2022年2月、Darktraceは顧客のOffice 365環境における3つのSaaSアカウントの侵害を検知しました。このインシデントは、Darktrace/AppsとDarktrace/Emailがどのように連携して、異常なログイン、アプリの権限変更、新しいEメールルール、および送信スパムに警告を発することができるかを強調するための効果的なユースケースを提供します。また、Darktrace RESPOND/Appsが自律モードに設定されていれば、さらなる侵害を阻止できたかもしれなかった事例をお伝えします。
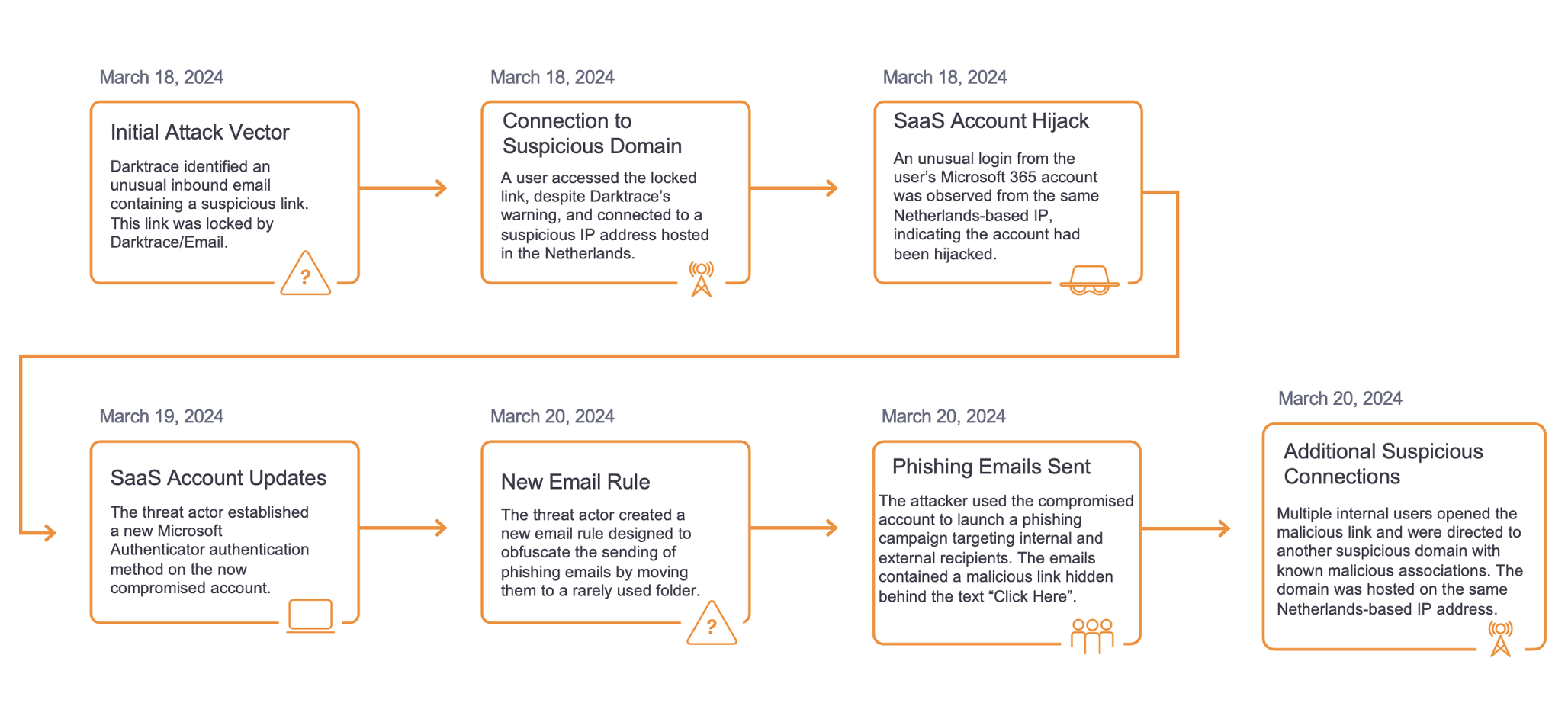
Account Compromise Timeline
February 9 2022
アカウントAは、一般的にSaaSアカウント攻撃と関連しているBAV2ROPCユーザーエージェントで、ナイジェリアからの稀なIPからログインされました。BAV2ROPCは「Basic Authentication Version 2 Resource Owner Password Credential」の略で、iOS Mailなどの古いEメールアプリで一般的に使用されています。BAV2ROPCは、アカウントが「レガシー認証」を有効にしているSaaS/メールアカウントの侵害でよく見られます。これは、多要素認証(MFA)が有効になっていても、IMAP/POP3のようなレガシーなプロトコルはMFA用に設定されていないため、MFA通知が送信されないためです。
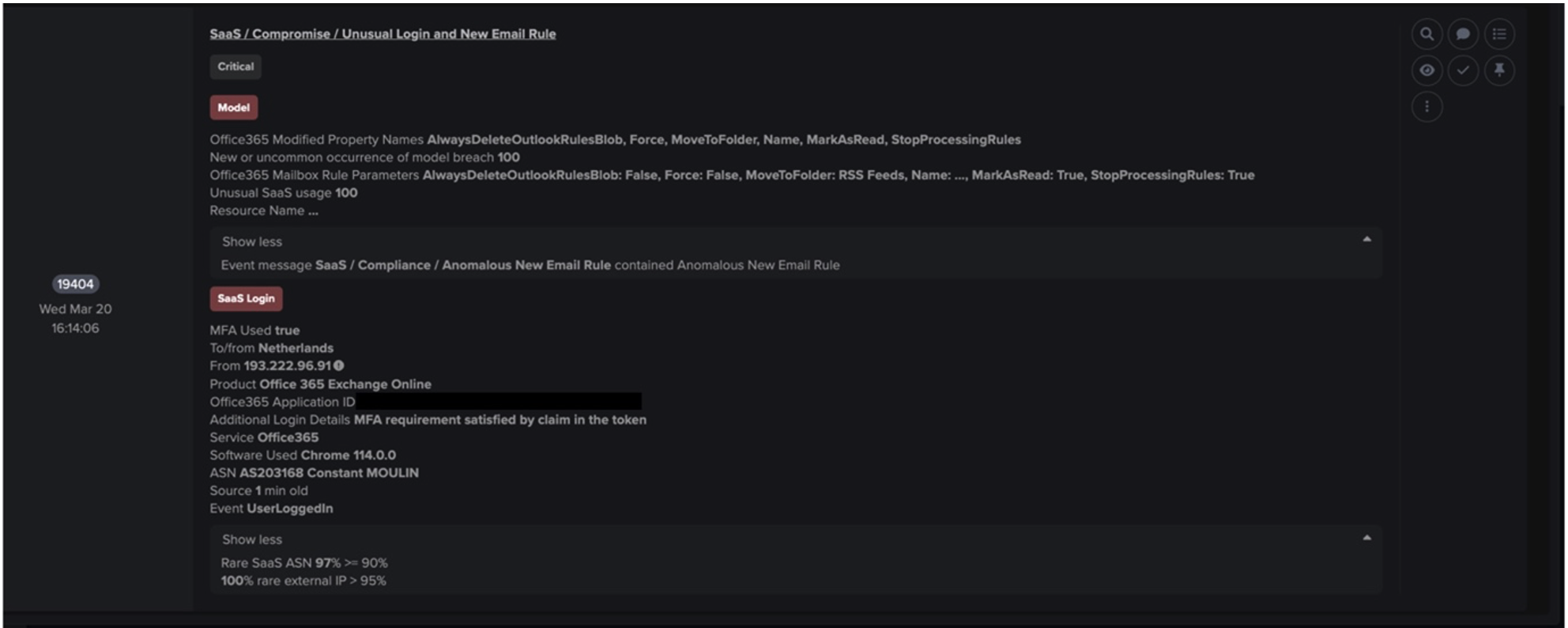
