2021年6月から2022年6月にかけて、世界中の暗号通貨プラットフォームは、パスワードやアカウント回復フレーズを盗むことから、クリプトジャッキングや暗号通貨取引を直接狙うに至るまで、手口がさまざまなサイバー犯罪者によって推定440億米ドルを失ったとされています。
最近、サイバー犯罪者が情報窃取マルウェアを使用して機密性の高い暗号通貨ウォレットの詳細を収集・流出させ、最終的に多額のデジタル通貨を窃取するという事例が増加しています。潜在的な侵害を検知して対応できる自律的な意思決定能力を持つことは、暗号通貨ウォレットと取引を攻撃者から保護するために極めて重要です。
2022年後半、Darktrace は、複数の脅威アクターが、顧客ベース全体の暗号通貨ユーザーを標的とする斬新な攻撃手法を採用し、特にLaplas Clipperマルウェアの最新バージョンであることを確認しました。自己学習型AIを駆使して、Darktrace DETECT/Network™とDarktrace RESPOND/Network™は、Laplas Clipperの活動を発見して緩和し、多額のデジタル通貨の盗難を防ぐために介入することができました。
Laplas Clipperの背景
Laplas Clipperは、情報窃取マルウェアの一種で、被害者の暗号通貨ウォレットから脅威アクターのウォレットに暗号通貨トランザクションを流用することで動作します [1]。Laplas Clipperは、さまざまな脅威アクターが購入して使用できるMalware-as-a-Service(MaaS)製品です。2022年10月に180のサンプルが特定され、別のマルウェア株、すなわちSmokeLoader [2] とリンクされたときから、野生で観察されています。このローダー自体は、少なくとも2011年から観測されており、一般的なマルウェア株の配信メカニズムとして機能しています [3]。
SmokeLoaderは通常、スパムメールや標的型フィッシングキャンペーンで送信される悪意のある添付ファイルを通じて配布されますが、ファイルホスティングページや偽装されたWebサイトからユーザーが直接ダウンロードすることもできます。SmokeLoaderは、フィッシングメールに添付されたMicrosoft Word文書またはPDFファイルとしてダウンロードされたBatLoaderスクリプトを介して、侵害されたデバイスにLaplas Clipperを特別に配信することが知られています。これらのソーシャルエンジニアリングの例は、ユーザーにマルウェアをダウンロードさせることを目的とした比較的手間のかからない手法であり、その後、Explorer.exeプロセスに悪意のあるコードを注入し、最終的にLaplas Clipperをダウンロードさせます。
Darktraceの顧客ベースで観察された Laplas Clipper の活動は、通常、SmokeLoader が Laplas Clipper のコマンド&コントロール(C2)インフラストラクチャに HTTP GET リクエストを行うことから始まります。ダウンロードされると、クリッパーは build[.]exe モジュールをロードし、被害者のクリップボードに暗号通貨のウォレットアドレスがないか監視を開始します。ウォレットアドレスが特定された場合、感染したデバイスはLaplas Clipperに関連するサーバーに接続し、脅威アクターに属するウォレットアドレスをダウンロードします。脅威アクターのアドレスは、通常、検知を回避するために、置き換えられるアドレスと同様に見えるように偽装されます。マルウェアはクリップボードのアクティビティを更新し続け、暗号通貨取引のために財布のアドレスがコピーされるたびに、ユーザーのウォレットのアドレスをなりすましたアドレスに置き換えます。
Darktrace によるLaplas Clipper のカバレッジとその配信方法
2022年10月と11月に、Darktrace は複数の顧客ネットワークでLaplas Clipperに関連する不審なアクティビティが大幅に増加したことを確認しました。この活動は、主に以下の内容で構成されていました:
- 不審なエンドポイントに接続するユーザーデバイス
