組織と第三者との間の信頼関係は、サイバー脅威アクターが機密ネットワークにアクセスするための標的として、ますます一般的になってきています。このような信頼関係は、通常、組織が外部または隣接するエンティティに付与し、ビジネス目的で内部リソースへのアクセスを許可するものです。
Several high-profile compromises have occurred due to the leveraging of privileged network access by such third parties. One prominent example is the 2016 DNC network attack, in which the trust between the Democratic Congressional Campaign Committee (DCCC) and the Democratic National Committee (DNC) was exploited. Supply chain attacks, which also leverage the implicit trust between IT vendors and customers, are also on the rise with some estimates projecting that by 2025, almost half of all organizations will be impact by supply chain compromises.2 These trends may also be attributed to the prevalence of remote work as well as the growth in IT-managed service providers.3
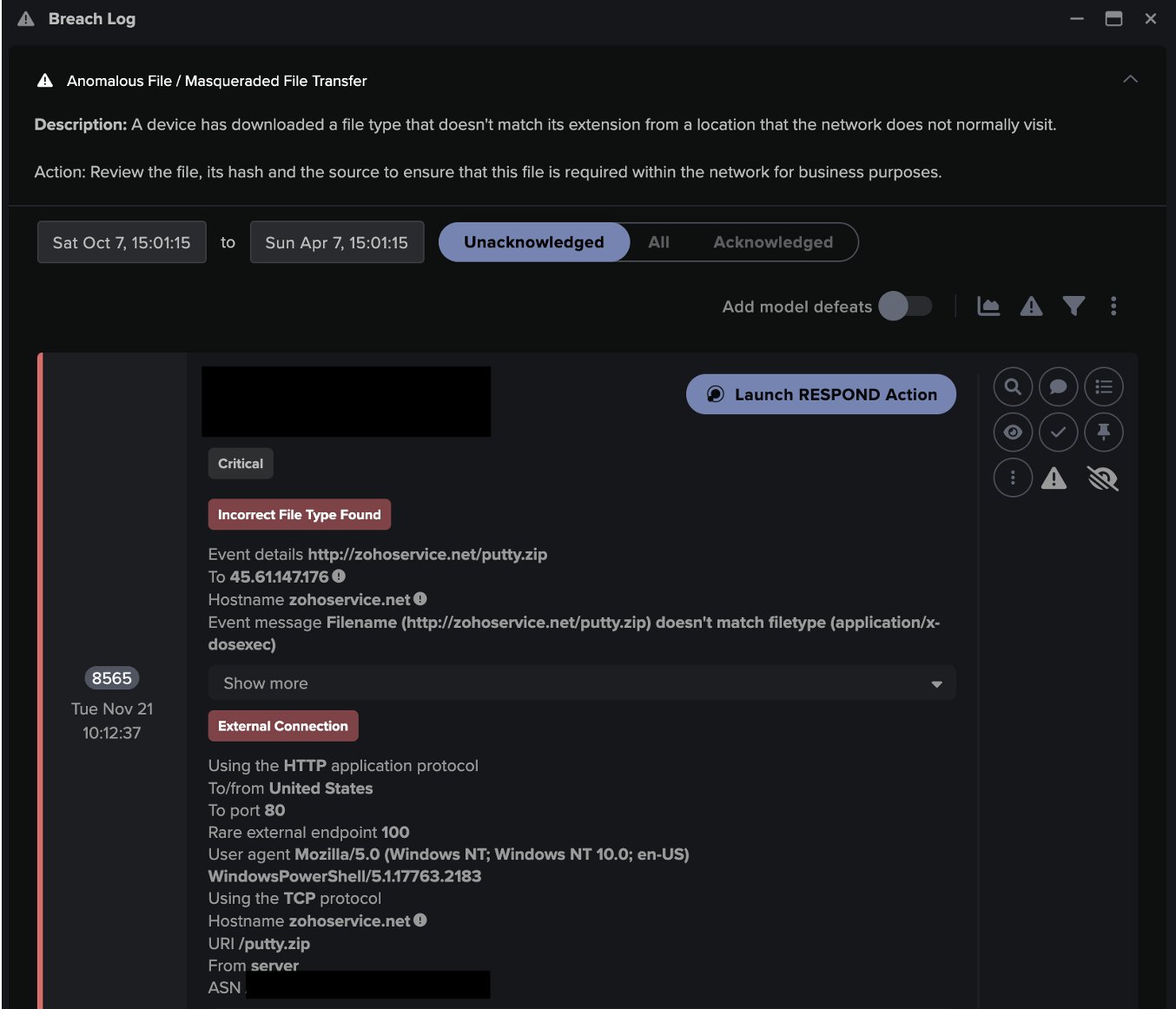
