2022年後半、Darktrace は顧客基盤においてVidar Stealerの感染が増加していることを確認しました。これらの感染は、コマンド&コントロール(C2)情報の取得のための特定のソーシャルメディアプラットフォームの使用や、C2通信における特定のURIパターンの使用など、予測可能な一連のネットワーク行動で構成されていました。このブログでは、これらのVidar Stealer感染で観察されたネットワーク活動のパターンの詳細と、この活動に関するDarktraceのカバレッジについて説明します。
Vidar Stealerの活動背景
2018年に初めて確認されたVidar Stealerは、ユーザーのデバイスから機密データを取得し、その後流出させることができるインフォスティーラーです。このデータには、銀行の詳細、保存されたパスワード、IPアドレス、ブラウザの履歴、ログイン認証、暗号通貨ウォレットのデータなどが含まれます [1]。情報盗み出しツールは、通常、悪意のあるスパムメール、クラックされたソフトウェアのウェブサイト、悪意のある広告、正規のブランドを装ったウェブサイトを通じて配信され、ユーザーのデバイス上で実行されると、ソーシャルメディアプラットフォームのプロファイルにアクセスすることが知られています。インフォスティーラーは、このようにして、コマンド&コントロール(C2)サーバーのIPアドレスを取得します。C2サーバーのIPアドレスを取得した後、他の多くのインフォスティーラーと同様に、サードパーティーのダイナミックリンクライブラリ(DLL)をダウンロードし、感染したデバイスに保存されている機密データにアクセスするために使用することが知られています。そして、入手した機密データを束ねて、C2サーバーに送り返します。
