ほんの数年前、一般的な報道では、「スマッシュ・アンド・グラブ攻撃」の時代は終わり、より巧妙で「ロー・アンド・スロー」な手口を使う新種のハッカーが台頭してきたと発表されました [1]。このような攻撃は間違いなく出現していますが、スマート・アンド・グラブはすぐに見過ごされるようになり、おそらく心配な結果を招いています。昨年、Googleは、Cookieを盗むマルウェアを使用したフィッシングキャンペーンを繰り返し行い、最近では、2022年のウクライナ紛争において、同様の技術を使用したハッカーが確認されたという報告があります [2 & 3]。彼らのインスピレーションはどこから来ているのでしょうか。2021年夏に初めて登場したBlackMatterのような大規模なAPTグループにとって、スマッシュ・アンド・グラブは決して流行り廃りのあるものではありません。
このブログでは、2021年にDarktrace を試用していたある組織を襲った BlackMatter ランサムウェア攻撃について解剖しています。このインシデントは、セキュリティチームが優先度の高いアラートに反応しない場合に何が起こるかを明らかにするものです。
ランサムウェアの攻撃全体がわずか48時間の間に実行される可能性がある場合、脅威が拡大する前に検知に反応して被害を防ぐためにセキュリティチームに頼ることは高いリスクがあります。その導入にはためらいがありますが [4]、このブログでも、Darktrace RESPOND のような自律遮断ソリューションの必要性を示しています。
ネーム・ゲーム:BlackMatter、REvil、DarkSide
表面上は短命の犯罪組織であるにもかかわらず [5]、新しいBlackMatterグループのTTP(戦術、技術、手順)と引退したREvilやDarkSideの組織のTTPの間には、現在多くの類似性が描かれています [6]。
DarkSideとREvilは、引退する以前は、おそらくサイバー犯罪集団の中で最も著名なブランドとして、昨年最も破壊的なランサムウェア攻撃のうちの2つを担当していました。DarkSideは、Colonial Pipelineの攻撃から2週間足らずで、その活動を停止することを発表しました [7]。一方、FBIは、7月4日のKaseya攻撃で壊滅的な被害を受け、9月に復帰に失敗した後、2022年1月にREvilをシャットダウンしました [8]。現在では、どちらか、あるいは双方のメンバーがBlackMatterを結成することになったのではないかと疑われています。