その後、アカウントAはシングルフルストップと名付けられた新たなEメールルールを作成しました。攻撃者は一般的に、自分が所有する外部のメールアカウントに特定のメールを転送する機能を使用して、自分自身に永続的なアクセスを与えるために新たなメールルールを作成します。つまり、そのアカウントのパスワードが変更されたり、MFAがオンになったりしても、そのルールが適用されている限り、攻撃者は転送されたメールを受け取り続けることになります。このケースでは、攻撃者は以下のフィールドと機能を使用して新しいEメールルールを構成しました:
- AlwaysDeleteOutlookRulesBlob - Outlook on the WebまたはPowershellを使用して受信トレイルールを編集する際の警告メッセージを非表示にします。これは、攻撃者が実行するコマンドのリストが決まっており、確認メッセージをクリックすることでアカウントの搾取に時間がかかることを避けたかったためと考えられます。
- Force - 警告または確認メッセージを非表示にします。
- MoveToFolder - Eメールをフォルダに移動します。これは、アカウントが攻撃者によってメール送信に使用されているという事実を隠すために、バウンスされたメールを受信トレイから遠ざけるためによく使用されます。
- 名前 - ルールの名前を指定します。この場合、シングルフルストップです。
- SubjectOrBodyContainsWords - キーワードを含むEメールがアクションされます。