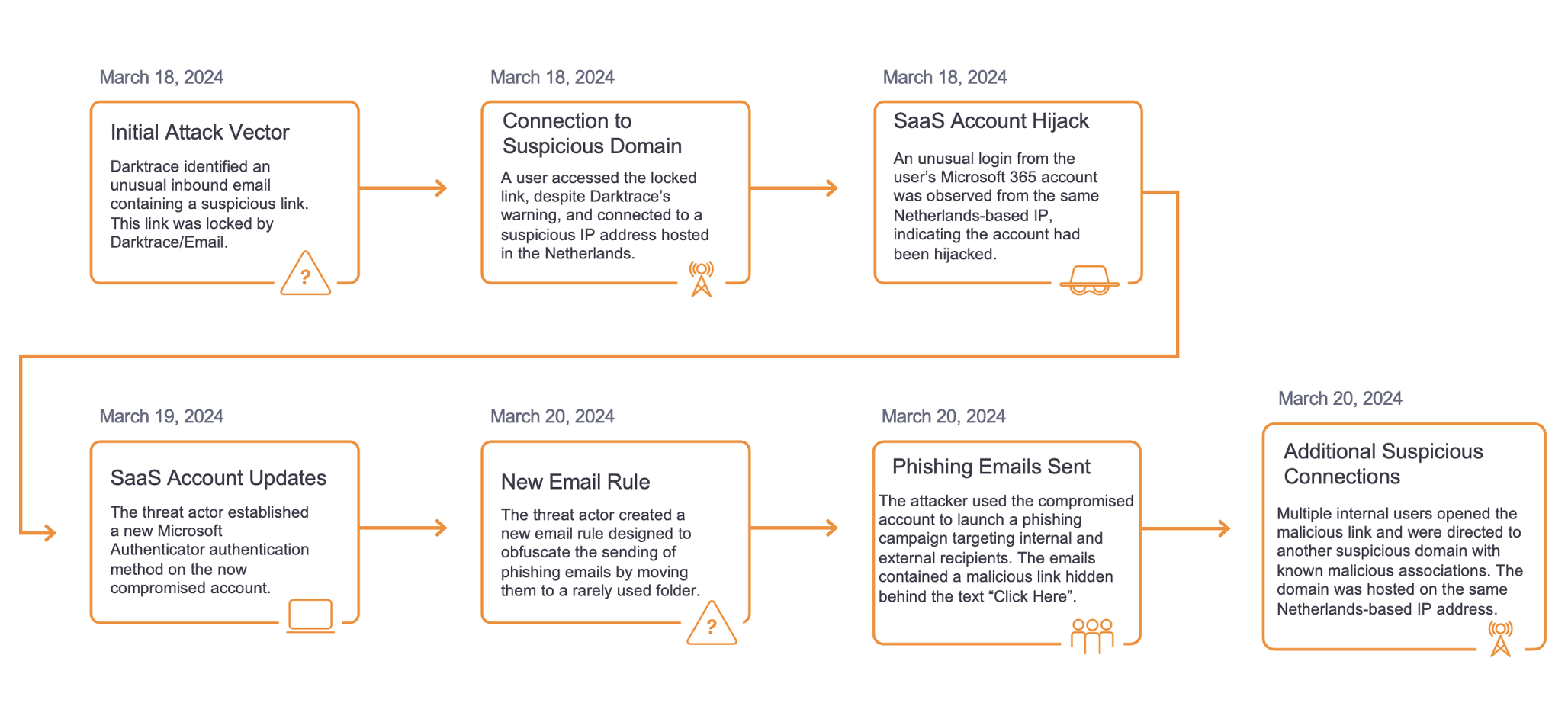
一連の攻撃の詳細
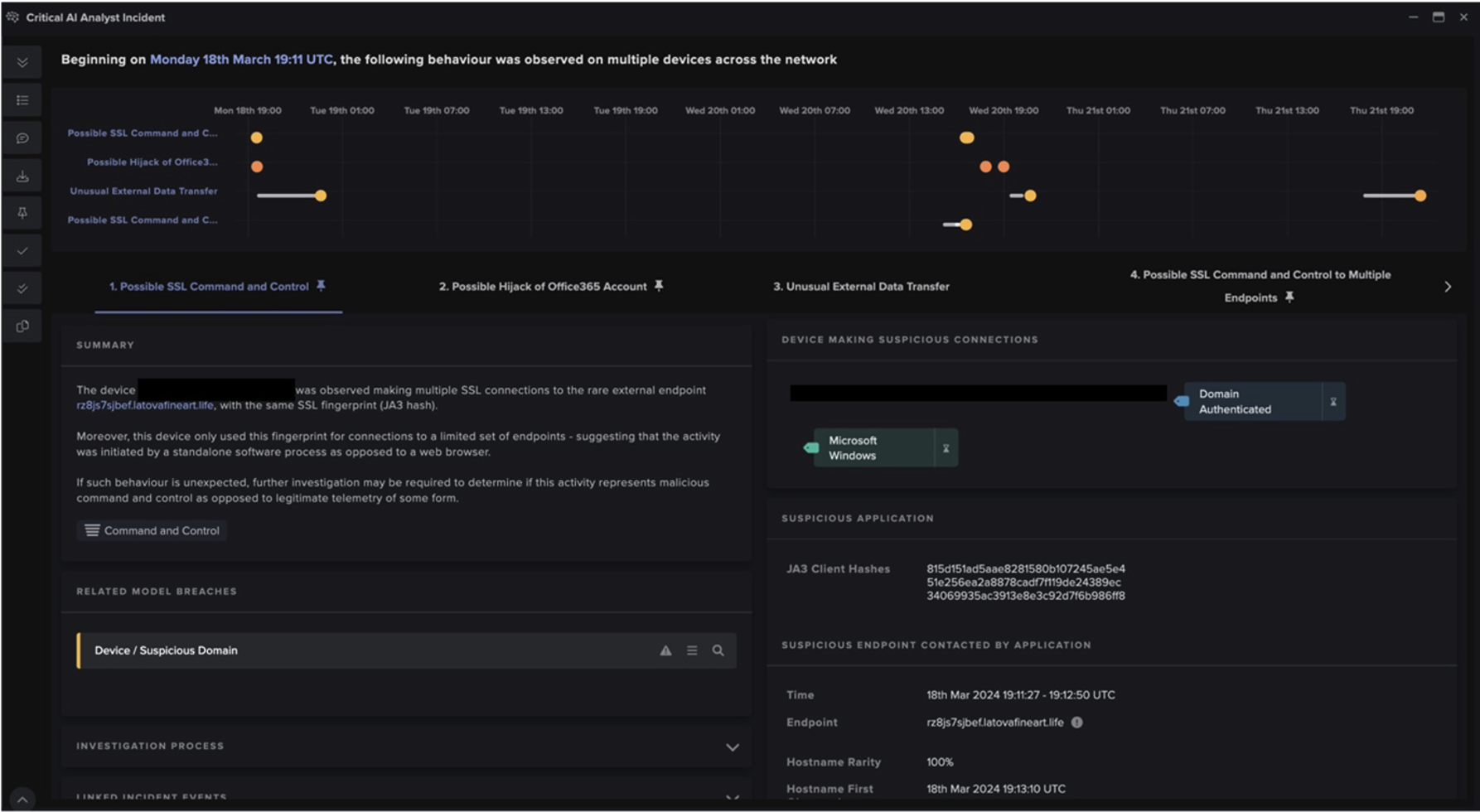
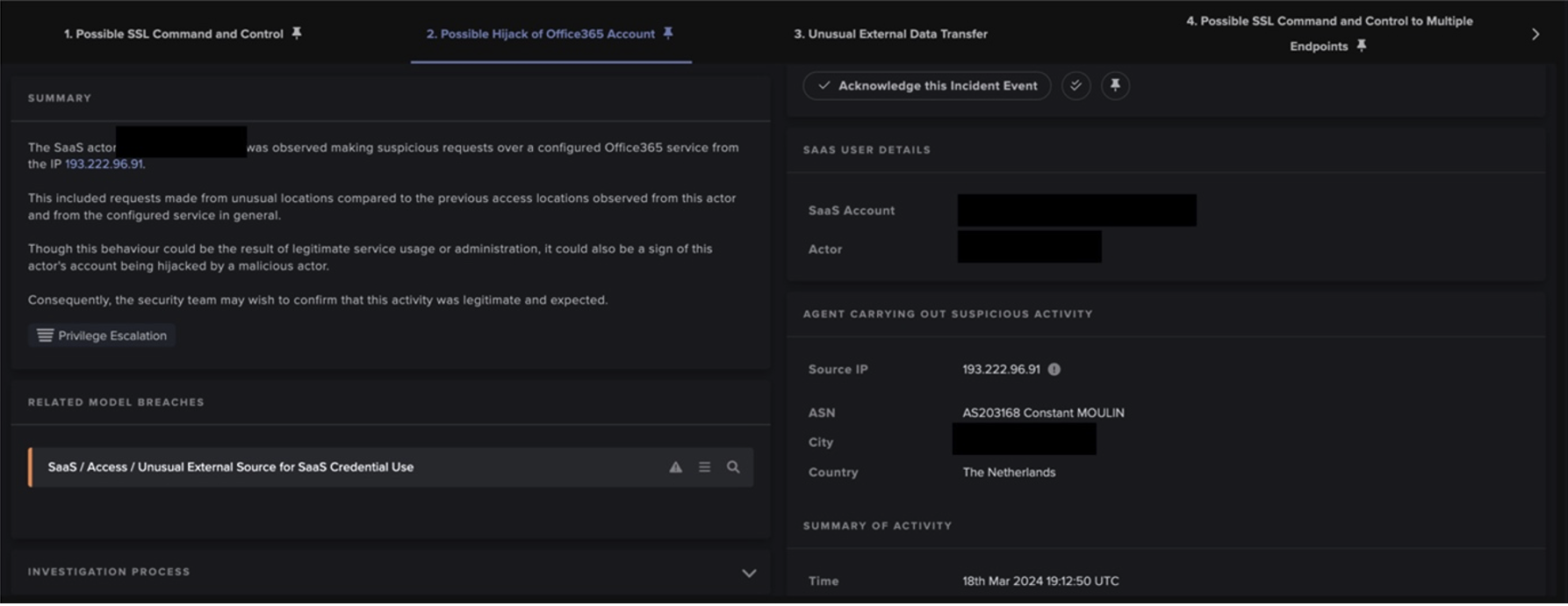
2022年後半、Darktrace は多くのクライアントネットワークで次のような活動パターンを確認しました:
1. ユーザーのデバイスがTelegramおよび/またはMastodonサーバーにHTTPS接続
2. ユーザーのデバイスが、空のUser Agentヘッダー、空のHostヘッダー、4桁からなるターゲットURIを持つHTTP GETリクエストを、通常とは異なる外部のエンドポイントに行う
3. ユーザーのデバイスは、空のUser Agentヘッダー、空のHostヘッダー、および10桁の数字の後に .zip が続くターゲットURIを持つHTTP GETリクエストを、通常とは異なる外部のエンドポイントに送信
4. ユーザーのデバイスは、空のUser Agentヘッダー、空のHostヘッダー、およびターゲットURI " / " を使用して、通常とは異なる外部のエンドポイントにHTTP POSTリクエストを送信


これらの一連のアクティビティは、ユーザーがデバイス上でVidar Stealerを実行した結果、それぞれ発生したものです。ユーザーを騙してデバイス上でVidar Stealerを実行させるために使用された一般的な方法はありません。むしろ、マルスパムからクラックされたソフトウェアのダウンロードに至るまで、様々な方法が使用されたようです。