このようなネットワーク関係と脅威技術の性質を考慮すると、シグネチャベースの検知はこのような信頼悪用の特定と緩和において非常に不利であり、ネットワーク管理者は、ネットワークへのアクセスを必要とするIPをブロックするためにファイアウォールを使用することは容易ではありません。しかし、Darktrace DETECT™とその自己学習型AIは、このような侵害の特定と軽減に成功しています。2023年9月、Darktraceは医療機関のネットワーク上でこのような信頼関係の悪用に関わるインシデントを観測しました。
攻撃の概要
2023年9月上旬、あるDarktraceの顧客が、Ask the Expert™(ATE)サービスを通じてDarktraceセキュリティオペレーションセンター(SOC)に連絡し、ネットワーク上で検知された不審な活動に関する支援を要請しました。Darktraceは、顧客のセキュリティチームに、ネットワーク上に現れた未知のデバイスを警告し、偵察、ラテラルムーブメント、データ流出の試みなど、一連の予期せぬ活動を実行するように進めていました。
この顧客にとっては不運だったことは、Darktrace RESPOND™は、この侵害が発生した時点では自律遮断モードが有効になっていなかったため、RESPONDによって提案された予防措置は、事後的に顧客のセキュリティチームが手動で適用する必要がありました。それにもかかわらず、Darktrace による疑わしい活動の迅速な特定と SOC の調査により、侵入を初期段階で阻止し、より破壊的な侵害に発展するのを防ぐのに役立ちました。
初期アクセス
Darktraceは当初、顧客の内部ネットワーク内に、以前のパートナー組織のネットワークからのリモートアクセスを示唆するネットワークアドレス変換(NAT)IPアドレスで現れた新しいデバイスを観察しました。顧客によって実施されたさらなる調査により、パートナー組織内の貧弱なクレデンシャルポリシーが、仮想デスクトップインターフェース(VDI)マシンにアクセスするために攻撃者によって悪用された可能性が高いことが判明しました。