- StopProcessingRules - このルールの条件が満たされた場合、後続のルールが処理されるかどうかを決定します。この場合、攻撃者はこれを false に設定し、疑惑を持たれないように後続のルールが処理されるようにしたと思われます。
その後、アカウントAがメール管理アプリ「Spike」に許可を与えていることが確認されました。これは、侵害されたアカウントの迅速な自動搾取を可能にするためと思われます。攻撃者は、アカウントの侵害から悪意のある使用までの時間を短縮するため、このプロセスを高速化し、セキュリティチームが対応する時間を短縮したいと考えています。

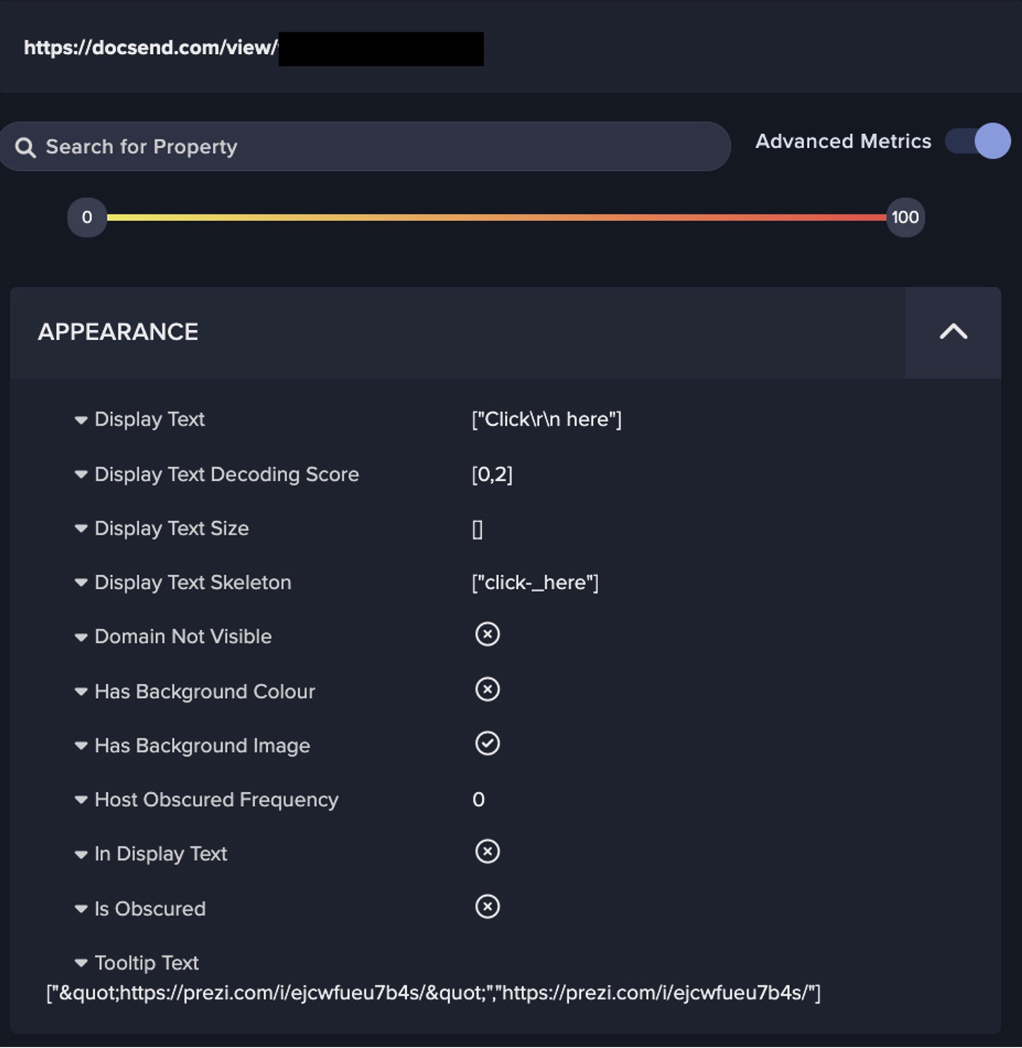
その後、このアカウントは15分間に794通のメールを社内外の受信者に送信していることが確認されました。これらのメールには、同じ件名や関連するフィッシングリンクなど、類似した性質がありました。この大量のスパムは、攻撃者が最短時間内にできるだけ多くのアカウントと認証情報を侵害したかったためと思われます。メールで送信されたリンクのドメインはspikenow[.]comで、「共有リンクを表示」というテキストで隠されていました。これは、攻撃者がメールの送信とフィッシングリンクのホスティングにSpikeを使用したことを示唆しています。


アカウントAからこの大量の送信メールが送信されてから15分以内に、ナイジェリアにある同じ稀なIPからアカウントBにアクセスされました。アカウントBはまた、シングルフルストップという名前の新しいEメールルールを作成しました。これまでのルールに加えて、以下のルールが観測されました:
- From - 特定のアドレスからのEメールがこのルールで処理されることを指定します。
- MarkAsRead - メールを既読としてマークすることを指定します。
フィッシングメールの送信とアカウントBの異常な挙動との間の時間枠が短いため、アカウントBが最初のフィッシング被害者であった可能性があります。

2022年2月10日
翌日、3つ目のアカウント(アカウントC)も同じく稀なIPからアクセスされました。これは2回発生し、1回はユーザーエージェントMozilla/5.0、もう1回はBAV2ROPCでした。13:08にBAV2ROPCでログインした後、このアカウントはメール管理アプリSpikeにアカウントAと同じ権限を与えました。その後、同じメールルールと思われるものが作成され、名前はシングルフルストップでした。アカウントBと同様に、このアカウントはアカウントAから送信されたフィッシングメールの1つによって侵害された可能性があります。

脅威アクターの動機は不明ですが、これは以下の結果を招いた可能性があります:
- 将来、組織に対して使用するため、またはサードパーティに売却するためのクレデンシャルハーベスティング。
- 専門的なウェブサイト(LinkedIn、Indeed)において侵害されたユーザーになりすまし、さらに企業アカウントをフィッシングした可能性:
- LinkedInで1人のユーザーの偽アカウントが発見された。
- この同じユーザーがIndeedに登録するEメールが、侵害の際に確認された。
攻撃は他のセキュリティスタックをどのようにすり抜けたか?