このようなリブランディング戦略は、現在、これらのグループが採用することが多くなっている「スマッシュ・アンド・グラブ」攻撃と類似しています。数日後、数週間後、数か月後に戻ってきたときには、自分自身や自分たちの攻撃を認識できないほど小さな変化を遂げています。このように、DarkSideはBlackMatterとなり、その攻撃は、過去に遭遇した脅威について訓練されたセキュリティシステムをすり抜けることができるのです。
攻撃の詳細
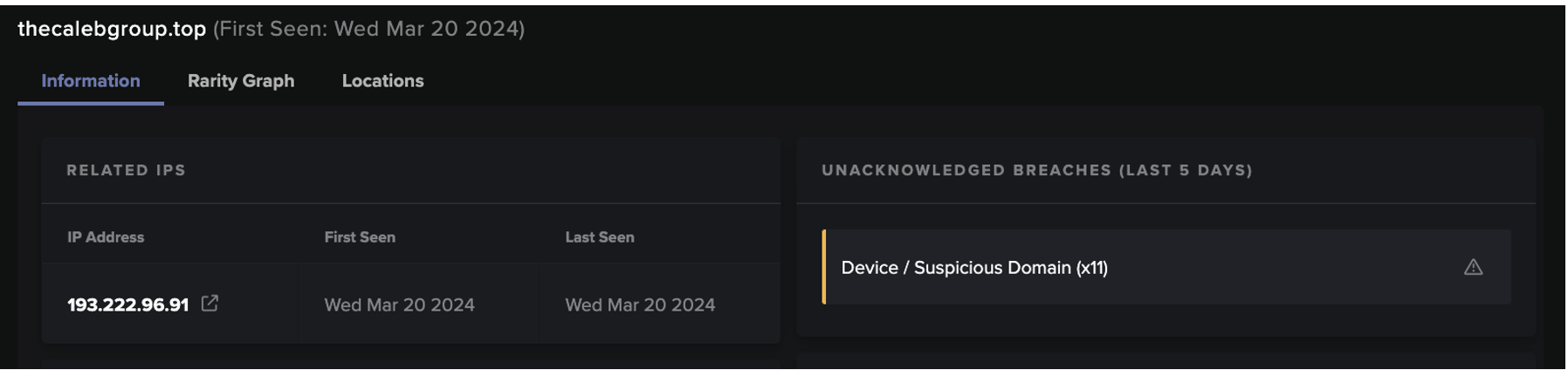
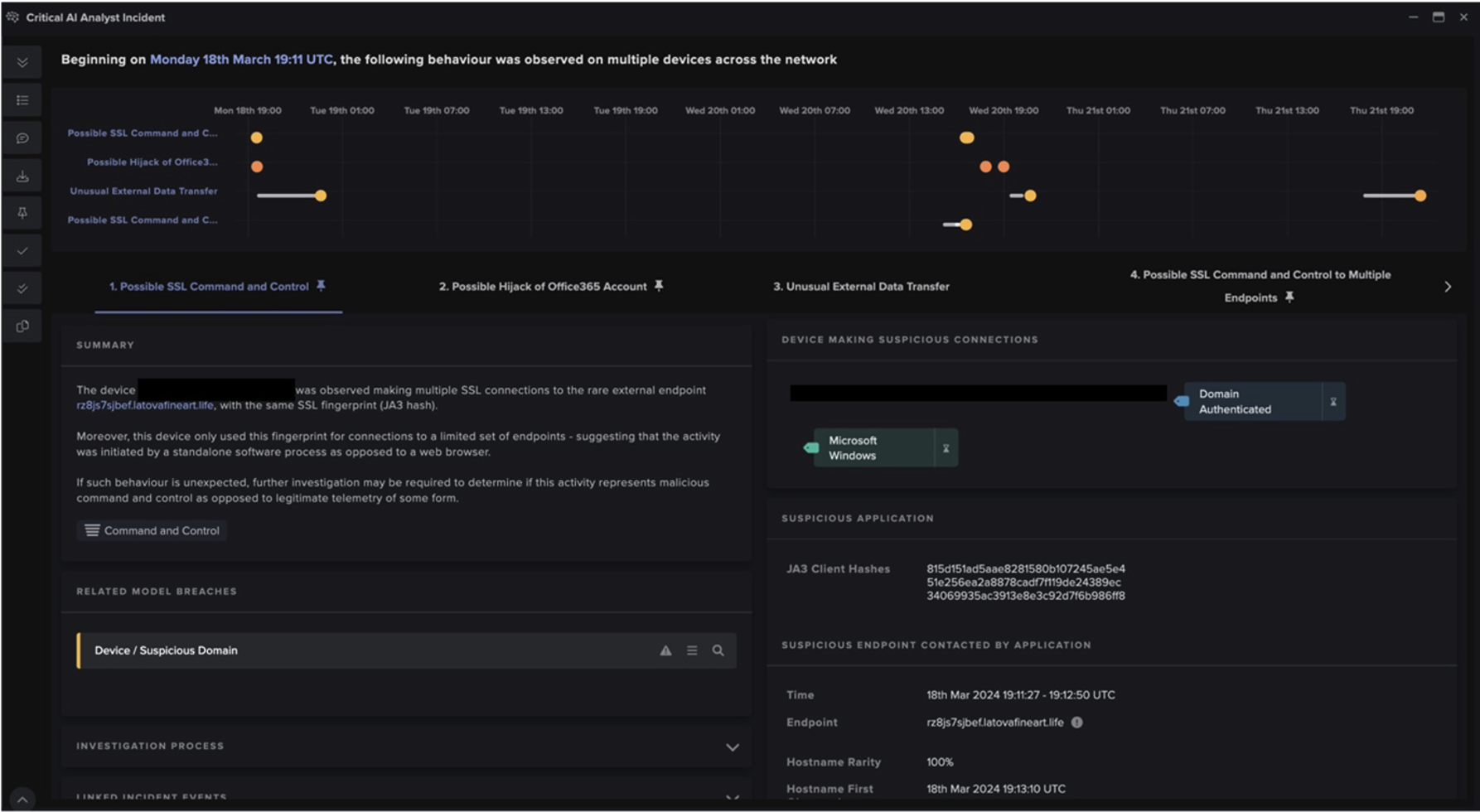
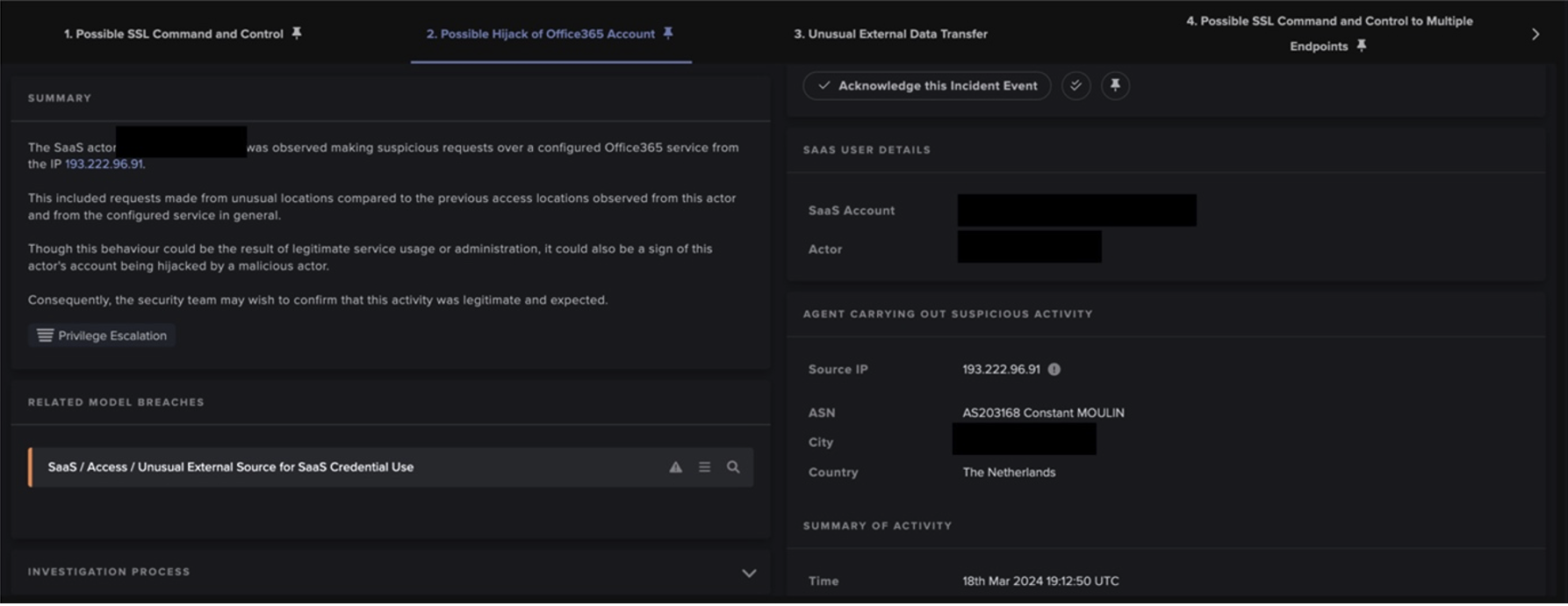
2021年9月、Darktrace は米国のマーケティング会社を監視していましたが、BlackMatter の活動の特徴を示す二重の強奪ランサムウェア攻撃の犠牲となりました。この攻撃は、ドメイン認証された1台のデバイスが同社のネットワークに参加したことから始まりました。これは、事前に感染していた会社のデバイスが、しばらくオフラインの状態から再接続されたものと思われます。
参加からわずか15分後、デバイスは1,000以上の異なる内部IPに対してSMBとICMPのスキャン活動を開始しました。また、Epmapperへのリクエストも急増し、RPCベースのラテラルムーブメントの意図があることが示唆されました。1つのクレデンシャルが特に目立っていましたが、管理者クレデンシャルを含む複数のクレデンシャルが使用されていました。この偵察は予想外の性質を持っていたため、すぐにDETECT/Network モデルブリーチの連鎖を引き起こし、DarktraceのSOC は Proactive Threat Notification サービスを通じて警告を発しました。SOCのアナリストは活動のトリアージを開始しましたが、同社は受け取ったアラートのいずれにも対応できず、検知された脅威は同社のデジタル環境に根を下ろしたままとなりました。
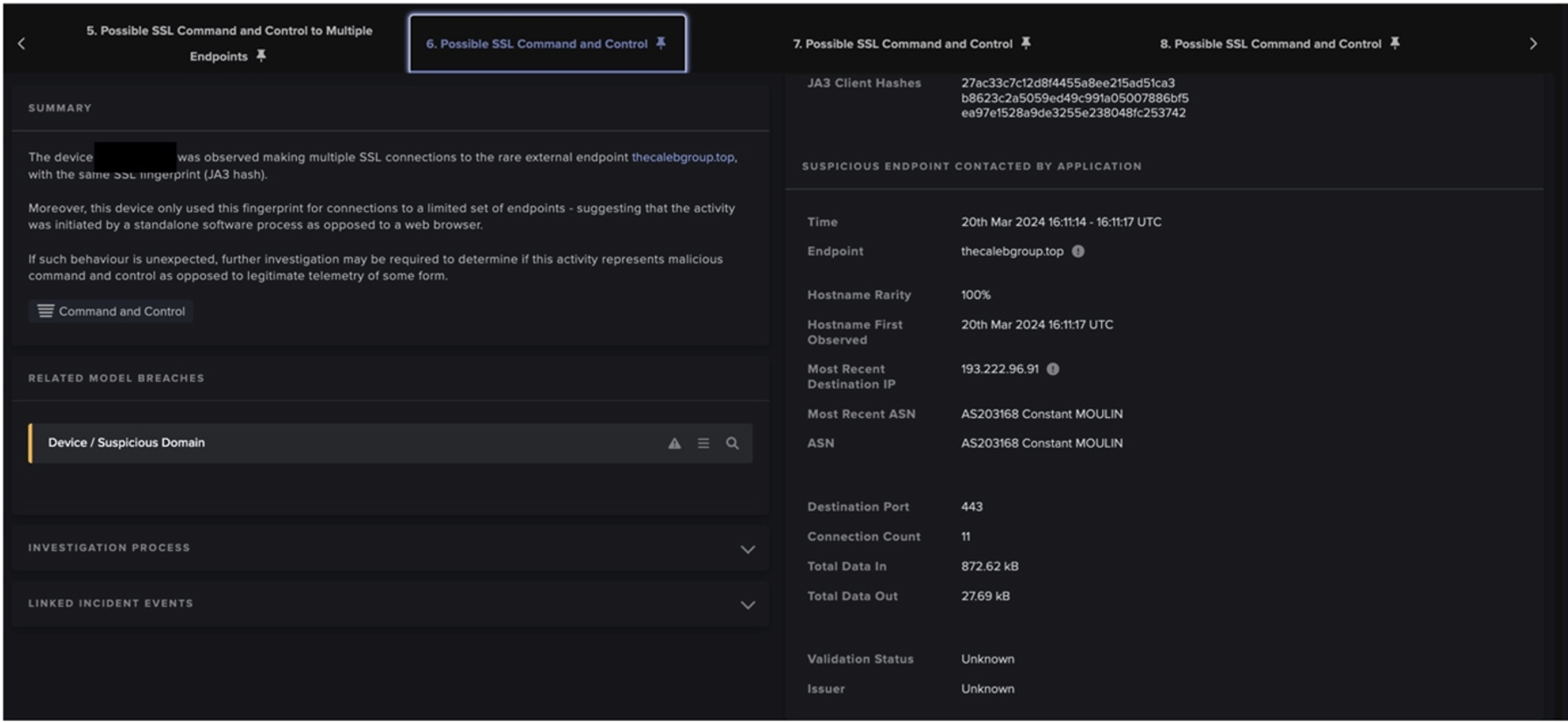
その直後、Cobalt Strike [9] に関連するエンドポイントに向けて、一連のC2ビーコンが発生しました。これには、svcctl、SecAddr、およびさらなるRPC接続に対するさまざまな異常なWMIバインド要求が伴っていました。これらにより、最初に感染したデバイスは、他の11台のデバイスに素早く感染することができました。翌日もスキャンを続けた結果、すぐに貴重なデータが確認されました。数回の転送を経て、230GBの内部データがSSHポート22を介して4つのファイルサーバーから流出しました。このデータは、SMB WritesとMoves/Renamesによって暗号化され、ランダムに生成される拡張子 .qHefKSmfd によって、組織で使用できないようにされました。最後に qHefKSmfd.README.txt と題した身代金要求のメモが投下されました。