信頼できるアソシエイトのVDIアプライアンスを使用して、脅威アクターはNATリモートアクセスインフラを利用して顧客の環境にアクセスすることができました。顧客のネットワーク内のデバイスは、以前はパートナーネットワークからのリモートアクセスに利用されていました。それ以来、このネットワークへのアクセスはすべての関係者から排除されたと思われていましたが、リモートアクセス機能は稼動したままであることが明らかになりました。顧客は環境内にファイアウォールも設置していましたが、攻撃時の設定ミスにより、リモート環境へのインバウンドポートアクセスが許可され、2023年8月29日に不審なデバイスがネットワークに接続されました。
内部偵察
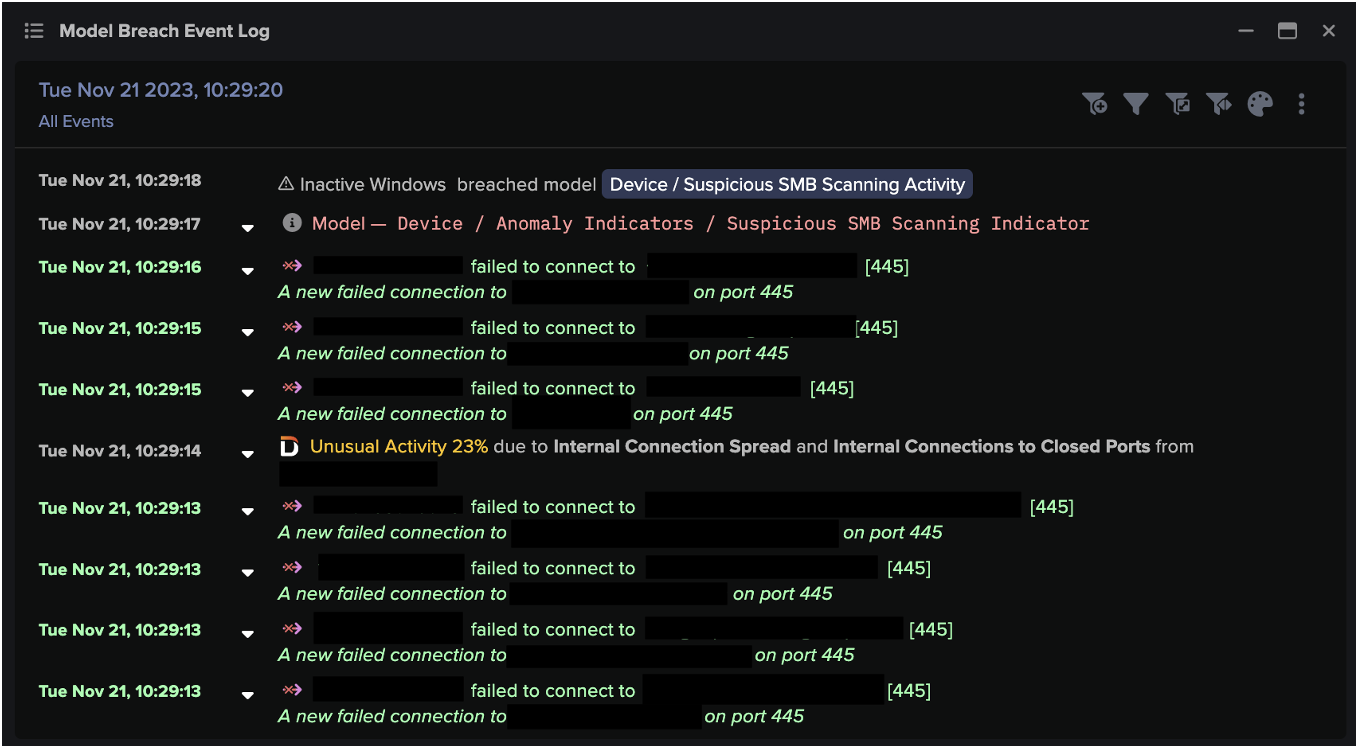
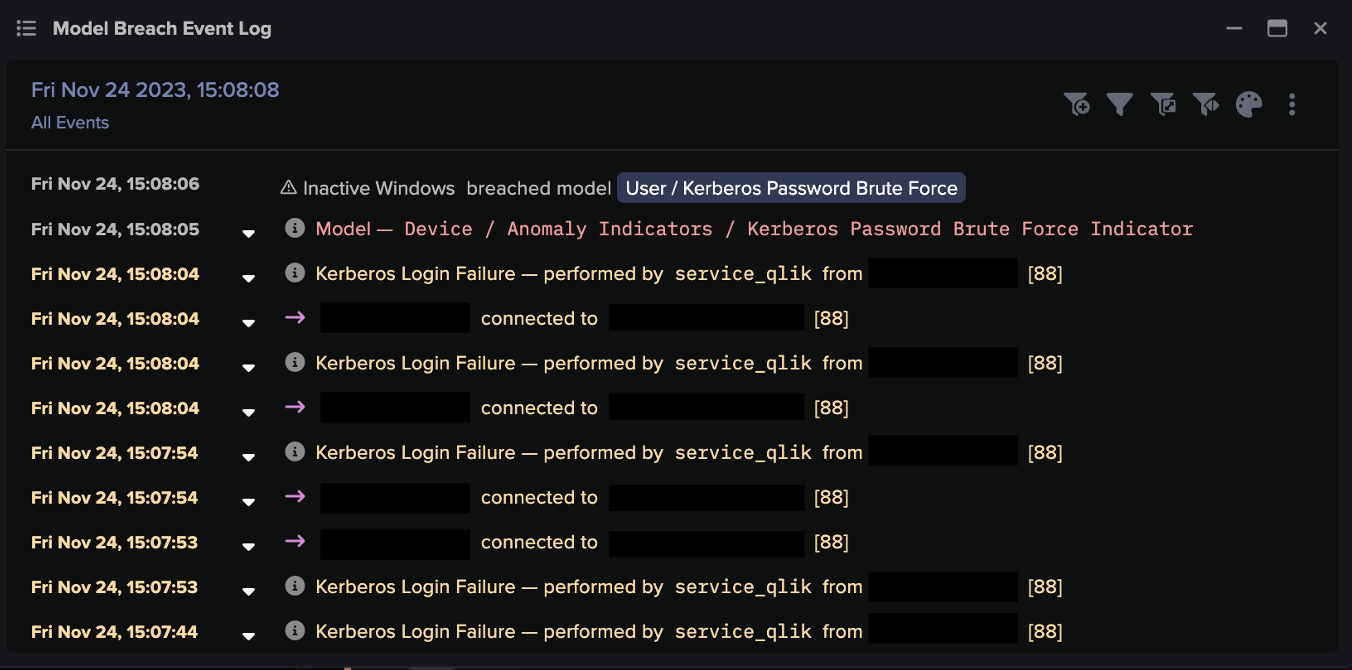
このデバイスがネットワークに接続した直後、Darktraceはこのデバイスが一連の内部偵察活動を実行しているのを観測しました。このアクティビティは、内部ICMPアドレス接続で開始され、SMB、RDP、HTTP、RPC、SSLなどの重要なサービスに関連するさまざまなポートへの内部TCP接続試行が続きました。また、このデバイスが特権クレデンシャルを使用しようとしていることも検知されましたが、このクレデンシャルは後に一般的な多目的管理アカウントに関連するものであることが特定されました。脅威アクターは、さらに6つのユーザー認証情報を使用しようとしながら、DNSの逆引きを含む内部偵察を進めました。