- Office 365の認証情報が侵害され、ユーザーエージェントBAV2ROPCが使用されていたため、MFAでは不審なログインを阻止することができませんでした。
- RESPONDは人間による確認を求める設定(Human Confirmation Mode)であったため、自律的なアクションを取ったことは確認できず、自律検知されたものだけが表示されました。アカウントAを無効にすれば、フィッシングメールとそれに続くアカウントBとCの侵害を防げた可能性は高かったでしょう。
- この組織は、DarktraceのProactive Threat Notification および Ask The Expertの各サービスに登録していなかったため、Darktrace SOC アナリストによるさらなるトリアージが可能であったはずです。
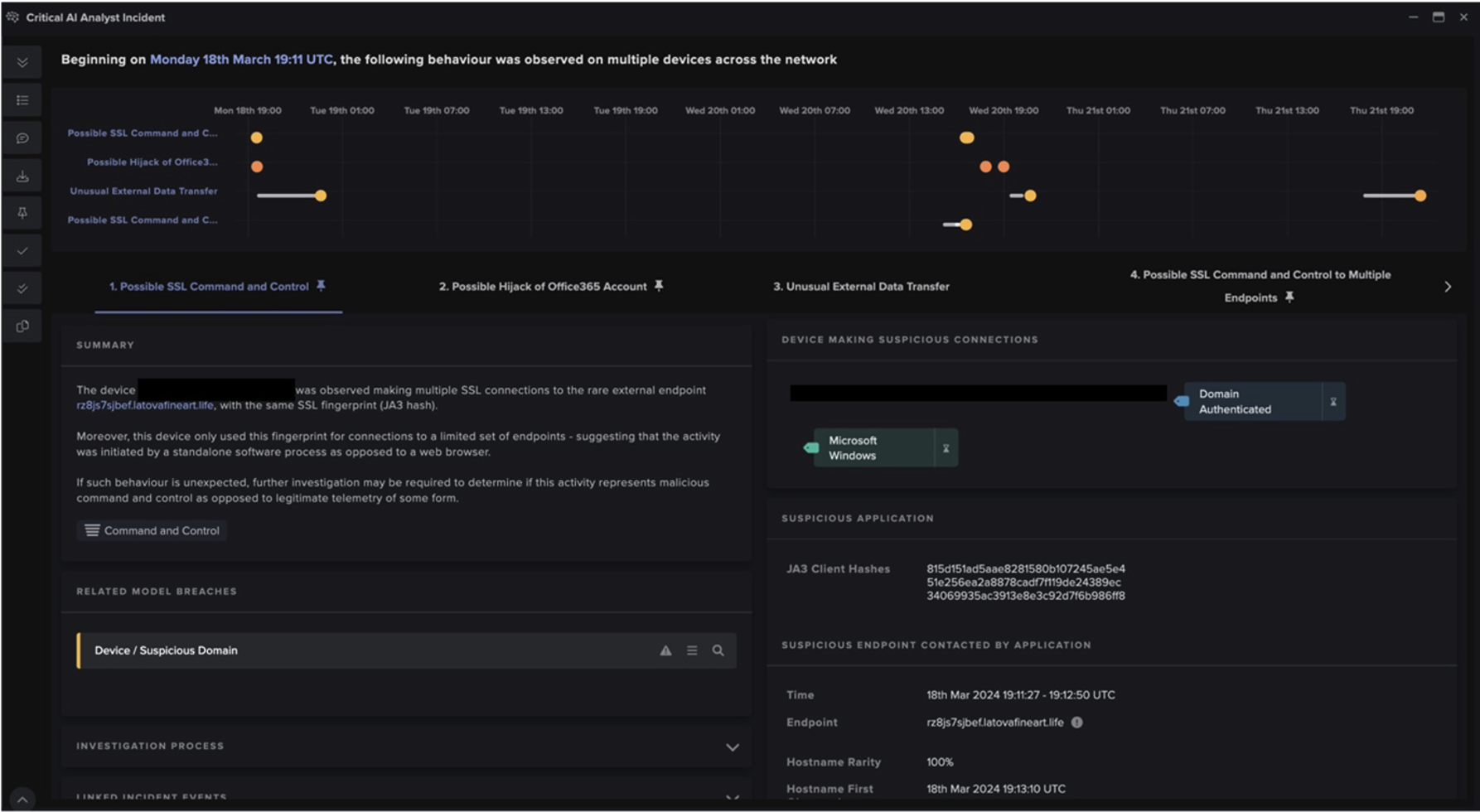
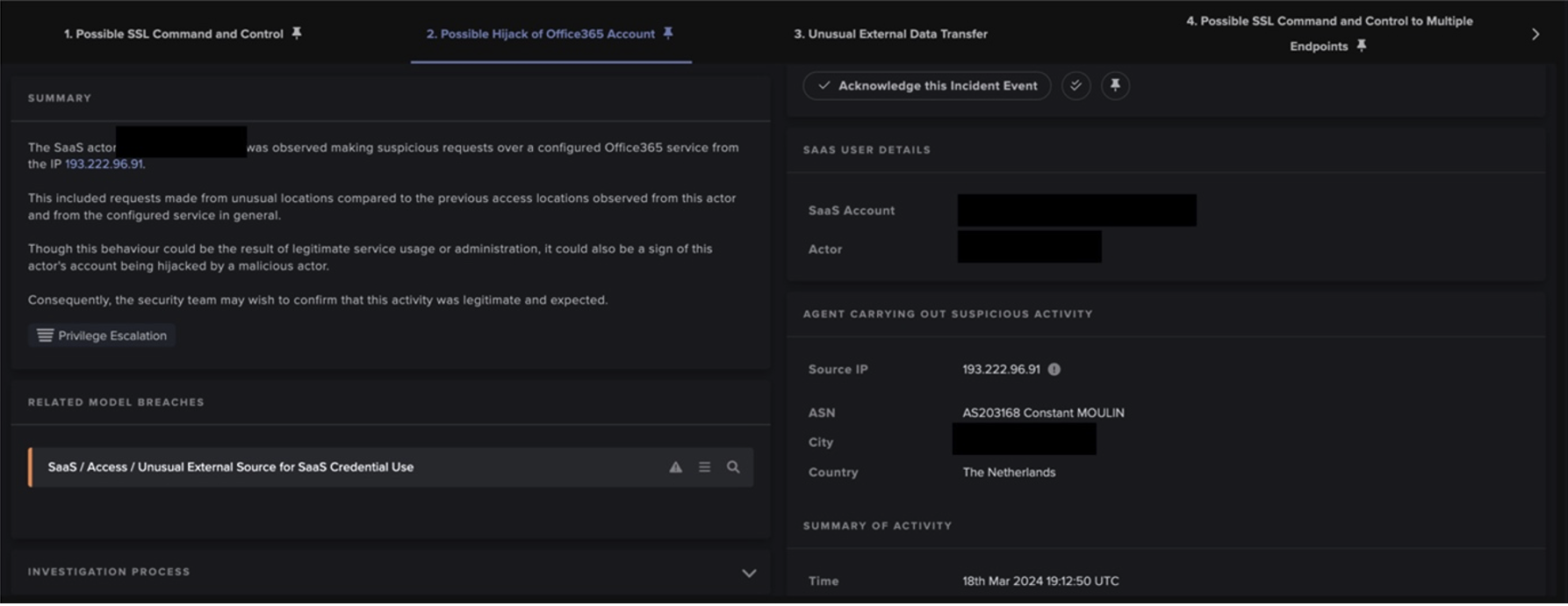
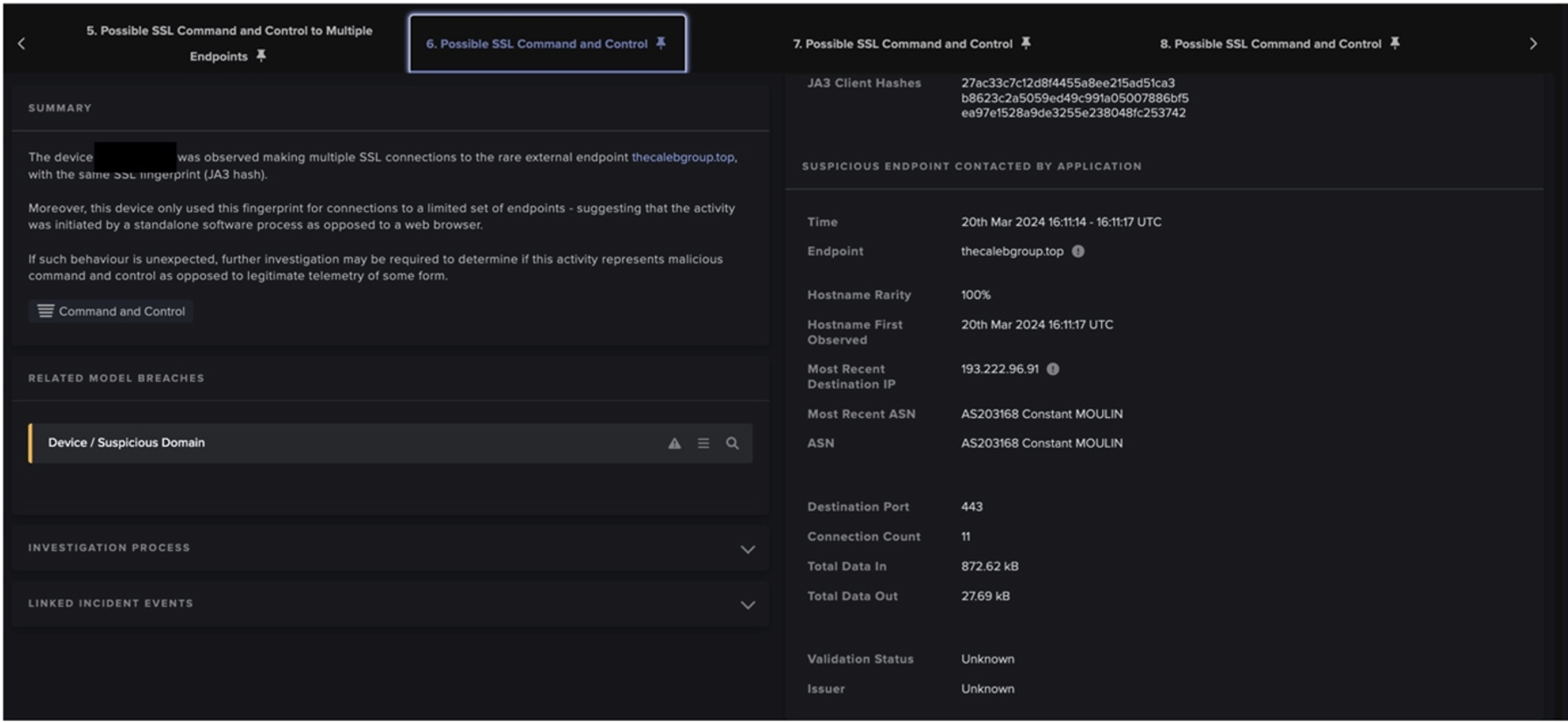
Cyber AI Analyst Investigates
DarktraceのCyber AI Analystは、人間を遥かに凌駕するスピードとスケールで調査を自動化し、関連するインシデントに即座に優先順位を付け、実用的なインサイトを自動作成することで、セキュリティチームが脅威を迅速に理解し、対処できるようにします。
In this case, AI Analyst automatically investigated all three account compromises, saving time for the customer’s security team and allowing them to quickly investigate the incident themselves in more detail. The technology also highlighted some of the viewed files by the compromised accounts which was not immediately obvious from the model breaches alone.