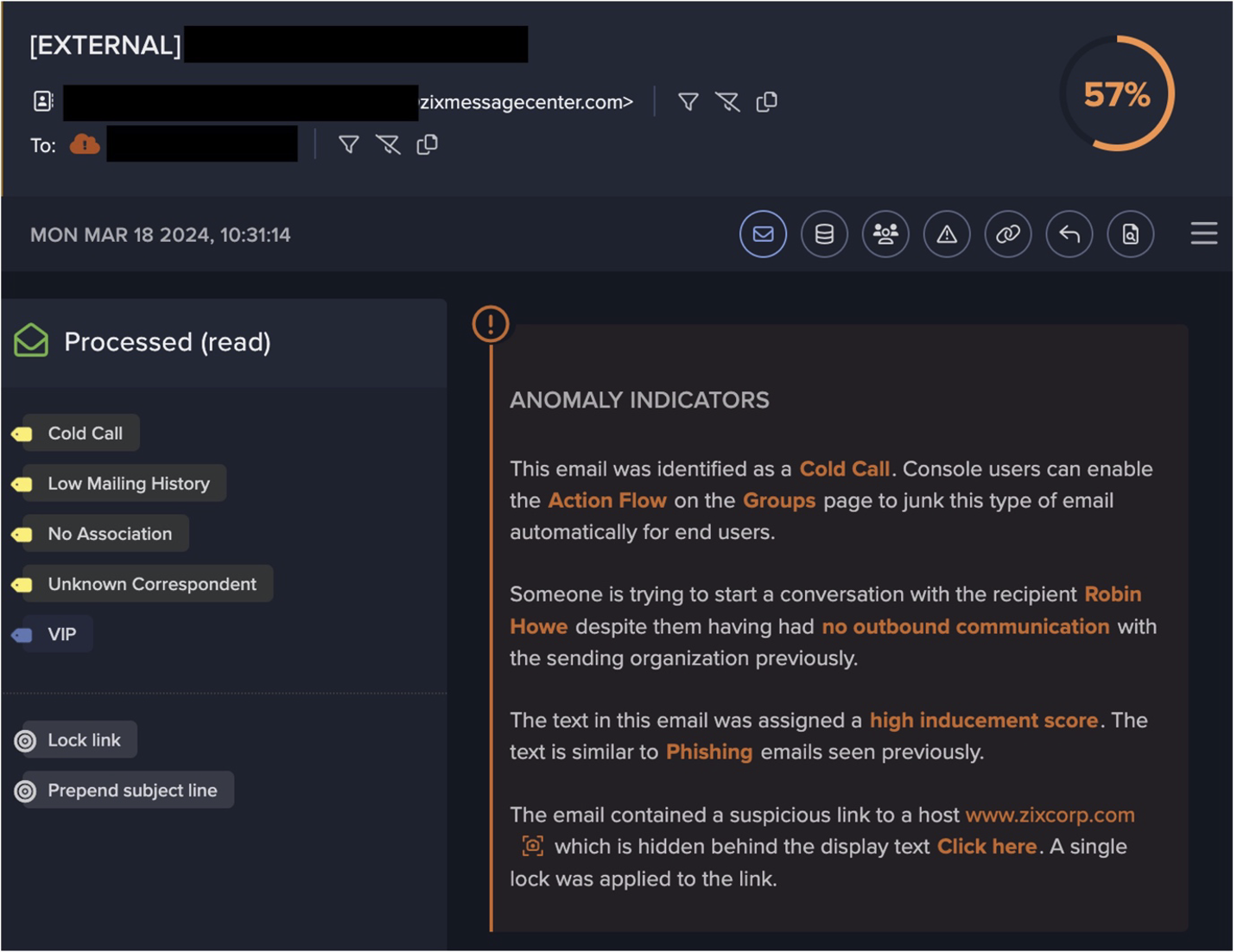
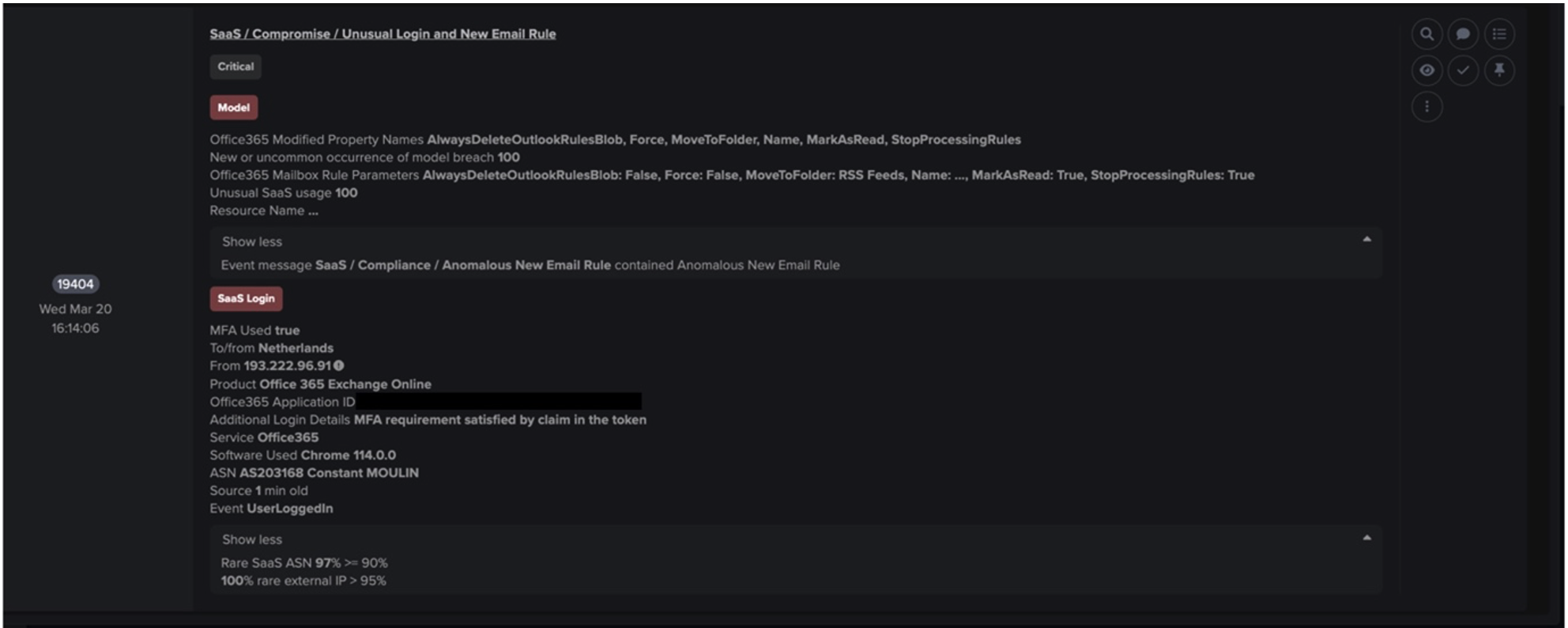
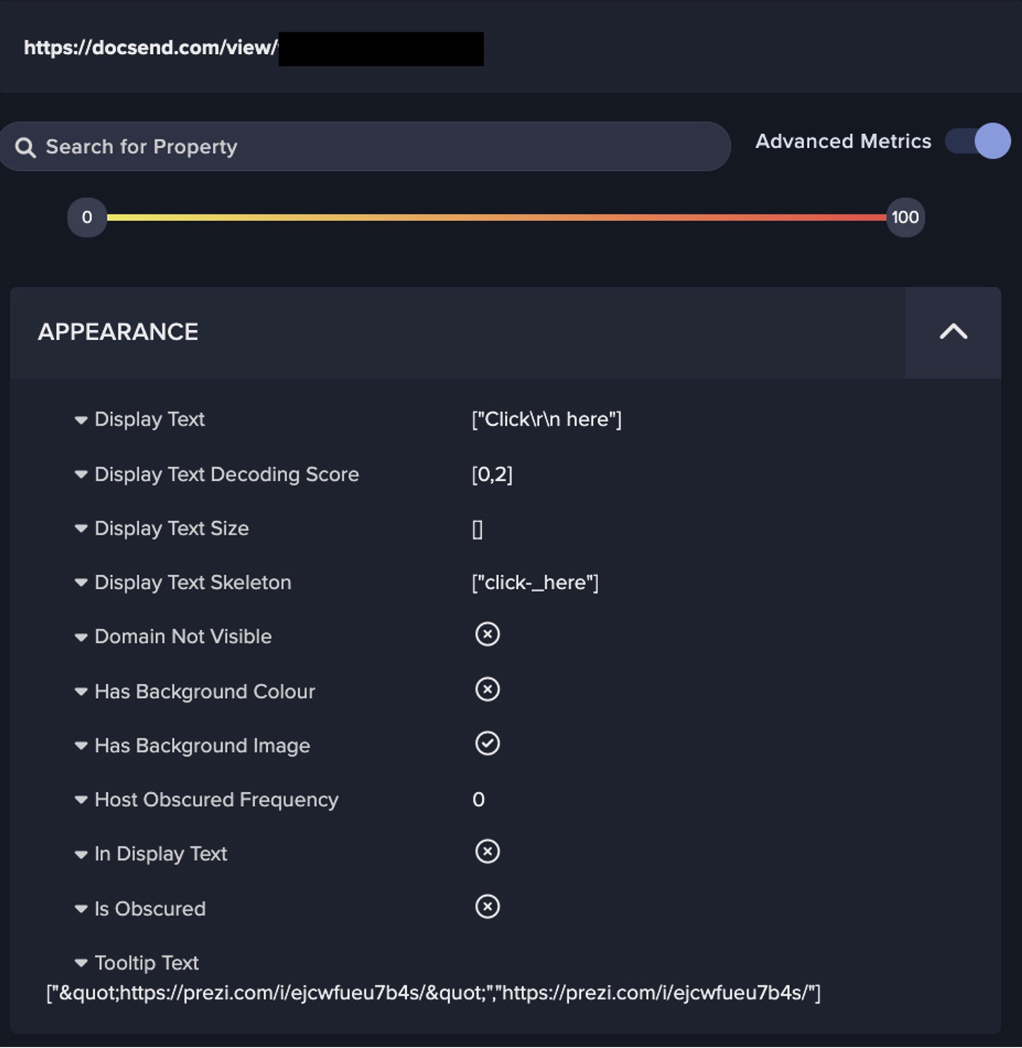
Vidar Stealerは、ユーザーのデバイス上で実行されると、Telegram(https://t[.]me/)またはMastodonサーバー(https://nerdculture[.]de/ または https://ioc[.]exchange/)へのHTTPS接続を行います。TelegramとMastodonは、ユーザーがプロフィールを作成できるソーシャルメディアプラットフォームです。悪意のある行為者は、これらのプラットフォーム上でプロフィールを作成し、そのプロフィールの説明文にC2情報を埋め込むことが知られています[2]。 Darktraceのクライアントベースで観察されたVidarのケースでは、Vidarは、プロファイルの説明からC2サーバのIPアドレスを取得するために、Telegramおよび/またはMastodonサーバに連絡していたようです。ソーシャルメディアプラットフォームは一般的に信頼されているため、マルウェアのサンプルとC2情報を共有するこの「デッドドロップ」方式では、脅威アクターは、これらの変更の伝達をブロックされることなく、C2情報を定期的に更新することが可能になります。

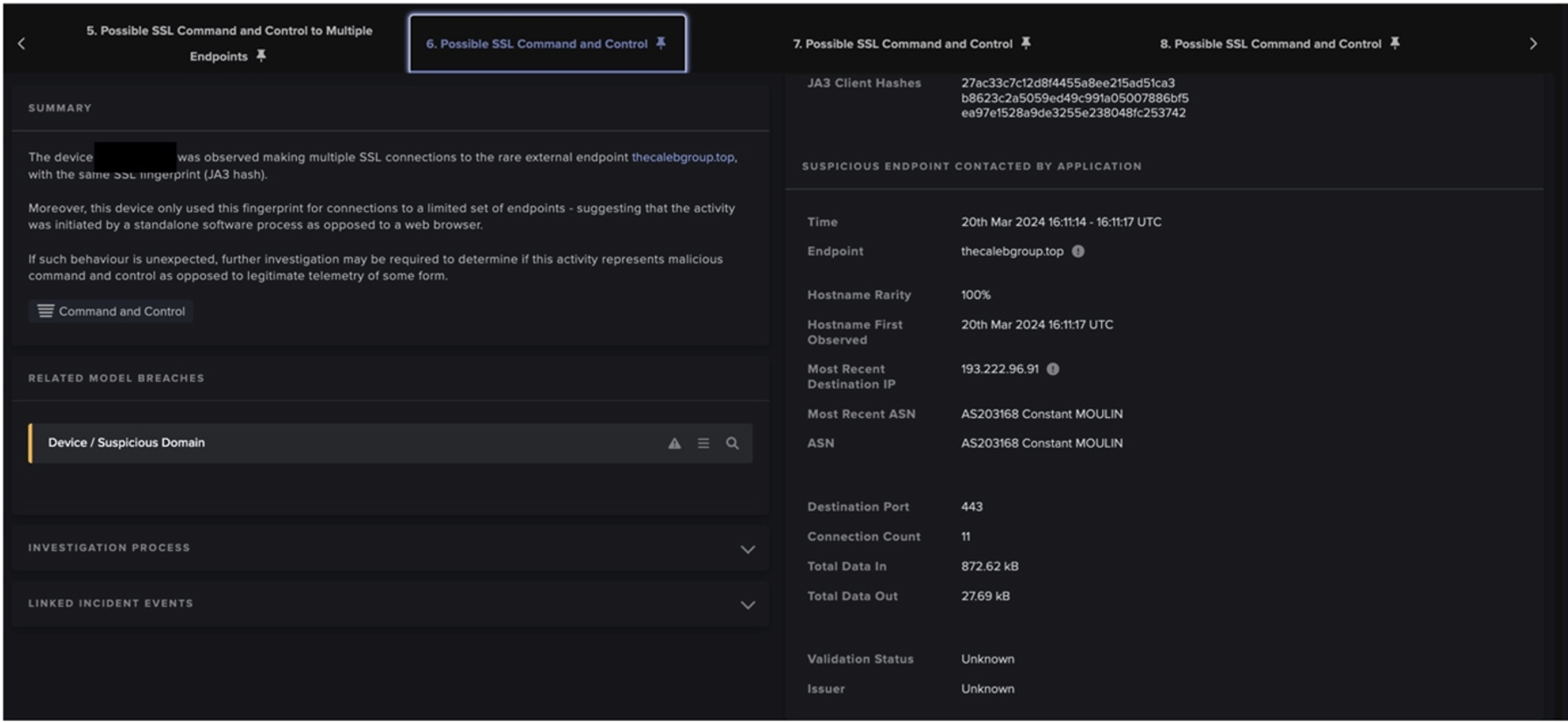