広範な内部接続に加え、DarktraceはRDPとSMBプロトコルに焦点を当てた持続的な接続試行を観測しました。Darktraceはまた、攻撃者の偵察のこの段階で、追加のSMB列挙を検知しました。この偵察活動は、利用可能な共有タイプと集約に利用可能な情報を特定するために、ホストによって以前は見られなかった多種多様なSMB共有へのアクセスを主に試みました。そのため、侵入ホストは、extramedwb というクレデンシャルを使用して、さまざまな内部ホストのサーバーサービス(srvsvc)エンドポイントにSMB書き込みを大量に行いました。このエンドポイントへの SMB 書き込みは、伝統的にバインディングの試みを示しています。
8月31日から、Darktraceは前述のNAT IPアドレスに関連する新しいホストを特定しました。この新しいホストは、VDIインフラストラクチャを利用してネットワーク上で偵察とラテラルムーブメントを行う主要なホストとして引き継がれたようです。以前のホストと同様に、このホストも8月31日に偵察活動を継続していることが確認されており、SMBの列挙、SMBアクセスの失敗、RDP接続の試行、DNSの逆引きが行われていました。 攻撃者は、偵察の実行のために、"auditor" や "administrator" などの一般的でおそらくデフォルトの管理者認証情報を含む複数の認証情報を利用していました。

Following these initial detections by Darktrace DETECT, Darktrace’s Cyber AI Analyst™ launched an autonomous investigation into the scanning and privileged internal connectivity and linked these seemingly separate events together into one wider internal reconnaissance incident.