Darktrace RESPOND (Antigena) actions
問題の組織では、アクティブモードでRESPOND/Appsが設定されていなかったため、このケースでは何の対策も取ることができませんでした。下の表は、RESPOND が取ったであろう重要な防御アクションを示しています。

それにもかかわらず、自律遮断技術が有効になっていれば、RESPOND がいつ、どのようなアクションを取ったかを知ることができるのです。

上の表は、RESPONDが有効になっていれば、インシデントが発生している間、3名のユーザーすべてが無効になっていたことを示しています。ハイライトされた行は、内部フィッシングメールが送信されたときにアカウントAが無効化され、その後、侵害されたEメールアカウント(BとC)の連鎖を防げた可能性があることを示しています。
結論
SaaSアカウントは、企業の攻撃対象領域を大きく拡大します。侵害されたアカウントの悪用が迅速に行われるだけでなく、1つの侵害されたアカウントが社内のフィッシングキャンペーンを経由してさらなる侵害につながることもあります。このことは、既存のITチームを補完し、侵害の時点で脅威を軽減する自律的かつプロアクティブなセキュリティの継続的な必要性を補強しています。すべてのアカウントの「レガシー認証」を無効にし、MFAを提供することである程度の保護が得られますが、Darktrace/Appsはそれ以上の感染をすべてブロックする能力を備えています。
Credit to: Adam Stevens and Anthony Wong for their contributions.
付録
Darktraceによるモデル検知の一覧
ユーザーA - 2022年2月9日
- 04:55:51 UTC | SaaS / Access / Suspicious Login User-Agent
- 04:55:51 UTC | SaaS / Access / Unusual External Source for SaaS Credential Use
- 04:55:52 UTC | Antigena / SaaS / Antigena Suspicious SaaS and Email Activity Block
- 04:55:52 UTC | Antigena / SaaS / Antigena Suspicious SaaS Activity Block
- 14:16:48 UTC | SaaS / Compliance / New Email Rule
- 14:16:48 UTC | SaaS / Compromise / Unusual Login and New Email Rule
- 14:16:49 UTC | Antigena / SaaS / Antigena Significant Compliance Activity Block
- 14:16:49 UTC | Antigena / SaaS / Antigena Suspicious SaaS Activity Block
- 14:45:06 UTC | IaaS / Admin / Azure Application Administration Activities
- 14:45:07 UTC | SaaS / Admin / OAuth Permission Grant
- 14:45:07 UTC | Device / Multiple Model Breaches
- 14:45:08 UTC | SaaS / Compliance / Multiple Unusual SaaS Activities
- 15:03:25 UTC | SaaS / Email Nexus / Possible Outbound Email Spam
- 15:03:25 UTC | SaaS / Compromise / Unusual Login and Outbound Email Spam
ユーザーB - 2022年2月9日
- 15:18:21 UTC | SaaS / Compromise / Unusual Login and New Email Rule
- 15:18:21 UTC | SaaS / Compromise / Unusual Login and New Email Rule
- 15:18:22 UTC | Antigena / SaaS / Antigena Significant Compliance Activity Block
- 15:18:22 UTC | Antigena / SaaS / Antigena Suspicious SaaS Activity Block
ユーザーC - 2022年2月10日
- 14:25:20 UTC | SaaS / Admin / OAuth Permission Grant
- 14:38:09 UTC | SaaS / Compliance / New Email Rule
- 14:38:09 UTC | SaaS / Compromise / Unusual Login and New Email Rule
- 14:38:10 UTC | Antigena / SaaS / Antigena Significant Compliance Activity Block
- 14:38:10 UTC | Antigena / SaaS / Antigena Suspicious SaaS Activity Block

Refrences
1.https://www.ncsc.gov.uk/guidance/phishing#section_3
3.https://customerportal.darktrace.com/product-guides/main/antigena-saas-inhibitors