TelegramまたはMastodonプロファイルの説明からC2アドレスを取得した後、Vidarは空のUser Agentヘッダー、空のHostヘッダー、4桁からなるターゲットURIでC2サーバにHTTP GETリクエストを行いました。このURIに現れる数字の並びはキャンペーンIDです。C2サーバはVidarのGETリクエストに応答し、Vidarのその後のデータ窃取活動に影響を与えると思われる設定情報を提供しました。
Vidarは、設定の詳細を受け取った後、空のUser Agentヘッダー、空のHostヘッダー、および10桁の数字の後に .zip が続くターゲットURIを持つGETリクエストをC2サーバに送りました。このリクエストには、vcruntime140.dll のようなサードパーティ製の正規のダイナミックリンクライブラリを含むZIPファイルが応答されました。Vidarは、これらのライブラリを使用して、感染したホスト上に保存された機密データにアクセスしました。


Vidarは、サードパーティのDLLを含むZIPファイルをダウンロードした後、C2エンドポイントに数百キロバイトのデータを含むPOSTリクエストを行いました。このPOSTリクエストは、窃取した情報の流出を意味する可能性が高いです。
Darktrace のカバレッジ
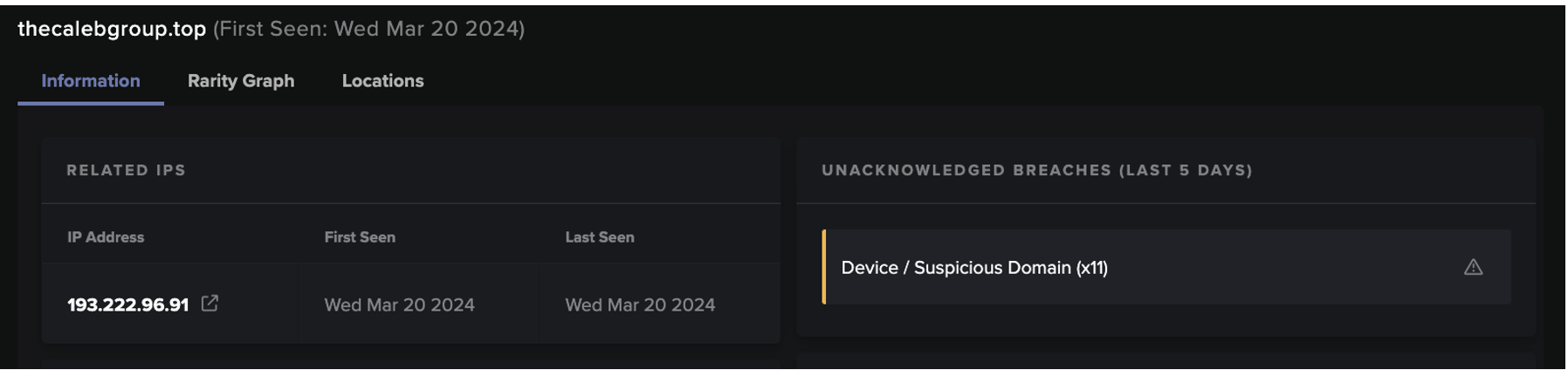
Vidarは、ユーザーのデバイスに感染した後、TelegramまたはMastodonに連絡し、そのC2サーバに一連のHTTPリクエストを行います。このインフォスティーラーは、ソーシャルメディアプラットフォームを使用し、ツールの転送にZIPファイルを使用するため、その活動の検知を複雑にしています。