この身代金要求書には、BlackMatterのアスキーロゴが添付されていました。

Darktrace DETECT と Cyber AI Analystがライブアラートを提供し続けましたが、脅威アクターは見事に任務を達成しました。
組織が脅威への対応を組織化できない理由は数多くあります(リソース不足、時間外の攻撃、単に動きが速すぎるグループなど)。DarktraceのRESPOND 機能が有効でなければ、脅威アクターはこの攻撃を何の障害もなく進めることができました。

RESPONDが導入されていた場合、攻撃はどのように展開されたか
Darktraceによる顧客独自のデジタル環境に対する「自己」の進化した知識で武装したRESPONDは、最初のネットワークスキャンから数秒以内に起動し、非常に異常であると認識されたことでしょう。ここで取られる標準的な行動は、通常通りビジネスを継続させながら異常をピンポイントで止めるために、侵害されたデバイスの標準的な「生活パターン」を一定期間にわたって強制的に実行することです。
RESPOND は、攻撃の展開に応じて常に脅威を再評価しています。RESPOND モデルでは、ポート 443 を介した C2 サーバーへの外部接続、外部への流出の試み、そして重要な点として暗号化に関連するポート 445 を介した SMB 書き込みアクティビティをブロックするよう警告が出されたことでしょう。
DETECT とRESPOND は互いに影響し合うので、Darktrace は BlackMatter が戦術を転換する際にその行動を評価し続けたことでしょう。これらの行動は、週末に稼働していない可能性のあるセキュリティチームのために重要な時間を取り戻し、解決するよりも多くの問題を引き起こす過度に攻撃的な対応をすることなく、攻撃者をその場に留まらせることができます。
最終的に、このインシデントは自律的に解決されませんでしたが、身代金事件を受けて、Darktrace は、RESPOND を有効にし、すべてのクライアントとサーバーデバイスのランサムウェア指標に対してアクティブモードに設定することを提案しました。これにより、このようなインシデントは二度と発生しないことが確認されました。
なぜRESPONDが効果的なのか
