレーションベンダーとは対照的に、行動AIは、ユーザーの受信トレイを通じて軽いタッチでトレーニングを行うことで、組織全体のセキュリティ意識を総合的に向上させることができ、エンドユーザーを防御強化の輪に引き込むことができます。
メールセキュリティの新境地は、AIとAIとの戦いであり、遅れをとった組織は、つらい思いをすることになるかもしれません。これらのテクノロジーは、従業員の体験をどのように変え、展開をダイナミックにし、セキュリティチームを増強し、統合された防御ループの一部を形成することができるかについて、Darktraceのブログシリーズをお読みください。
[1] 複数のアクティブなフィッシングペイロードに対するDarktrace/Emailのレスポンスと、他のメールセキュリティ技術が提示した16の独立したフィードのうち最も早いものとの間に生じた検知期間の差の平均