しかし、このインフォスティーラーのC2サーバーへのHTTPリクエストは、以下のDarktrace DETECT/Networkモデルを侵害する原因となりました:
- Anomalous File / Zip or Gzip from Rare External Location
- Anomalous File / Numeric File Download
- Anomalous Connection / Posting HTTP to IP Without Hostname
これらのモデルブリーチは、ユーザーのデバイスが Vidar に関連することが知られている IP アドレスに接触したために発生したものではありません。実際、報告された活動が発生した時点で、接触したIPアドレスの多くは、Vidarの活動と関連付けるOSINTを持っていませんでした。これらのモデルブリーチの原因は、実際にはデバイスの HTTP アクティビティの異常さにありました。Vidar に感染したデバイスが C2 サーバーに HTTP リクエストを送信しているのが観測されたとき、Darktrace は、この動作がデバイスにとってもネットワーク内の他のデバイスにとっても非常に異例であることを認識し ました。Darktraceがこの異常性を認識したことにより、モデルブリーチが発生したのです。
Vidar Stealerの感染は驚くほど速く、最初の感染からデータ窃取までの時間が1分未満になることもあります。Darktraceの 自律遮断技術が有効な場合、Darktrace RESPOND/Network は、最初の接続が行われた直後に、Vidar の C2 サーバーへの接続を自律的にブロックすることが可能でした。