レスポンスソリューションは、真の脅威が存在する場合にのみ起動するような正確さ、ユーザー側が支配権を握れるような設定、そして通常の業務を妨げることなく悪意のある活動のみを抑制するための正しいアクションを知るためのインテリジェンスを備えていなければならないのです。
これは、ある組織にとっての「通常」が何であるかを確立している場合にのみ可能です。そして、これこそが、DarktraceのRESPOND 製品ファミリーが、ターゲットを絞って適切な行動を取ることを保証する方法なのです。ネットワーク、クラウド、SaaSにおける微妙な、あるいは大きな逸脱を強調するDETECT アラートを活用することで、RESPOND は潜在的な脅威に対して慎重な対応を行うことができます。これには、次のようなアクションが含まれます:
- デバイスの「生活パターン」を一定期間強制
- 「グループ生活パターン」の強制(過去に同種のデバイスが行っていないことをデバイスが行うことを阻止)
- 特定の宛先への特定の種類の接続をブロック
- クラウドアカウントからログアウト
- エンドポイントデバイスの「スマート検疫」- 組織のVPNとアンチウイルスソリューションへのアクセスを維持
結論
CISA は、BlackMatter に関する報告書 [10] の中で、異常な活動を調査する能力を備えたネットワーク監視ツールに投資することを組織に推奨しています。あらかじめ決められたルールやシグネチャではなく、通常とは異なる挙動を検知することは、新たな脅威に対抗する上で重要なステップとなります。しかし、この事例が示すように、検知するだけでは十分とは限りません。いつ、どこから脅威が侵入してきても、即座に的確な対処を行い、脅威を封じ込めるRESPOND をオンにすることが、スマッシュアンドグラブ攻撃に対抗し、組織のデジタル資産を保護する最善の方法です。BlackMatter の背後にいる脅威アクターが、新しい名前と戦略で戻ってくるか、すでに戻っていることは間違いありませんが、RESPOND を導入した組織は、それに対する準備ができているはずです。
付録
Darktrace モデル検知
PTN というプレフィックスが付いたものは、Darktraceの24/7のSOCチームに直接アラートされました。
- Device / ICMP Address Scan
- Device / Suspicious SMB Scanning Activity
- (PTN) Device / Suspicious Network Scan Activity
- Anomalous Connection / SMB Enumeration