- ユーザー端末にインストールされたマルウェア SmokeLoader に関連するエンドポイントにHTTP GETリクエストを行う
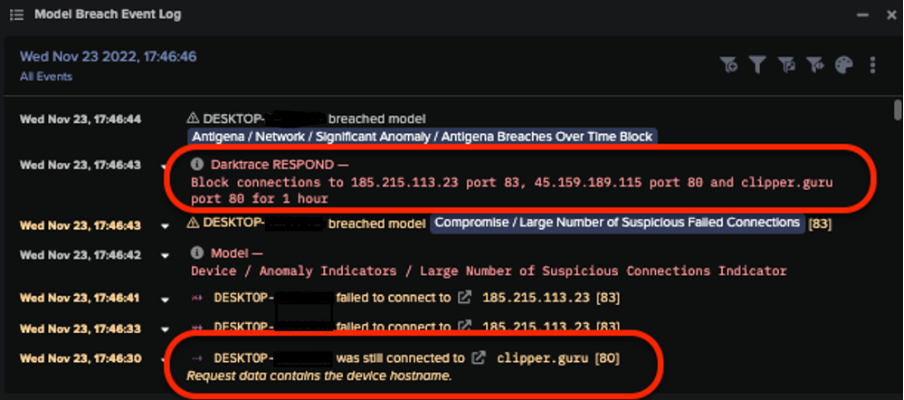
- ユーザー端末がLaplas Clipperダウンロードサーバー clipper[.]guru にHTTP接続を行い、そこから暗号通貨の支払いを迂回させるために詐称したウォレットアドレスをダウンロードさせる
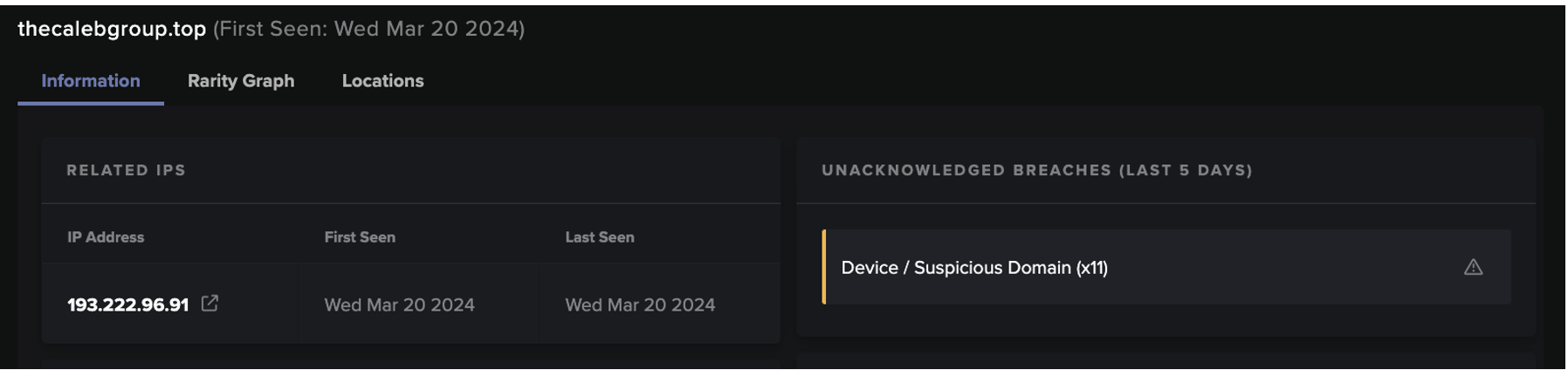
ある特定の事例では、Laplas Clipperダウンロードサーバーに接続する直前に、感染したデバイスがSmokeLoaderに関連するエンドポイントに接続することが確認されました。その他の例では、デバイスがshonalanital[.]com、transfer[.]sh、pc-world[.]ukというドメインを含む他の異常なエンドポイントに接続することが検知され、正規のエンドポイントである thepcworld[.]com を模倣しているようでした。
さらに、一部の侵害されたデバイスは、RedLine スティーラーマルウェアに関連する193.169.255[.]78 および 185.215.113[.]23 などの悪意のあるIPアドレスに接続しようとすることが確認されました。さらに、Darktrace は、SmokeLoaderに関連するIPアドレス 195.178.120[.]154 および 195.178.120[.]154、オープンソース情報がCobalt Strikeに関連する 5.61.62[.] 241 への接続も確認されています。


これらの接続に対応して、以下のDETECT/Networkのモデルが侵害されました:
- Compromise / Beacon to Young Endpoint
- Compromise / Slow Beaconing Activity to External Rare
- Compromise / Beacon for 4 Days
- Compromise / Beaconing Activity to External Rare
- Compromise / Sustained TCP Beaconing Activity to Rare Endpoint
- Anomalous Connection / Multiple Failed Connections to Rare Endpoints
- Compromise / Large Number of Suspicious Failed Connections
- Compromise / HTTP Beaconing to Rare Destination
- Compromise / Post and Beacon to Rare External
- Anomalous Connection / Callback on Web Facing Device
DETECT/Networkは、IOCs(侵害指標)の静的なリストではなく、デバイスの通常の行動パターンに基づいて動作するモデルであるため、このような活動を識別することができます。そのため、Darktraceは新たに作成された悪意のあるエンドポイントやC2インフラに接続することで、期待される行動パターンから逸脱した侵害デバイスを迅速に特定し、アラートを発することができます。
一例として、RESPOND/Networkは、Laplas Clipper C2サーバーに接続しようとする危険なデバイスを自律的に傍受し、SmokeLoader、ひいてはLaplas Clipper自体のダウンロードを阻止しました。
別の例では、DETECT/Networkは、感染したデバイスがMoneroデジタル通貨に関連する暗号通貨マイニングプールに対して多数のDNSリクエストを実行しようとしていることを確認しました。
この活動により、以下のDETECT/Networkモデルが侵害されました:
- Compromise / Monero Mining
- Compromise / High Priority Crypto Currency Mining