結論
2022年後半、Darktraceの顧客基盤において、特定のパターンの活動が盛んに行われ、そのパターンは幅広い業種や規模の顧客のネットワークで散見されました。さらに調査を進めると、このネットワーク活動のパターンは、Vidar Stealerの感染によるものであることが判明しました。これらの感染は、情報取得にソーシャルメディアプラットフォームを使用し、ツール転送にZIPファイルを使用するため、動きが早く、検知を回避するのに有効でした。インフォスティーラーの影響は、通常、最初の感染から時間が経過した後にネットワーク外で発生するため、インフォスティーラーの活動を十分に検知できない場合、攻撃者が知らないうちに活動し、強力な攻撃ベクトルが利用可能になって広範囲の侵害が行われる危険性があります。
Vidar のオペレーターによる回避の試みにもかかわらず、Darktrace DETECT/Network は、Vidar の感染から必然的に生じる異常な HTTP 活動を検知することができました。Darktrace RESPOND/Networkは、このような異常な活動に対して迅速に抑制的な行動をとることができました。Vidar Stealerの普及率[3]とVidar Stealer感染の進行速度を考慮すると、自律遮断技術は情報窃盗団の活動から組織を保護するために不可欠であることが証明されています。
本ブログに寄稿した脅威リサーチチームに感謝します。
MITRE ATT&CK マッピング

IoC一覧