ラテラルムーブメント
リモートアクセスインフラストラクチャを悪用して観測された新しいホストによって実行された偵察活動の後、Darktraceは、特にRPCコマンドとSMBファイル書き込みを介して、顧客のネットワーク内で横方向に移動しようとする試みの増加を検知しました。
具体的には、この脅威アクターは、複数の宛先デバイスに対してRPCバインドを試みていることが確認されており、このRPCバインドは、宛先デバイス上でコマンドの呼び出しやサービスの作成に使用される可能性があります。このアクティビティは、ネットワーク内の複数の宛先デバイスでntsvcsという名前のパイプへのバインドに何度も失敗していることで浮き彫りになりました。しかし、多数の接続試行があったことから、Darktraceは成功したRPC接続も多数検知しました。
Darktrace はまた、違反デバイスから一般的でないサービス制御(SVCCTL)の ExecMethod、Create、および Start サービス操作の急増を検知しました。

さらに、SMB/NTLM プロトコルを使用したラテラルムーブメントが行われました。また、感染したデバイスは、一連の匿名 NTLM ログイン(クライアントプリンシパルを指定せずに NTLM 認証を試行する)を内部ホストに対して実施していました。このような行為は、ネットワーク上で悪意のある、あるいは不正な行為が行われていることを強く示唆するものです。このホストはまた、キルチェーンのこの段階で、古い SMB バージョン 1 (SMBv1) プロトコルを使用していました。SMBv1の使用は、このバージョンのプロトコルに関連する悪用可能な脆弱性が多いため、ほとんどのネットワークでコンプライアンス上の問題になることが多いです。
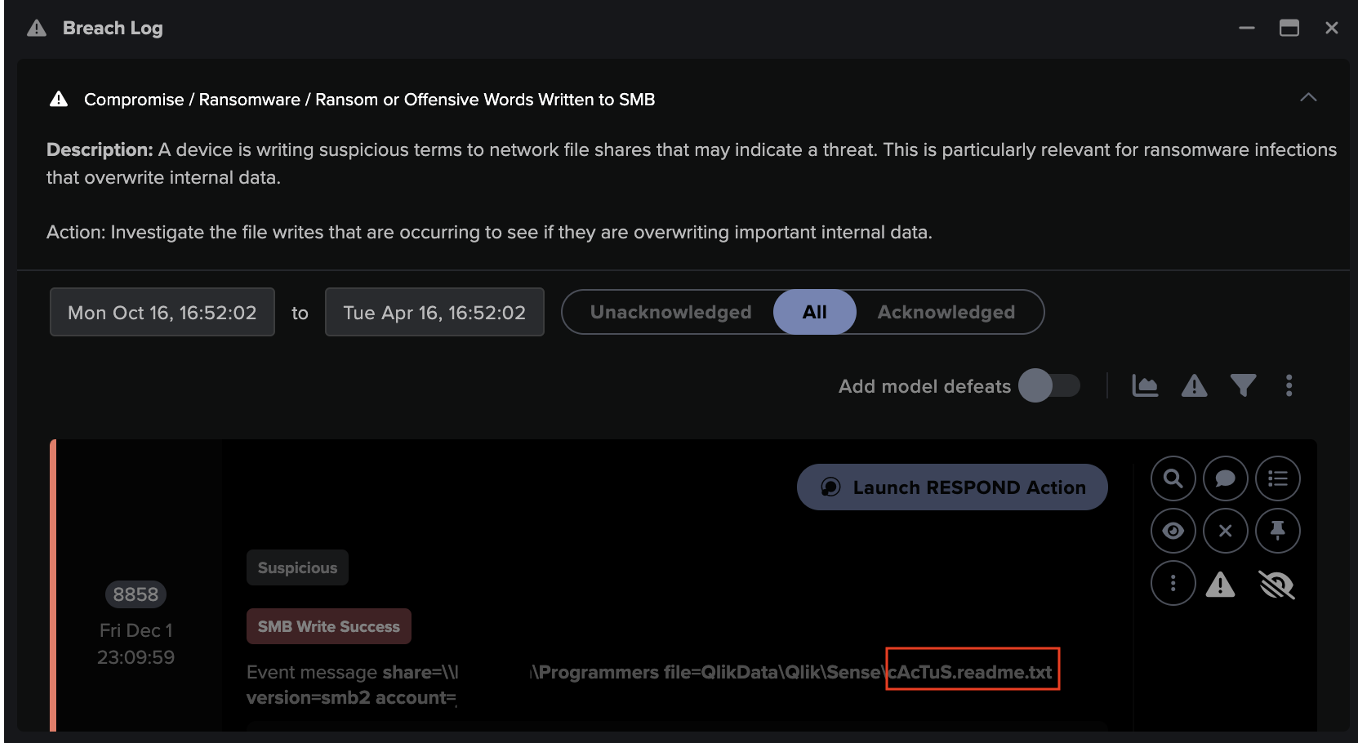
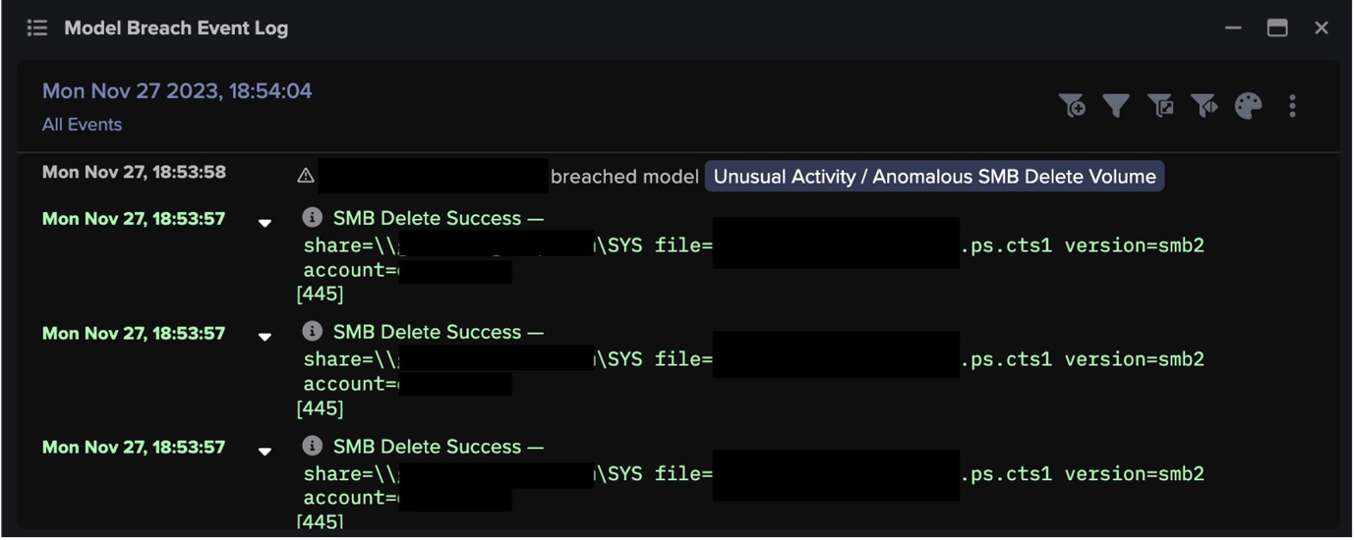
最後に、Darktraceは、SMB書き込みによる TRMtZSqo.exe などの一般的でない実行ファイルの内部転送を確認しました。違反デバイスは、このファイルを宛先サーバーの隠し管理共有(ADMIN$)に書き込むことが観察されました。Darktraceは、このアクティビティがデバイスにとって非常に異例であり、脅威アクターが、さらなる永続化、データ集約、および/またはコマンド&コントロール(C2)操作のために、悪意のあるペイロードを宛先サーバーに転送していることを表している可能性があることを認識しました。この時、デバイスから実行可能ファイルのさらなる SMB 書き込みと、それに続くこれらのバイナリの削除が観測されました。例えば、追加の実行可能ファイル JAqfhBEB.exe が侵害デバイスによって削除されているのが確認されました。この削除は、SVCCTL の作成および開始操作の急増と相まって、ネットワーク内で永続化バイナリとデータハーベスティングバイナリが転送、実行、削除されたことを示唆しています。