RESPOND/Network はすぐに介入し、デバイスにあらかじめ確立された生活パターンを適用し、予期せぬ活動を行えないようにし、問題のエンドポイントへの接続を1時間にわたってブロックしました。Darktraceの自律遮断技術によって実行されたこれらのアクションは、感染したデバイスが暗号マイニング活動を行うことを防ぎ、脅威者が追加の悪意ある活動を行うことができないようにしました。

最後に、RESPOND/Networkが稼働しない場合でも、Laplas Clipper C2サーバーへの外部接続はDETECT/Networkによって監視され、お客様のセキュリティチームにインシデントが通知されました。
結論
Laplas Clipperのような情報窃取型マルウェアの増加は、マルウェアのエコシステムにおける暗号通貨と暗号通貨マイニングの重要性を明らかにし、サイバーセキュリティの重要な懸念事項としてより広範に認識されるようになりました。しかし、Laplas Clipperのようなマルウェアは、暗号通貨に焦点を当てた脅威アクターがデジタル資産にもたらす真のセキュリティリスクを示しています。
自己学習型AIを活用し、DETECT/NetworkとRESPOND/Networkが連携して、疑わしいエンドポイントへの接続を素早く特定し、悪意のあるソフトウェアがダウンロードされる前にブロックし、お客様の安全を守ることができるようになりました。
付録
IoC一覧
a720efe2b3ef7735efd77de698a5576b36068d07 - SHA1 Filehash - Laplas Malware Download
conhost.exe - URI - Laplas Malware Download
185.223.93.133 - IP Address - Laplas C2 Endpoint
185.223.93.251 - IP Address - Laplas C2 Endpoint
45.159.189.115 - IP Address - Laplas C2 Endpoint
79.137.204.208 - IP Address - Laplas C2 Endpoint
5.61.62.241 - IP Address - Laplas C2 Endpoint
clipper.guru - URI - Laplas C2 URI
/bot/online?guid= - URI - Laplas C2 URI
/bot/regex?key= - URI - Laplas C2 URI
/bot/get?address - URI - Laplas C2 URI
Mitre Attack とマッピング
初期アクセス:
T1189 – Drive By Compromise
T1566/002 - Spearphishing
リソース開発:
T1588 / 001 - Malware
Ingress転送ツール:
T1105 – Ingress Tool Transfer
コマンド&コントロール:
T1071/001 – Web Protocols
T1071 – Application Layer Protocol
T1008 – Fallback Channels
T1104 – Multi-Stage Channels
T1571 – Non-Standard Port
T1102/003 – One-Way Communication
T1573 – Encrypted Channel
永続性:
T1176 – Browser Extensions
収集:
T1185 – Man in the Browser
持ち出し:
T1041 – Exfiltration over C2 Channel
参考文献
[1] https://blog.cyble.com/2022/11/02/new-laplas-clipper-distributed-by-smokeloader/
[2] https://thehackernews.com/2022/11/new-laplas-clipper-malware-targeting.html