107.189.31[.]171 - Vidar C2 Endpoint
168.119.167[.]188 – Vidar C2 Endpoint
77.91.102[.]51 - Vidar C2 Endpoint
116.202.180[.]202 - Vidar C2 Endpoint
79.124.78[.]208 - Vidar C2 Endpoint
159.69.100[.]194 - Vidar C2 Endpoint
195.201.253[.]5 - Vidar C2 Endpoint
135.181.96[.]153 - Vidar C2 Endpoint
88.198.122[.]116 - Vidar C2 Endpoint
135.181.104[.]248 - Vidar C2 Endpoint
159.69.101[.]102 - Vidar C2 Endpoint
45.8.147[.]145 - Vidar C2 Endpoint
159.69.102[.]192 - Vidar C2 Endpoint
193.43.146[.]42 - Vidar C2 Endpoint
159.69.102[.]19 - Vidar C2 Endpoint
185.53.46[.]199 - Vidar C2 Endpoint
116.202.183[.]206 - Vidar C2 Endpoint
95.217.244[.]216 - Vidar C2 Endpoint
78.46.129[.]14 - Vidar C2 Endpoint
116.203.7[.]175 - Vidar C2 Endpoint
45.159.249[.]3 - Vidar C2 Endpoint
159.69.101[.]170 - Vidar C2 Endpoint
116.202.183[.]213 - Vidar C2 Endpoint
116.202.4[.]170 - Vidar C2 Endpoint
185.252.215[.]142 - Vidar C2 Endpoint
45.8.144[.]62 - Vidar C2 Endpoint
74.119.192[.]157 - Vidar C2 Endpoint
78.47.102[.]252 - Vidar C2 Endpoint
212.23.221[.]231 - Vidar C2 Endpoint
167.235.137[.]244 - Vidar C2 Endpoint
88.198.122[.]116 - Vidar C2 Endpoint
5.252.23[.]169 - Vidar C2 Endpoint
45.89.55[.]70 - Vidar C2 Endpoint
参考文献
[1] https://blog.cyble.com/2021/10/26/vidar-stealer-under-the-lens-a-deep-dive-analysis/
[2] https://asec.ahnlab.com/en/44554/
[3] https://blog.sekoia.io/unveiling-of-a-large-resilient-infrastructure-distributing-information-stealers/