結論
最終的に、Darktraceは信頼関係を悪用して顧客のネットワークに不正アクセスした脅威アクターによる不審な活動を特定し、警告することに成功しました。
スキャン、RPCコマンド、SMBセッションの特定は、この侵入を封じ込め、軽減するための対応において、顧客を直接支援しました。Darktrace SOC が実施した調査により、顧客は攻撃を迅速にトリアージして修復し、潜在的な損害を軽減し、侵害がさらに拡大するのを防ぐことができました。もしDarktrace RESPONDが攻撃時に自律遮断モードが有効になっていれば、スキャン、共有列挙、ファイル書き込み活動を抑制するための迅速な行動を取ることができ、それによって攻撃者のネットワーク偵察と横移動の試みを阻止することができたでしょう。
組織間の信頼関係を悪用することで、脅威アクターは多くの場合、特定のエンドポイントからの接続を許可し、信頼するように再設定された従来のシグネチャベースのセキュリティ手法を回避することができます。特定のルールや許可されたIPアドレス、ポート、デバイスの設定に依存するのではなく、脅威検知に対するDarktrace DETECTのアノマリベースのアプローチは、問題のあるデバイスやドメインまたは関係が信頼されているかどうかに関係なく、最も早い段階で疑わしいネットワークアクティビティを特定できることを意味しました。
寄稿者:Adam Potter(Cyber Security Analyst)、Taylor Breland(Analyst Team Lead, San Francisco)
Darktrace DETECT モデルブリーチの適用範囲:
- Device / ICMP Address Scan
- Device / Network Scan
- Device / Suspicious SMB Scanning Activity
- Device / RDP Scan
- Device / Possible SMB/NTLM Reconnaissance
- Device / Reverse DNS Sweep
- Anomalous Connection / SMB Enumeration
- Device / Large Number of Model Breaches
- Anomalous Connection / Suspicious Activity On High Risk Device
- Unusual Activity / Possible RPC Recon Activity
- Device / Anonymous NTLM Logins
- Anomalous Connection / Unusual SMB Version 1 Connectivity
- Device / Repeated Unknown RPC Service Bind Errors