- Device / Possible RPC Lateral Movement
- Device / Active Directory Reconnaissance
- Unusual Activity / Possible RPC Recon Activity
- Device / Possible SMB/NTLM Reconnaissance
- Compliance / Default Credential Usage
- Device / New or Unusual Remote Command Execution
- Anomalous Connection / New or Uncommon Service Control
- Device / New or Uncommon SMB Named Pipe
- Device / SMB Session Bruteforce
- Device / New or Uncommon WMI Activity
- (PTN) Device / Multiple Lateral Movement Model Breaches
- Compromise / Sustained SSL or HTTP Increase
- Compromise / SSL or HTTP Beacon
- Compromise / Sustained TCP Beaconing Activity To Rare Endpoint
- Device / Anomalous SMB Followed By Multiple Model Breaches
- Device / Anomalous RDP Followed By Multiple Model Breaches
- Anomalous Server Activity / Rare External from Server
- Anomalous Connection / Anomalous SSL without SNI to New External
- Anomalous Connection / Rare External SSL Self-Signed
- Device / Long Agent Connection to New Endpoint
- Compliance / SMB Drive Write
- Anomalous Connection / Unusual Admin SMB Session
- Anomalous Connection / High Volume of New or Uncommon Service Control
- Anomalous Connection / Unusual Admin RDP Session
- Device / Suspicious File Writes to Multiple Hidden SMB Shares
- Anomalous Connection / Multiple Connections to New External TCP Port
- Compliance / SSH to Rare External Destination
- Anomalous Connection / Uncommon 1 GiB Outbound
- Anomalous Connection / Data Sent to Rare Domain
- Anomalous Connection / Download and Upload
- (PTN) Unusual Activity / Enhanced Unusual External Data Transfer
- Anomalous File / Internal / Additional Extension Appended to SMB File
- (PTN) Compromise / Ransomware / Suspicious SMB Activity
IoC一覧

参考文献リスト
[2] https://cybernews.com/cyber-war/how-do-smash-and-grab-cyberattacks-help-ukraine-in-waging-war/
[5] https://techcrunch.com/2021/11/03/blackmatter-ransomware-shut-down/
[7] https://www.nytimes.com/2021/05/14/business/darkside-pipeline-hack.html
[8] https://techcrunch.com/2022/01/14/fsb-revil-ransomware/
[9] https://www.virustotal.com/gui/domain/georgiaonsale.com/community
[10] https://www.cisa.gov/uscert/ncas/alerts/aa21-291a
寄稿者:Andras Balogh(SOCアナリスト)、 Gabriel Few-Wiegratz(hreat Intelligenceコンテンツ制作リーダー)