- Anomalous Connection / New or Uncommon Service Control
- Compliance / SMB Drive Write
- Anomalous File / Internal / Unusual Internal EXE File Transfer
- Device / Multiple Lateral Movement Model Breaches
AI Analyst のインシデント:
- Scanning of Multiple Devices
- Extensive Unusual RDPConnections
- SMB Write of Suspicious File
- Suspicious DCE-RPC Activity
MITRE ATT&CK マッピング
- Tactic: Initial Access
- Technique: T1199 - Trusted Relationship
- Tactic: Discovery
- Technique:
- T1018 - Remote System Discovery
- T1046 - Network Service Discovery
- T1135 - Network Share Discovery
- T1083 - File and Directory Discovery
- Tactic: Lateral Movement
- Technique:
- T1570 - Lateral Tool Transfer
- T1021 - Remote Services
- T1021.002 - SMB/Windows Admin Shares
- T1021.003 - Distributed Component Object Model
- T1550 - Use Alternate Authentication Material
参考文献
1https://attack.mitre.org/techniques/T1199/
2https://www.cloudflare.com/learning/insights-supply-chain-attacks/






























![Cyber AI Analyst Incident Log showing the offending device making over 1,000 connections to the suspicious hostname “zohoservice[.]net” over port 8383, within a specific period.](https://assets-global.website-files.com/626ff4d25aca2edf4325ff97/662971c1cf09890fd46729a1_Screenshot%202024-04-24%20at%201.55.10%20PM.png)